Encryption choices in medical devices aren’t just about “which algorithm is strongest.” They’re about what you can support, validate, document, and maintain over a long product lifecycle—often across embedded platforms, cloud services, and hospital IT environments.
This post compares Twofish and Blowfish through a MedTech lens and gives practical guidance for teams dealing with legacy products, modernization, and FDA-facing evidence.
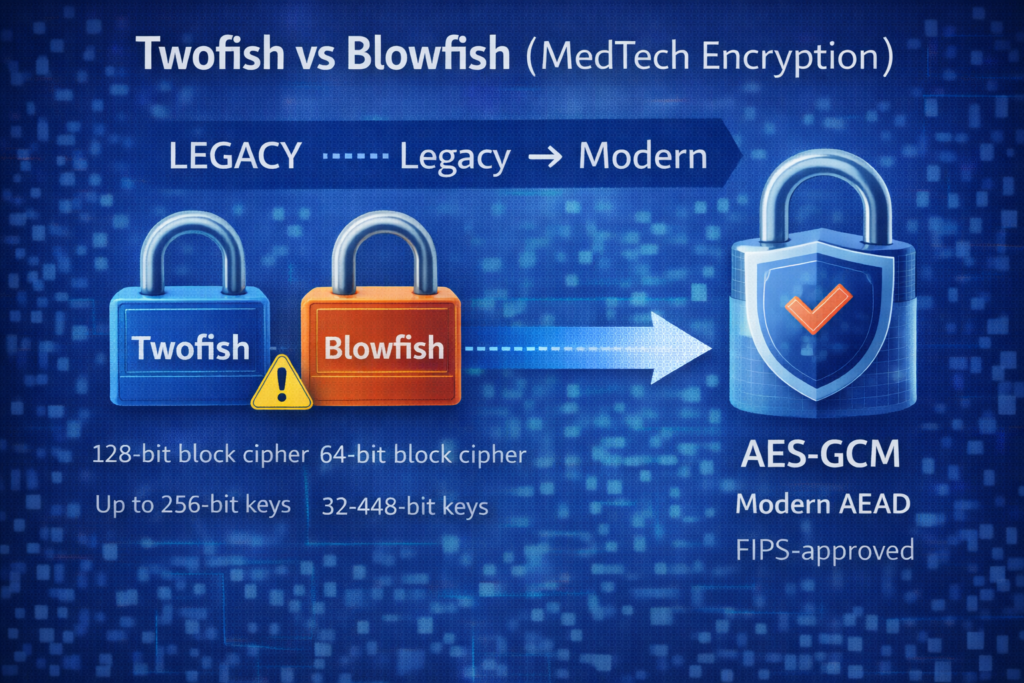
Quick Answer (If You’re Designing a New Medical Device Today)
- Default recommendation: use AES with an authenticated mode such as AES-GCM (or another modern AEAD scheme) for most new designs.
- Twofish: generally considered a solid cipher, but less common in modern standardized stacks and validated modules.
- Blowfish: avoid for new designs; its 64-bit block size creates scale-related risk (birthday/SWEET32-type concerns) and it’s largely a legacy choice.
If your device uses Twofish or Blowfish today, the key question is: what data volumes, what protocols, and what lifecycle plan are involved?
Why Medical Device Encryption Decisions Are Different
Medical device teams have extra constraints that typical IT apps don’t:
- Long lifecycles: devices may be deployed for years (or a decade+) with incremental updates.
- Mixed environments: home networks, hospital networks, gateways, cloud connectivity, service tooling.
- Validation burden: changes must be tested and documented; “crypto swaps” are rarely trivial.
- Regulatory expectations: you need a defensible security story with evidence, not just claims.
That’s why “which cipher wins” is the wrong framing. The better framing is: Which approach is standard, supportable, and defensible?
Twofish Overview (Where It Fits)
Twofish is a symmetric block cipher designed as an AES competition finalist. It uses a 128-bit block size and supports keys up to 256 bits.
Where Twofish can make sense in MedTech
- Legacy systems already using Twofish where the implementation is stable and well-tested
- Constrained environments where an existing library is deeply integrated
- Situations where you have strong key management and an overall modern design (e.g., authenticated encryption at the system level)
Twofish watch-outs
- Standardization and ecosystem support: Twofish is less common in modern “default stacks” than AES.
