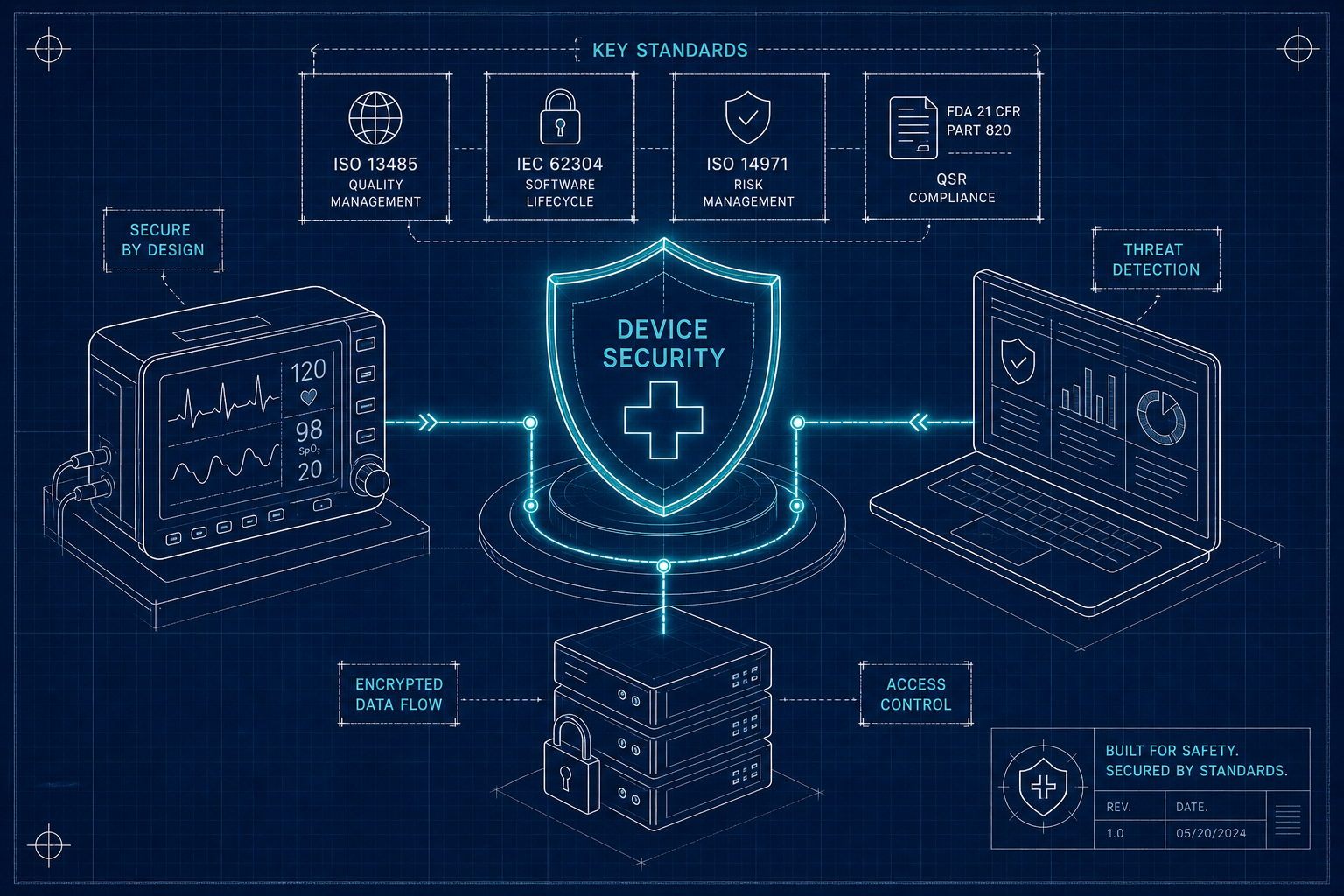
MedTech Cyber Standards Every Device Team Must Know
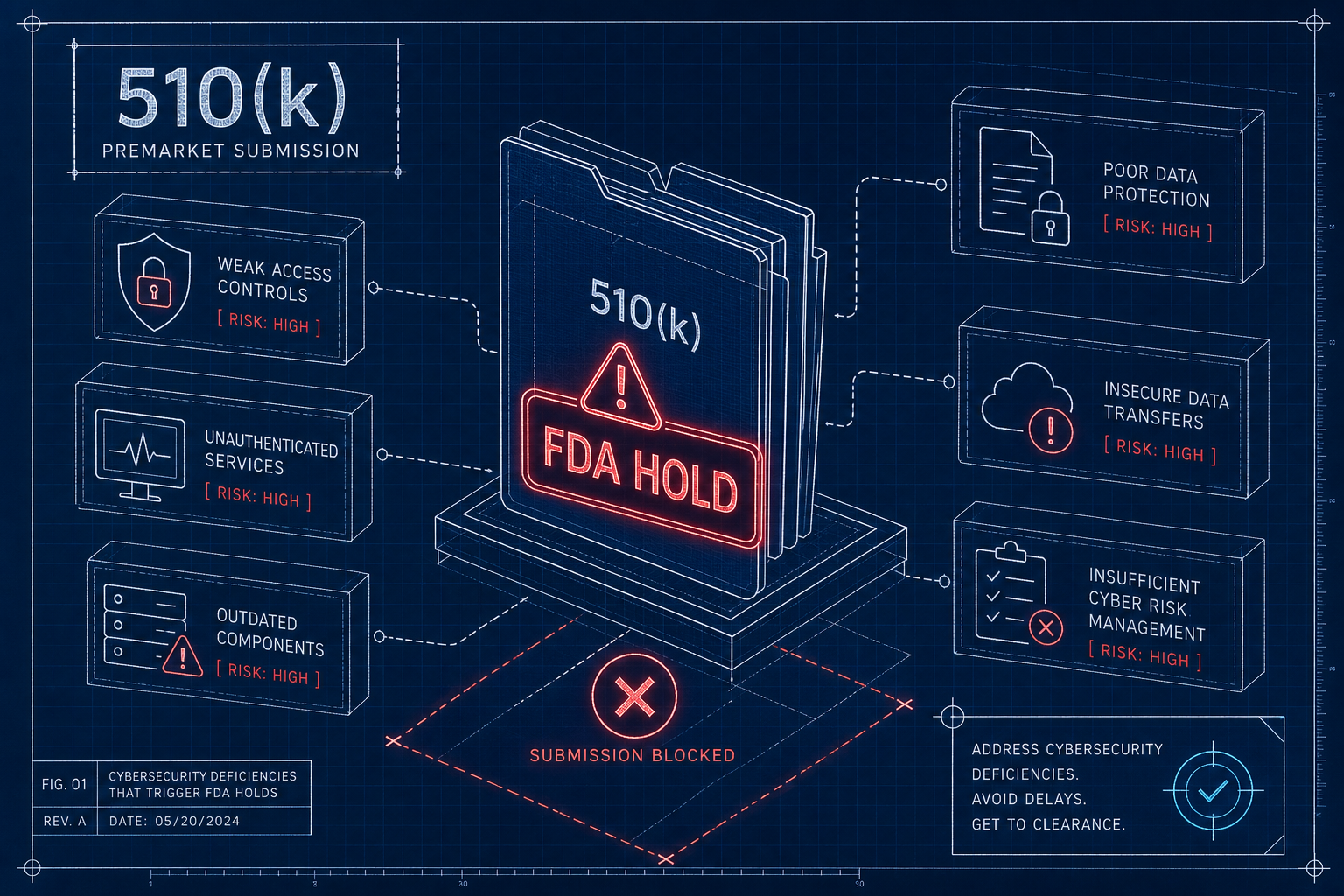
The seven MedTech cyber standards FDA reviewers expect - FDA premarket guidance, IEC 62304, ISO 14971, AAMI TIR57, UL 2900, IEC 62443, IEC 81001-5-1 - and how to map them as one program.
Read article