Published: February 9, 2024 · Last reviewed: May 1, 2026
Parameterized queries separate SQL code from user-controlled data, preventing the database from interpreting input as executable SQL commands. This mechanism directly mitigates SQL injection (CWE-89), a critical software weakness that, in medical devices, can lead to compromised data integrity, therapy delivery disruptions, or clinical workflow interruptions. Implementing parameterized queries is a foundational secure coding practice that aligns with an FDA-aligned secure product development lifecycle, providing defensible evidence of designing for security in premarket submissions as required by the February 3, 2026, final guidance.
Why SQL injection matters in medical device ecosystems
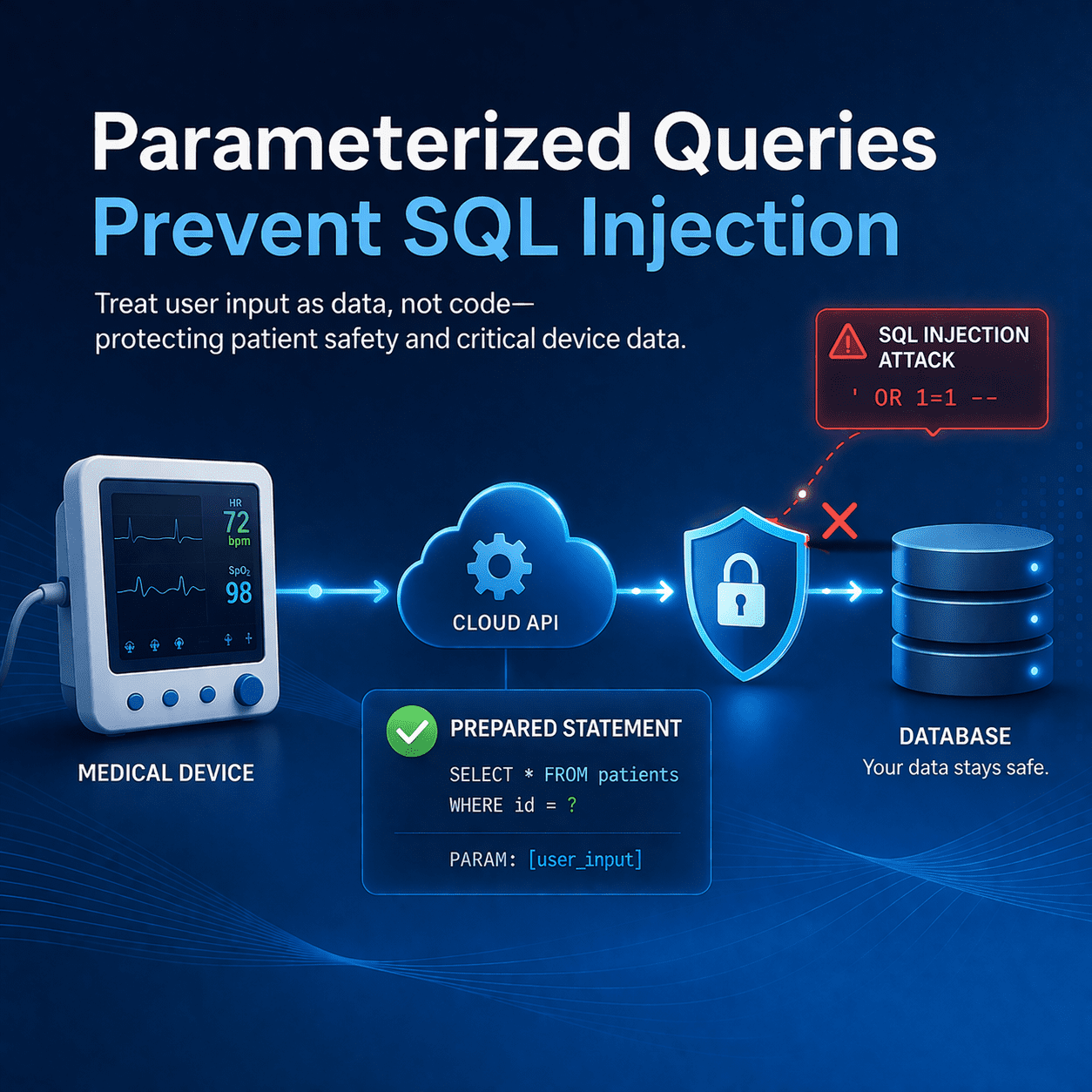
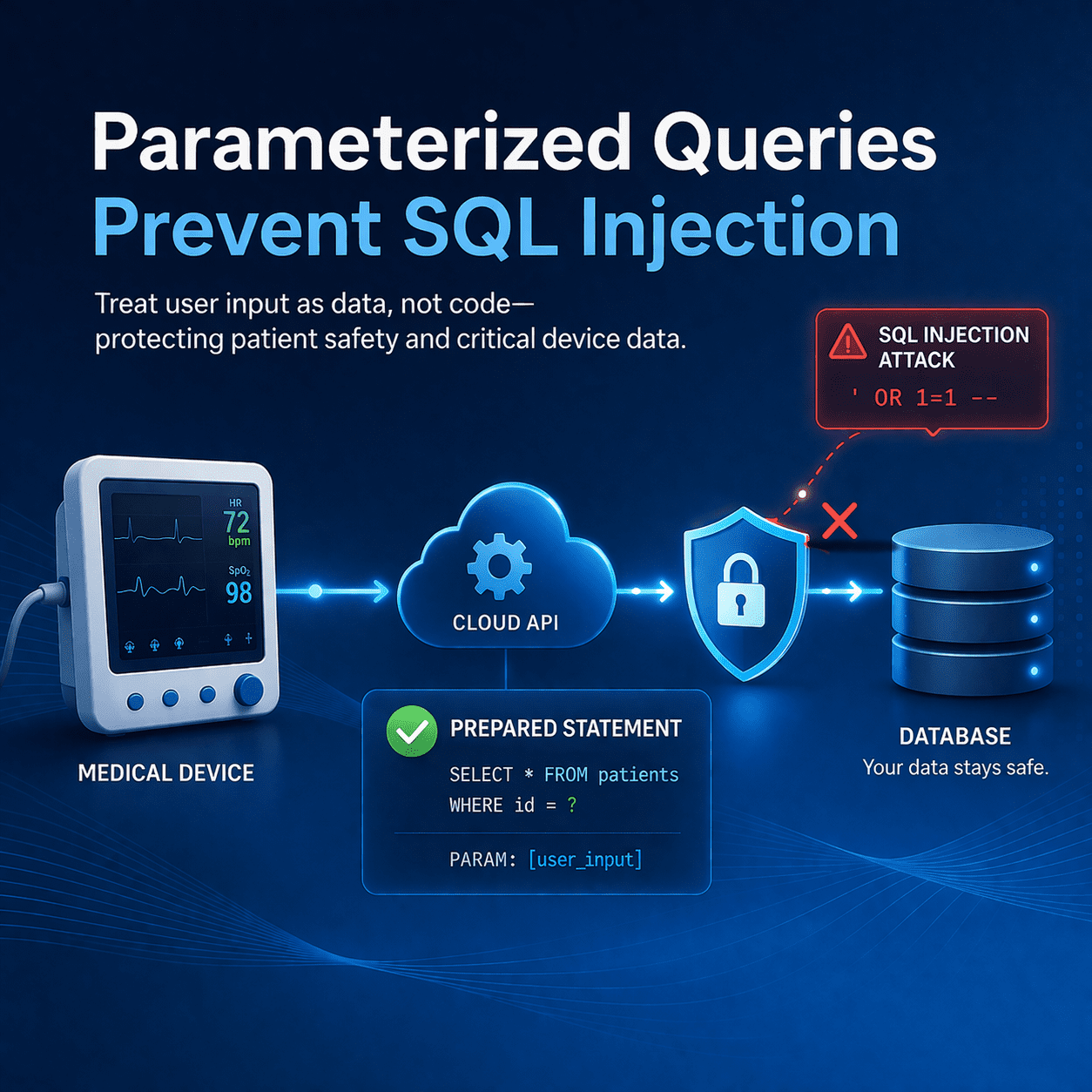
Modern devices rarely operate alone. Common architectures include:
- Device → cloud API → database (telemetry, configuration, analytics)
- Clinician web portal → backend services → database (patient lists, results review, alerts)
- Service/maintenance tools (field support apps, provisioning utilities)
In these systems, SQL injection can enable unauthorized data access, data manipulation, privilege escalation, or denial-of-service attacks. That can translate into clinical risk (delayed care, incorrect data presented to clinicians, disrupted connectivity) and regulatory friction if you can’t show secure coding practices and verification evidence.
If your product meets the definition of a “cyber device,” your premarket submission also needs to support the cybersecurity expectations tied to Section 524B (plans/procedures, reasonable assurance of cybersecurity, and SBOM). Parameterized queries are one concrete way to reduce risk in the “code, data, and execution integrity” category of controls-and to show you designed for security rather than patching after the fact.
What parameterized queries are (and why they work)
Parameterized queries separate SQL code from user-controlled data. Instead of building query strings by concatenating input, you define the SQL statement first and pass parameters separately. This keeps the database from interpreting input as executable SQL-so attackers can’t change the intent of the query.
In plain terms: parameterization makes the database treat input as values, not commands.
Quick example (conceptual)
Risky pattern (don’t do this):
query = "SELECT * FROM patients WHERE id = " + user_input
Safer pattern (do this):
query = "SELECT * FROM patients WHERE id = ?"
execute(query, [user_input])
Where parameterization fits in an FDA-aligned SPDF
Parameterized queries are strongest when they’re not “one-off developer hygiene,” but a documented, repeatable practice within your secure development process. Here’s how it maps cleanly into a practical SPDF:
- Threat modeling: identify injection abuse cases (e.g., login, search, reporting endpoints) and define controls.
