Published: March 1, 2024 · Last reviewed: May 1, 2026
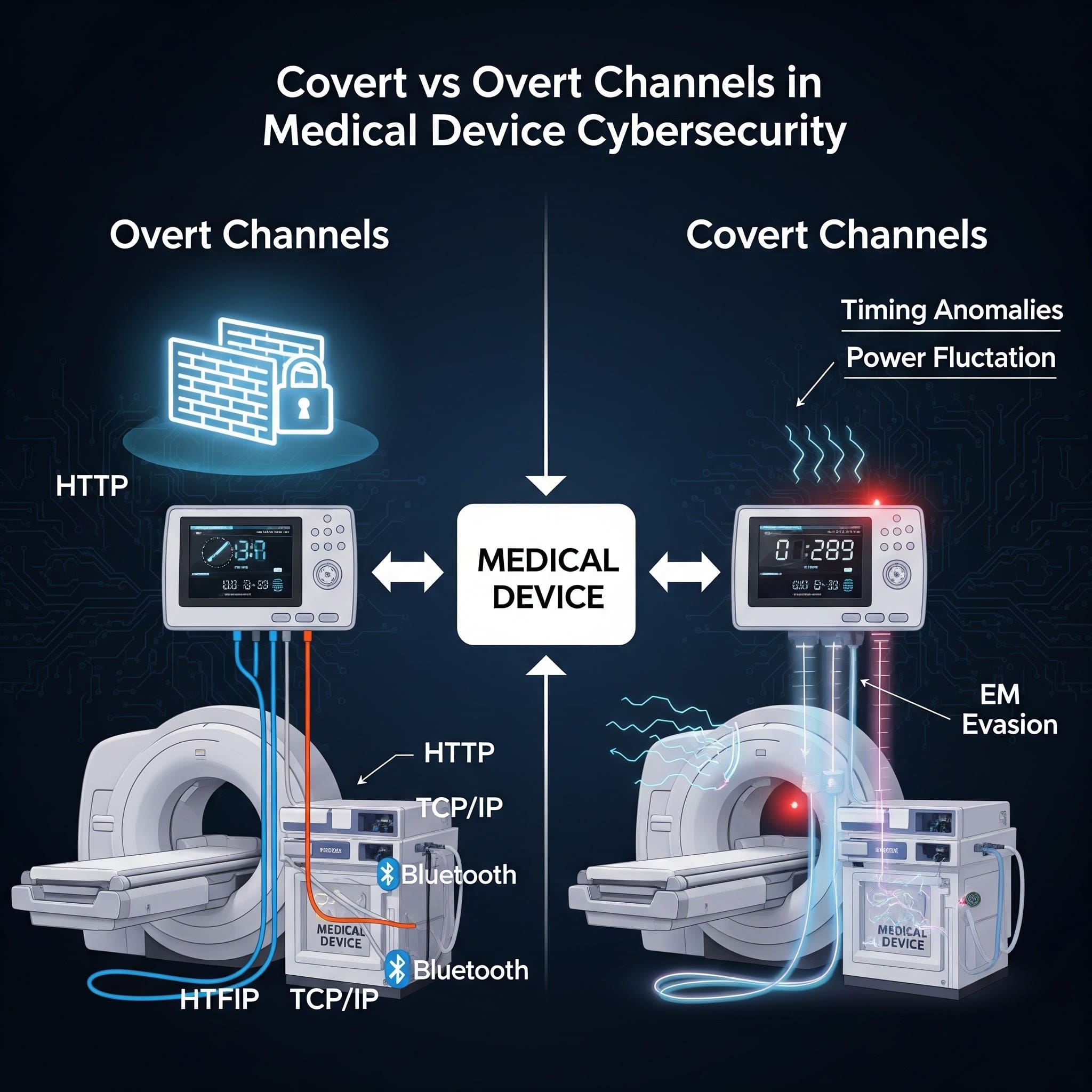
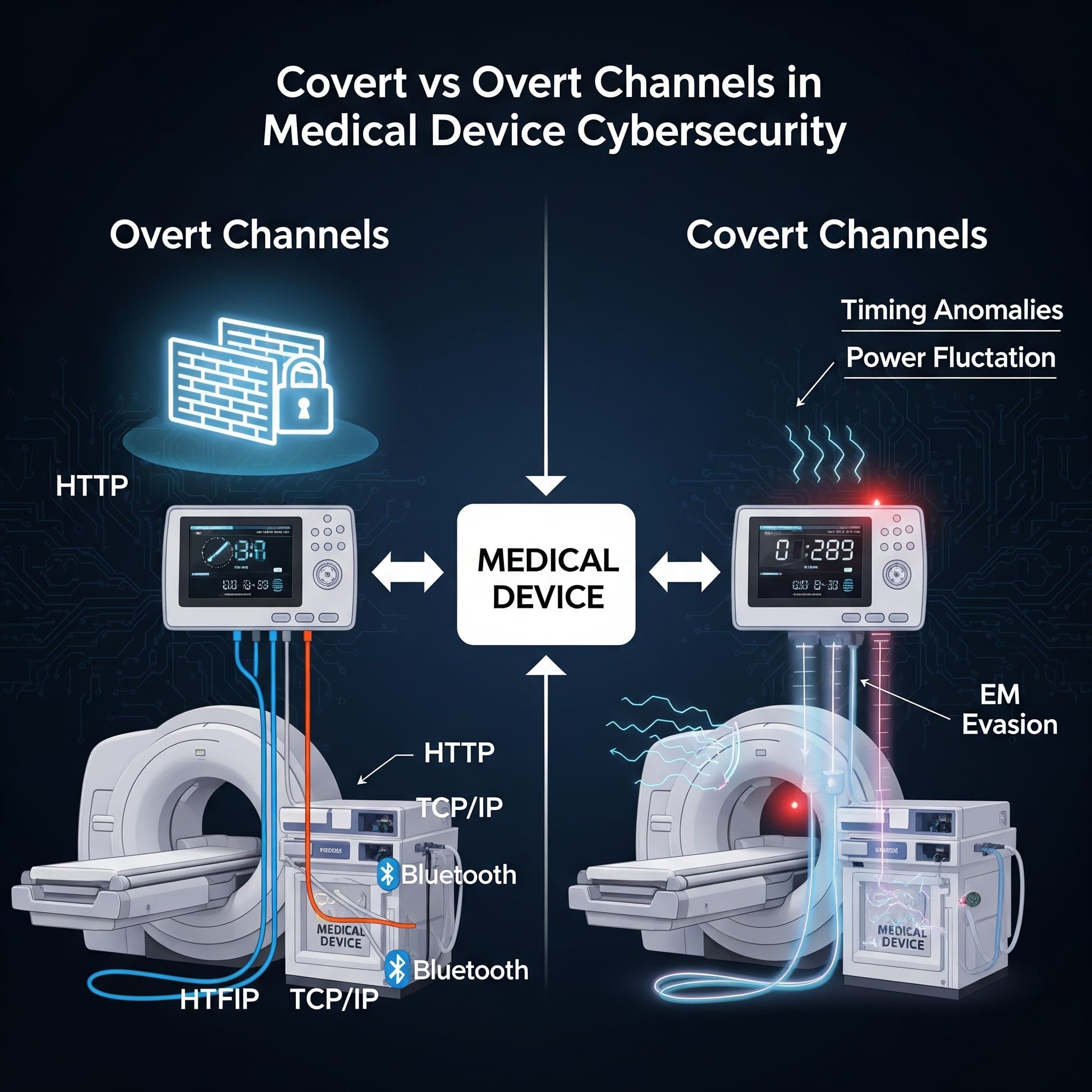
Connected medical devices depend on legitimate communication paths-telemetry, updates, remote support, integrations with hospital systems. Those intended paths are overt channels.
