What Is a Radiology Information System (RIS)? RIS Meaning, How It Works, and Cybersecurity Best Practices
RIS stands for Radiology Information System (RIS). RIS software helps imaging departments manage orders, scheduling, workflow, reporting, and operational tasks—while integrating with other systems and devices across the radiology ecosystem.
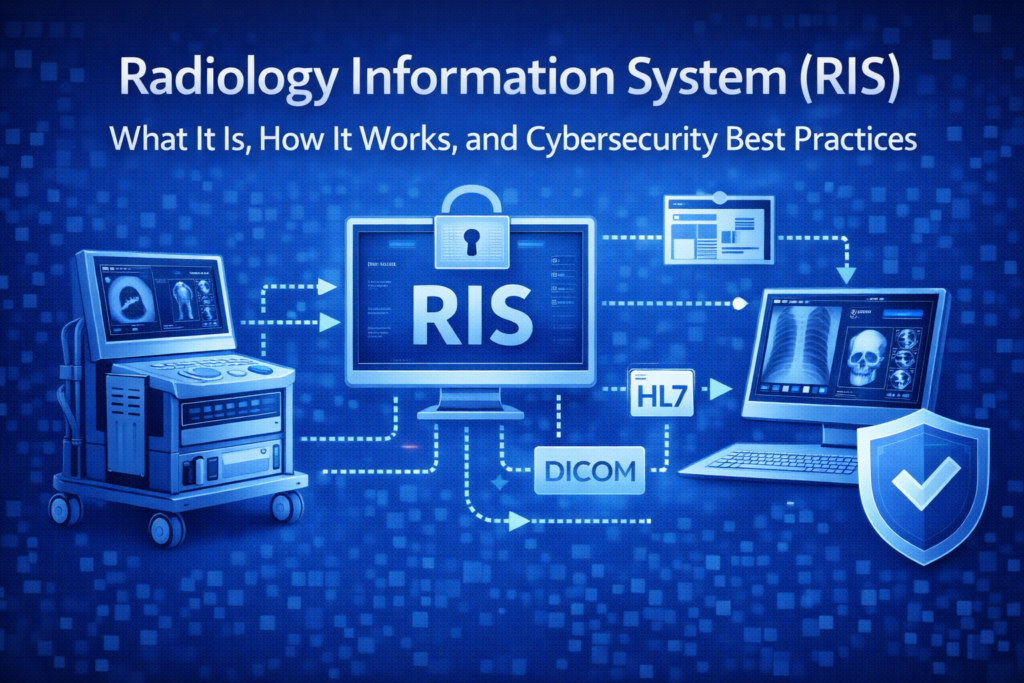
Because a RIS sits at the intersection of patient data, clinical workflow, and interoperability, it’s also a high-value target. This guide explains what a RIS is, how RIS–PACS–EHR integration typically works, and practical cybersecurity controls that reduce real-world risk.
RIS Meaning: What Does a Radiology Information System Do?
A Radiology Information System (RIS) is specialized software that supports imaging operations. Depending on the organization and vendor, a RIS commonly supports:
- Order and exam workflow (tracking studies from request to completion)
- Scheduling (appointments, resources, modality coordination)
- Reporting support (radiologist workflow, report distribution)
- Operational and administrative data (worklists, status, analytics)
- Billing/revenue workflow support (often integrated—varies by environment)
In plain terms: if PACS is where images live, RIS is where imaging operations are organized.
RIS vs PACS vs EHR: What’s the Difference?
These systems work together, but they serve different purposes:
| System | Primary Purpose | Typical Data |
|---|---|---|
| Radiology Information System (RIS) | Radiology workflow and departmental operations | Orders, scheduling, exam status, reporting workflow, operational metadata |
| Picture Archiving and Communication System (PACS) | Imaging storage, retrieval, and distribution | Images, studies/series, imaging metadata, viewer access |
| Electronic Health Record (EHR) / Hospital Information System (HIS) | Enterprise patient record and clinical operations | Patient demographics, clinical documentation, orders, results, billing context |
Integration improves efficiency and reduces manual entry—but it also expands the attack surface if security controls aren’t designed in.
How RIS Software Works in a Typical Imaging Workflow
- Order placed: An imaging order is created from the EHR/HIS or ordering system.
- Scheduling: The RIS schedules the exam (time, modality, location) and tracks status.
- Acquisition support: Modality worklists and imaging workflows reduce manual data entry and mismatches.
- Interpretation and reporting: Radiologists interpret studies; reports flow back to downstream systems.
- Operational closure: Completion, analytics, and (often) billing workflow follow.
RIS–PACS Integration: HL7, DICOM, and Why Interfaces Create Risk
RIS value comes from interoperability. In many deployments, workflows are orchestrated using:
- Health Level Seven (HL7) (commonly HL7 v2) for registration, orders, and results.
- Digital Imaging and Communications in Medicine (DICOM) for imaging workflows and imaging metadata exchange.