- Security requirements: “All database access must use parameterized queries; no raw SQL concatenation.”
- Implementation standards: coding guidelines + code review checklist items.
- Verification: SAST rules + manual review + targeted DAST/pen testing for injection.
- Lifecycle: keep the control effective as features evolve (new endpoints, new queries, new third-party components).
If you’re building your FDA-ready cybersecurity package, parameterized queries are also easy to cite as a specific control when documenting how your software reduces realistic threats and prevents common vulnerability classes.
Implementation patterns that actually hold up in reviews
1) Parameterize everything (not just login)
SQL injection shows up in the “boring” places: search filters, sort options, report builders, export functions, admin tooling, and device provisioning workflows. Make parameterization a default requirement across all services.
2) Be careful with “dynamic” query parts
Parameterization works for values, but not for dynamic SQL keywords (e.g., column names in ORDER BY). For those cases:
- Use allowlists (only permit known-safe column names or sort options)
- Use query builders/ORM safely (avoid raw query escape hatches)
- Never pass user input into SQL structure (table names, operators, joins) without strict allowlisting
3) Don’t confuse “stored procedures” with “safe”
Stored procedures can be safe if they use bind variables properly. They can also be vulnerable if they build dynamic SQL internally. Treat them the same way you treat application code: enforce parameterization and review.
4) Use least-privilege database accounts
Even perfect parameterization doesn’t justify overly powerful DB credentials. Use separate accounts/roles for read vs write and keep permissions tight. This limits blast radius if another control fails.
5) Log and monitor injection attempts
At minimum, log authentication failures, suspicious query patterns, and repeated input validation failures at the application layer (without logging secrets/PHI). This supports postmarket monitoring and incident response readiness.
How to prove it: testing and evidence you can reuse in submissions
Parameterized queries are a control. FDA reviewers (and your internal stakeholders) will care about evidence that the control is implemented and verified. A practical evidence set includes:
- Threat model showing injection threats and mitigations
- Secure coding standard requiring parameterized queries
- Code review checklist item: “No string-concatenated SQL”
- SAST results (rules targeting injection + manual review notes)
- DAST / penetration test results showing injection testing on key endpoints
- Risk file linkage mapping injection threats → controls → verification → residual risk
If you want a faster path to this documentation set, see our guidance breakdown of what typically belongs in an eSTAR-ready premarket package, plus common gaps that trigger questions.
FDA Medical Device Cybersecurity 2026: 524B eSTAR Checklist
Common MedTech pitfalls (even on “mature” teams)
- ORM “raw query” shortcuts introduced under deadline pressure
- Dynamic report builders that allow unsafe query structure
- Admin tools that skip the same controls used in production services
- Over-privileged service accounts that amplify impact
- Security testing that’s too generic (not targeting your real injection surfaces)
Key Takeaways
- Parameterized queries are a baseline control for preventing SQL injection (CWE-89).
- Use them everywhere-not just login screens.
- Handle dynamic SQL safely with allowlists and safe query builders.
- Pair implementation with evidence: threat modeling + SAST + pen testing + traceability.
- Make it part of your SPDF so it scales and survives design changes.
FAQs
Are parameterized queries enough to stop SQL injection?
They are the most reliable primary control, but they should be paired with defense-in-depth (least privilege, input validation for expected formats, logging/monitoring, and security testing).
Do ORMs automatically prevent SQL injection?
Often-but not always. ORMs can be bypassed through raw queries, dynamic filters, and unsafe extensions. Treat “no raw concatenated SQL” as a hard rule regardless of ORM usage.
Can stored procedures replace parameterized queries?
Only if the stored procedure uses safe parameter binding and does not build dynamic SQL from user input. Stored procedures can still be vulnerable if implemented incorrectly.
What should we include in a premarket submission related to SQL injection prevention?
At minimum: threat model coverage of injection, documented secure coding requirements, verification evidence (SAST + targeted DAST/pen test), and traceability into your risk management file.
How do we test for SQL injection in medical device web portals and APIs?
Use a mix of SAST (code-level checks), manual review for dangerous patterns, and DAST/penetration testing focused on your real inputs (filters, search, exports, admin features, device provisioning endpoints).
Conclusion
SQL injection prevention is one of the simplest “high ROI” wins in medical device software security. Parameterized queries reduce a common, high-impact vulnerability class, and they produce clean, defensible evidence when you’re building an FDA-ready cybersecurity story.
Book a Discovery Session
If you want help turning secure coding controls (like parameterized queries) into submission-ready evidence-threat modeling, SAST, penetration testing, and documentation-we can help.
Related: Medhacking and Medjacking