- Validation expectations: many organizations prefer FIPS-validated modules and NIST-approved algorithms for regulated environments.
Blowfish Overview (Why It’s Considered Legacy)
Blowfish is a classic symmetric block cipher that supports variable key lengths (up to 448 bits), but it uses a 64-bit block size. That 64-bit block size is the modern problem.
Why 64-bit block size matters
Even when a cipher’s core design remains strong, a short block size can create practical risk in some contexts as data volume grows (birthday-bound collision realities). The SWEET32 work made this especially well known for 64-bit block ciphers used with certain modes/protocols.
Where Blowfish might still be encountered
- Older medical devices and legacy file encryption implementations
- Older VPN/TLS-era configurations (less common now, but still seen in “long-lived” environments)
Blowfish watch-outs
- Avoid for new designs: the 64-bit block size is a long-term liability.
- Modern interoperability: many contemporary security baselines and libraries steer away from legacy 64-bit block ciphers.
So… Twofish vs Blowfish for Medical Devices?
If you have to choose between these two in a medical device context:
- Prefer Twofish over Blowfish when staying within a legacy design, because the 128-bit block size avoids the key scale-related issue inherent to 64-bit block ciphers.
- But for new systems: the more defensible, widely supported choice is usually AES with a modern authenticated mode (e.g., AES-GCM).
What Matters More Than the Cipher Name
In medical device cybersecurity, encryption failures usually happen because of implementation and operational issues—not because a team picked “the wrong cipher” in isolation. Focus on:
- Authenticated encryption: confidentiality + integrity (not just scrambling bytes)
- Key management: generation, storage, rotation, and access control
- Nonce/IV handling: avoid reuse and ensure correct usage per mode
- Secure updates: signed updates, protected keys, and repeatable verification
- Threat modeling: define what you’re protecting and from whom
Modernization Plan (If You Have Legacy Twofish/Blowfish)
If your device or ecosystem uses Twofish or Blowfish today, here’s a practical path that won’t create chaos:
- Inventory usage: where is the cipher used (data at rest, on-device comms, cloud, backups)?
- Estimate data volume and exposure: especially important for 64-bit block ciphers.
- Design a migration strategy: versioned formats, backwards compatibility, staged rollouts.
- Move toward modern baselines: AES + AEAD (commonly AES-GCM) and validated modules where needed.
- Document evidence: what changed, why, and how it was verified (test results, security rationale).
FAQs
Is Twofish still secure?
Twofish is widely regarded as a strong design and has been extensively studied. The bigger question for MedTech is whether it fits your validation, interoperability, and lifecycle support strategy.
Why is Blowfish discouraged for new designs?
Primarily because Blowfish uses a 64-bit block size, which can create scale-related risk in some real-world contexts. It’s generally considered a legacy choice when modern alternatives exist.
What should medical device manufacturers use instead?
For most modern designs, AES with an authenticated mode like AES-GCM is a common, defensible baseline, especially when paired with strong key management and a validated crypto module strategy.
Does FDA require a specific algorithm?
FDA’s cybersecurity guidance focuses on secure-by-design and providing documentation and evidence. In practice, using well-established, widely supported cryptography and being able to justify and verify your approach is the key.
External References (Trusted Resources)
- Twofish: A 128-Bit Block Cipher (Schneier et al.)
- The Blowfish Encryption Algorithm (Schneier)
- SWEET32: Birthday attacks on 64-bit block ciphers
- NIST FIPS 197: Advanced Encryption Standard (AES)
- NIST SP 800-38D: Recommendation for GCM (Authenticated Encryption)
- FDA: Cybersecurity in Medical Devices (Final Guidance)
How Blue Goat Cyber Helps
If you’re dealing with legacy encryption, planning a migration, or need a defensible cryptography story for premarket or postmarket needs, Blue Goat Cyber can help you document requirements, evaluate risk, and produce evidence that holds up in review.
- FDA Premarket Cybersecurity Services
- FDA-Compliant SBOM Services for MedTech
- Medical Device Threat Modeling
- Medical Device Vulnerability & Penetration Testing
- FDA Postmarket Cybersecurity Management
- Contact Blue Goat Cyber
Bottom line: Twofish vs Blowfish is mostly a legacy discussion. For new medical device designs, prioritize modern, widely supported, authenticated encryption baselines—and prove it with evidence.