- Integrating the Healthcare Enterprise (IHE) profiles (often Scheduled Workflow) that standardize how systems coordinate and reduce mismatches.
Connectivity is a benefit—and a risk multiplier. Each interface, integration engine, and trusted connection becomes a place where weak authentication, poor segmentation, misconfiguration, or unvalidated inputs can create a real incident.
RIS Cybersecurity: Why It Matters in Healthcare and MedTech
RIS environments commonly handle or connect to systems that handle electronic protected health information (ePHI) and support critical imaging workflows. A compromise can affect:
- Confidentiality: patient data exposure
- Integrity: wrong-patient/wrong-study associations or altered workflow data
- Availability: disruptions to scheduling, reporting, and imaging operations (a major ransomware impact area)
For medical device manufacturers, RIS is also part of the broader connected ecosystem—where devices, networks, software, and services influence risk and patient safety outcomes.
Common RIS Security Risks and Failure Modes
- Interface exposure: HL7 interfaces and integration engines are high-value targets when access controls and monitoring are weak.
- Identity and access weaknesses: shared accounts, weak passwords, over-permissioned roles, stale vendor access.
- Legacy dependencies: older operating systems, unpatched third-party components, unsupported libraries.
- Flat networks: minimal segmentation enables lateral movement from one compromise to many systems.
- Data integrity risk: workflow mismatches can become clinical risk (not just an IT problem).
- Third-party connectivity: remote support paths and vendor integrations expand the trust boundary.
RIS Cybersecurity Best Practices That Actually Help
1) Treat RIS as a critical clinical workflow system
Apply the same rigor you would to other mission-critical clinical systems: hardening standards, change control, monitoring, and tested recovery procedures.
2) Strong access control and auditability
- unique user IDs (avoid shared logins)
- role-based access control (least privilege)
- multi-factor authentication (MFA) wherever feasible (especially admin and remote access)
- audit logs for high-risk actions (user admin, interface configuration, report edits)
3) Segmentation to reduce blast radius
Segment RIS, PACS, modality networks, and general IT, where possible. Restrict inbound/outbound traffic to what is required and alert on unusual connections.
4) Secure HL7 and interface engines
- authenticate and tightly control interface endpoints
- validate message formats and reject unexpected inputs
- monitor message failures, spikes, and unexpected routing changes
- document source-of-truth systems to prevent silent integrity drift
5) Patch and lifecycle management (including third-party components)
Maintain an inventory of RIS components, versions, and dependencies. Track vulnerabilities and define remediation SLAs—especially for internet-exposed services or remote access paths.
6) Resilience: backup and downtime planning for radiology operations
- backups that are protected from ransomware and tested for restore
- downtime workflows for scheduling/reporting continuity
- tabletop exercises that include imaging operations
- clear vendor coordination for support and recovery
Quick Checklist: Is Our RIS Environment Defensible?
- We can list every RIS/PACS/interface component, version, and owner.
- Admin access is MFA-protected and fully logged.
- RIS/PACS/modalities are segmented from general IT and tightly routed.
- Interface engines are monitored for anomalies, failures, and configuration changes.
- Backups are protected, tested, and recovery objectives are defined.
- We have a vulnerability intake and patch process that includes vendors and third parties.
FAQs
What does RIS stand for in radiology?
RIS stands for Radiology Information System—software that manages radiology workflow such as scheduling, orders, reporting operations, and departmental coordination.
What is the difference between RIS and PACS?
RIS focuses on workflow and operational coordination, while Picture Archiving and Communication System (PACS) focuses on imaging storage, retrieval, and distribution. They are commonly integrated.
How does RIS integrate with PACS and the EHR?
Integration commonly uses Health Level Seven (HL7) messaging for orders/results and Digital Imaging and Communications in Medicine (DICOM) workflows for imaging/modality coordination, often guided by Integrating the Healthcare Enterprise (IHE) profiles.
Why is RIS a cybersecurity concern?
RIS is connected to ePHI and critical imaging workflows. Compromise can disrupt radiology operations, expose data, or create integrity risks in imaging processes.
External References (Trusted Resources)
- Integrating the Healthcare Enterprise (IHE): Scheduled Workflow (SWF) Profile
- U.S. HHS: HIPAA Security Rule overview
- NIST SP 800-66 Rev. 2: Implementing the HIPAA Security Rule
- IEC 80001-1: Risk management for IT networks incorporating medical devices
How Blue Goat Cyber Helps
RIS environments sit inside larger medical device systems and healthcare networks—where cybersecurity, safety, and operations intersect. Blue Goat Cyber helps MedTech teams and healthcare stakeholders build defensible cybersecurity across connected ecosystems.
- Threat Modeling
- Medical Device Vulnerability & Penetration Testing
- Premarket Cybersecurity Support
- Postmarket Cybersecurity Management
- Contact Blue Goat Cyber
Bottom line: A Radiology Information System (RIS) is the workflow engine for radiology—and a critical node in the connected healthcare ecosystem. Secure the integrations, segment the environment, and build evidence-driven controls that hold up under real-world pressure.