The problem is that attackers don’t need your “intended” path. They look for ways to move data or commands through mechanisms your system wasn’t designed to use for communication. Those unintended paths are covert channels.
If you build cybersecurity evidence for FDA submissions or operate a postmarket program, this distinction matters because covert channels often show up as: “unexpected outbound traffic,” “unexplained data movement,” or “we can’t prove what left the device.”
At a glance
| Dimension | Overt Channels | Covert Channels | | :--- | :--- | :--- | | Definition | Explicit, documented communication paths designed for data transfer. | Hidden paths using unintended mechanisms to bypass security. | | Use Case | Routine telemetry, software updates, and EMR integrations. | Data exfiltration, command-and-control, or side-channel signaling. | | Visibility | Monitored via standard system logs and network dashboards. | Invisible to standard logging; requires anomalies or deep inspection. | | Security Posture | Protected by TLS, firewalls, MFA, and access controls. | Exploits physical characteristics (timing/power) or protocol headers. | | Common Attacks | Man-in-the-Middle, credential theft, or API exploits. | Protocol tunneling, steganography, or clock skew modulation. | | FDA Relevance | Subject to standard Premarket Cybersecurity controls (Section 524B). | Evaluated under forensic analysis and threat modeling (STRIDE/CAPEC). | | Key Tradeoff | Ease of management vs. target for direct attack. | High complexity to implement vs. high stealth for attackers. |
Definitions (plain language)
What is an overt channel?
An overt channel is a legitimate, intended communication path-designed to transmit information and typically protected by standard controls (authentication, authorization, encryption, logging). Examples include HTTPS to a cloud endpoint, an authenticated API call to an on-prem server, or a documented HL7/FHIR integration path.
What is a covert channel?
A covert channel is an unintended method of communication that can transfer information in a way that violates policy or bypasses controls. NIST describes covert channels as a way to communicate information using a mechanism not intended for information transfer. NIST glossary: covert channel
In practical terms: covert channels are how data exfiltration and command-and-control (C2) can hide inside “normal-looking” activity-especially if you don’t have strong egress controls and monitoring.
Why this matters for medical device manufacturers
Medical devices live in constrained, high-complexity environments: segmented hospital networks, vendor gateways, shared infrastructure, and long-lived products with legacy dependencies.
That combination creates a familiar pattern:
- You design and document overt channels (what the device is supposed to do).
- Attackers exploit weaknesses to create covert channels (what the device can be made to do).
FDA’s premarket cybersecurity expectations focus heavily on having a secure product development process, clear architecture and data flows, and lifecycle risk management-exactly the areas where covert channels should be analyzed and controlled. FDA cybersecurity premarket guidance (current)
If you want help making this “submission-ready,” start with medical device threat modeling and an evidence-driven FDA premarket cybersecurity package.
Types of covert channels: timing vs storage
Security engineering typically groups covert channels into two buckets:
Timing channels
A timing channel transmits data by modulating time-based behavior-delays, jitter, response timing, packet timing, CPU scheduling patterns. In MedTech, timing channels can become realistic when devices share CPU resources, buses, or network links (for example, multi-process systems, gateways, or virtualized components).
Storage channels
A storage channel transmits data by writing it somewhere it “shouldn’t” be used for communication-unused header fields, metadata, shared memory, log fields, caches, file attributes, or even LED/blinker patterns in extreme cases.
Real-world examples in medical device environments
1) DNS tunneling through “allowed” infrastructure
Hospitals often permit DNS. Attackers can abuse DNS as a covert channel by encoding data in queries or responses. If your device or supporting gateway can reach external DNS resolvers, DNS tunneling becomes a plausible exfiltration path.
2) “Overt” web traffic used for covert exfiltration
HTTPS (443) is an overt channel-until it’s used to move unexpected payloads to an unapproved destination. Without destination allowlisting, certificate controls, and monitoring, outbound HTTPS can become the easiest covert channel to operate.
3) Debug and maintenance interfaces as covert paths
Serial consoles, hidden service ports, maintenance shells, and test hooks are common in device development. If not controlled or removed, they can become covert channels-especially when combined with physical access in clinical environments.
