If you are preparing a 510(k), De Novo, or PMA, picking the right cybersecurity partner can save you a lot of rework. The wrong partner can leave you with reports that look fine on paper but do not map cleanly to what FDA reviewers want to see.
This guide is not a vendor ranking. Instead, it gives you a practical way to evaluate firms and a set of questions you can copy and paste into your next vendor call.
Start with what the FDA actually expects
FDA’s current premarket cybersecurity guidance (issued February 2026) focuses on three big ideas:
- Cybersecurity is part of safety, and it belongs in your quality system and design controls.
- Secure product development matters. The FDA describes a Secure Product Development Framework (SPDF) as one way to reduce vulnerabilities across the product lifecycle.
- Submission documentation must tell a complete story, including architecture, threat modeling, testing, transparency, and lifecycle plans.
FDA reference: Cybersecurity in Medical Devices: Quality Management System Considerations and Content of Premarket Submissions (Feb 3, 2026)
eSTAR is not optional for most teams
In practice, your vendor needs to deliver work that aligns with how the FDA receives submissions. FDA’s eSTAR program page states that eSTAR is required for all 510(k) and De Novo submissions, unless exempted.
FDA reference: eSTAR Program
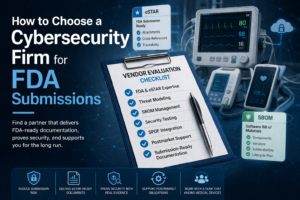
What an FDA-ready cybersecurity partner should be able to deliver
The exact scope depends on your device, intended use, and risk, but a firm that is ready for FDA work should be comfortable producing and packaging these items:
- Architecture and system description (components, interfaces, trust boundaries, data flows, external dependencies).
- Threat model tied to realistic attack paths and patient or clinical impact, not just generic IT threats.
- Cybersecurity risk management evidence with traceability from threats to requirements, controls, and verification results.
- SBOM plus a plan to keep it current after release.
- Security controls and rationale (what you implemented and why it is appropriate for the device and environment).
- Security testing evidence that matches your actual attack surface (for example, static analysis, dynamic analysis, fuzzing where appropriate, penetration testing).
- Update and patching approach, including how updates are secured and how you avoid breaking safety or performance.
- Vulnerability management and coordinated disclosure procedures that continue after clearance.
- Cybersecurity labeling and user guidance so hospitals and users can deploy the device safely.
If you want a simple way to organize the artifact set internally, here is a Blue Goat reference that breaks the typical package into 18 deliverables: Navigating the FDA’s 18 Cybersecurity Deliverables
Section 524B and “cyber devices” (what to confirm early)
FDA explains that FDORA added Section 524B to the FD&C Act and that it applies to “cyber devices.” If your device meets that definition, your submission needs to include specific cybersecurity information.
How to choose a cybersecurity firm for FDA submissions
1) Make sure they do medical device work, not just “enterprise security”
Ask how they handle patient impact, clinical workflows, and device system interactions (device, app, cloud, update infrastructure). If they only talk in SOC 2 language or web app templates, that is a warning sign.
2) Ask for eSTAR-ready outputs, not just reports
Good partners plan for packaging: version control, consistent terminology across artifacts, and clear cross references so a reviewer can follow the chain from threat model to test evidence without guessing.
3) Look for SPDF evidence, not SPDF buzzwords
The FDA expects cybersecurity to be built into development. A strong partner can help you show how your secure development practices work in reality (requirements, reviews, testing, release controls, and postmarket monitoring), not just in a slide deck.
4) Confirm testing is scoped to your real attack surface
Pen testing should reflect the device architecture (radio protocols, update mechanism, APIs, mobile app, cloud services, and the use environment). One generic pen test package does not fit every device.
5) Do they stay with you after clearance?
Cybersecurity obligations continue after the device ships. Ask what they provide postmarket: vulnerability intake and triage, SBOM monitoring, patch documentation support, and coordinated disclosure help.
Vendor interview questions
- FDA fit: Which submission types do you support (510(k), De Novo, PMA)? What exactly do you deliver (artifacts, testing, eSTAR packaging, deficiency support)?
- eSTAR packaging: Do you deliver eSTAR-ready attachments and cross references, or does our team reformat everything?
- Threat modeling: How do you tie threats to patient impact and realistic clinical use?
- SBOM: Which formats do you support, and how do you help keep the SBOM current after release?
- Testing: What testing methods are included, and what drives scope (interfaces, architecture, risk, environment)?
- Traceability: How do you link threats to requirements, controls, and verification evidence?
- Unresolved anomalies: How do you document and justify security anomalies at submission time?
- Deficiency response: If the FDA asks questions, how do you support the response and what does that support include?
- Postmarket: What do you provide after clearance (intake, triage, patching support, disclosure coordination)?
Red flags that usually mean “keep looking”
- They cannot explain how cybersecurity ties into safety risk management and design controls.
- They only offer a generic template pen test and cannot tailor the scope to your interfaces and update path.
- They do not talk about traceability or how artifacts fit into eSTAR.
- They treat SBOMs as one-time exports rather than lifecycle items.
- They have no plan for postmarket vulnerability handling.
Plan for QMSR realities
FDA’s Quality Management System Regulation (QMSR) became effective on February 2, 2026. If your cybersecurity story is disconnected from your quality system, it tends to show up as gaps in documentation and weak traceability.
FDA reference: Quality Management System Regulation (QMSR)
Where Blue Goat Cyber fits
If you want a partner that focuses specifically on FDA-facing medical device cybersecurity, Blue Goat Cyber supports premarket documentation, threat modeling, SBOM work, penetration testing, and postmarket vulnerability management.
- FDA Premarket Cybersecurity Services
- FDA-Compliant SBOM Services
- Medical Device Penetration Testing
- FDA Postmarket Cybersecurity Services
Key takeaways
- Pick vendors based on FDA-ready deliverables and traceability, not brand recognition.
- Make eSTAR packaging a requirement so your regulatory team is not stuck reformatting work.
- Threat modeling should reflect patient impact and real architecture, not generic checklists.
- SBOM and vulnerability management are lifecycle work, not submission-only artifacts.
- Engage early so cybersecurity evidence is built during development, not reconstructed at the end.
FAQs
What is the best cybersecurity firm for FDA medical device submissions?
The best firm is the one that can deliver FDA-appropriate artifacts (architecture, threat model, SBOM, risk management evidence, testing evidence, labeling support) and package them into a clean eSTAR-ready submission set, while also supporting postmarket vulnerability handling.
Is eSTAR required for 510(k) and De Novo submissions?
FDA states eSTAR is required for all 510(k) and De Novo submissions, unless exempted. Confirm your submission type and any exemption conditions with your regulatory lead.
Do we need an SBOM for FDA submissions?
FDA’s cybersecurity guidance discusses SBOM as part of the recommended documentation for devices with cybersecurity risk, and Section 524B also addresses cybersecurity information for cyber devices. Practically, reviewers expect a clear component inventory plus a plan to maintain it after release.
Is a penetration test enough to satisfy FDA cybersecurity expectations?
No. Testing is important, but the FDA also expects secure development practices (SPDF), clear architecture and threat modeling, risk management evidence, and lifecycle plans for monitoring and remediation.
Call to action
Want to reduce submission risk and get an FDA-ready cybersecurity package?