4) Rogue implants and “quiet network neighbors”
Sometimes the covert channel isn’t inside the device-it’s attached to the environment. A small Ethernet implant (“LAN turtle” style) can create an unauthorized bridge for data movement and remote access. See our related post: Covert channels from rogue Ethernet implants (MedTech defenses).
How to address covert channels in an FDA-aligned way
You don’t “eliminate covert channels” with a single control. You reduce likelihood and impact through layered design and operational controls that also produce strong documentation.
1) Start with data flows and trust boundaries
- List approved communications (destinations, protocols, ports, auth methods).
- Define trust boundaries (device ↔ hospital network ↔ cloud ↔ service tools).
- Identify where data could cross a boundary unintentionally (logs, telemetry, DNS, debug).
2) Egress control: the highest ROI control for covert channels
- Allowlist destinations (FQDN/IP) and required ports for device outbound traffic.
- Block direct-to-Internet traffic where possible; use controlled proxies/gateways.
- Enforce TLS certificate validation and consider mTLS for high-value services.
3) Monitoring that catches covert behavior
- Baseline expected destinations and connection frequency.
- Alert on new domains/IPs, unusual DNS query volume, and abnormal payload sizes.
- Log security-relevant events in a way your postmarket team can actually use.
4) Reduce “unintended communication surfaces”
- Disable/remove debug ports and test services in production builds.
- Harden configuration: least privilege, no default credentials, secure secrets handling.
- Validate third-party components and dependencies (this is where an SBOM helps).
Need help operationalizing this across submissions and postmarket? See FDA postmarket cybersecurity services and FDA-compliant SBOM services for MedTech.
Key takeaways
- Overt channels are intended communication paths; covert channels are unintended paths used to bypass policy or controls.
- In MedTech, covert channels often appear as “unexpected outbound traffic,” DNS abuse, misuse of HTTPS, or leftover debug/maintenance interfaces.
- Best defenses are layered: strong data-flow documentation, egress allowlisting, monitoring, and removal of unnecessary services.
- Addressing covert channels cleanly supports FDA-aligned evidence: architecture, threat modeling, and lifecycle risk management.
FAQs
What is the difference between covert and overt channels?
Overt channels are intended, documented communication paths (e.g., HTTPS telemetry to a cloud endpoint). Covert channels are unintended paths used to transfer information in ways that bypass policy or controls.
What are examples of covert channels?
Common examples include timing channels (modulating response timing or packet timing) and storage channels (hiding data in metadata, unused header fields, logs, shared memory, or unexpected file locations).
Is DNS tunneling a covert channel?
Yes. DNS is a normal (overt) service, but encoding data inside DNS queries/responses creates a covert channel for exfiltration or C2-especially if outbound DNS is not controlled and monitored.
How do covert channels show up in medical device penetration testing?
Testers often find them indirectly: unexpected listening services, unrestricted egress, weak certificate validation, insecure remote support paths, or hidden debug interfaces that allow data movement or remote control.
How should we address covert channels for FDA submissions?
Document approved data flows and trust boundaries, identify misuse cases in threat modeling, and provide evidence of controls-especially egress allowlisting, authentication/encryption, and monitoring/logging aligned to your secure product development process.
Can an overt channel become a covert channel?
Yes. If a legitimate channel (like HTTPS) is not constrained to approved destinations and monitored, attackers can use it to move unauthorized data-turning an overt channel into a covert path.
Conclusion
Overt channels keep your product working. Covert channels are how attackers make it misbehave-quietly. The best medical device cybersecurity programs treat covert-channel risk as a design input: define data flows, constrain egress, remove unnecessary surfaces, and monitor what’s leaving your ecosystem.
Book a Discovery Session
If you want help turning threat modeling and network controls into credible, FDA-aligned cybersecurity evidence-while strengthening postmarket readiness-let’s talk.
Sources & references
Primary sources cited in this article. Links open in a new tab.