Published: February 11, 2024 · Last reviewed: May 1, 2026
Updated April 9, 2026
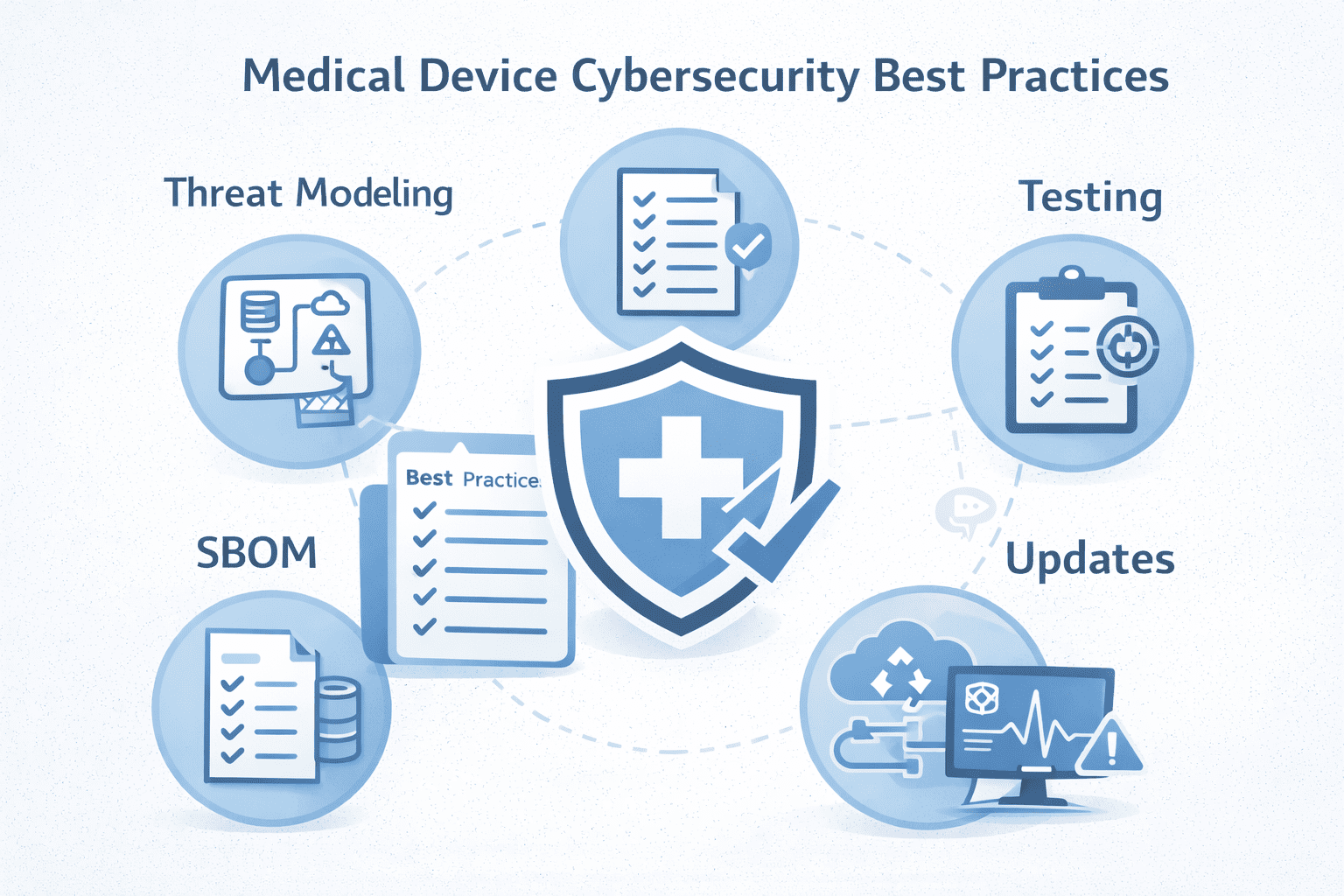
Medical device cybersecurity best practices prioritize patient safety and clinical operations by integrating security throughout the product lifecycle. Key practices include defining the full system ecosystem, performing realistic threat modeling, deriving traceable security requirements, maintaining an operational Software Bill of Materials (SBOM), and verifying security with risk-based testing. A strong postmarket program for vulnerability management and secure update mechanisms are also critical for sustained security.
Medical device cybersecurity isn’t just about protecting data-it’s about protecting patients, clinical operations, and essential device performance. As devices become more connected (through apps, cloud services, hospital networks, and remote updates), the attack surface grows, and the consequences of failure become increasingly severe: downtime, disrupted therapy, unsafe behavior, and loss of trust.
This guide gives you a practical, manufacturer-focused set of best practices you can implement-and the kind of evidence that supports modern FDA expectations, including lifecycle cybersecurity and Section 524B “cyber device” readiness.
Key Takeaways
- Define the complete system ecosystem, not just the device.
- Perform realistic threat modeling early in development.
- Formulate traceable security requirements from identified threats.
- Maintain an operational SBOM for proactive vulnerability monitoring.
- Conduct risk-aligned security testing and validation.
- Implement a secure and reliable update mechanism.
Quick answer: Medical device cybersecurity best practices (2026)
Medical device cybersecurity best practices include:
- Define the full system (device + app + cloud + update infrastructure)
- Threat model realistic attack paths and patient impact
- Turn threats into requirements with traceability to controls and tests
- Maintain an operational SBOM with continuous monitoring
- Verify with risk-based testing (including penetration testing where appropriate)
- Secure updates so you can remediate postmarket
- Run a real postmarket program (intake, triage, CVD, patching, communications)
If you do nothing else, do those.
Why cybersecurity matters for medical devices
Connected medical devices can be targeted for data theft, operational disruption (such as ransomware), and impact on availability. However, the more significant point is that cybersecurity issues can escalate into safety issues when they compromise availability, integrity, or essential performance.
A strong cybersecurity program reduces risk, supports regulatory readiness, and makes your product easier for customers to deploy and maintain.
Medical device cybersecurity best practices checklist
Use this as your practical build plan (and a final quality check before submission or release):
- Define system scope and interfaces
- Implement a Secure Product Development Framework (SPDF)
- Perform system-level threat modeling
- Convert threats into security requirements + traceability
- Design a security architecture that holds up in real deployments
- Build strong identity, authentication, and access control
- Maintain an operational SBOM (not a one-time file)
- Manage third-party and supplier risk (SOUP/OTS)
- Verify with testing aligned to risk (not just tools)
- Secure your update mechanism and release integrity
- Enable logging and monitoring for response readiness
- Operate postmarket cybersecurity as a program (CVD + remediation)
Best practice #1: Define the system (not just the device)
Cybersecurity starts with scope. Your “device” is usually an ecosystem:
- Device hardware/firmware
- Mobile/desktop apps
- Cloud services/APIs
- Update servers and build pipelines
- Customer networks and deployment constraints
Document your system boundaries, key interfaces, trust boundaries, and intended use environment. If reviewers (or customers) can’t see the system, they can’t trust your cybersecurity story.
Best practice #2: Build cybersecurity into your SPDF (secure by design)
A Secure Product Development Framework (SPDF) is a repeatable way to bake security into the lifecycle-so you’re not scrambling late-stage.
A practical SPDF includes:
- Security risk management integrated with product development
- Security architecture and design reviews
- Secure coding practices and code review discipline
- Security verification (testing) tied to real risk
- Postmarket monitoring, disclosure, and remediation workflows
This is the difference between “we added security features” and “we can prove security is maintained over time.”
Best practice #3: Threat model early (and keep it realistic)
Threat modeling is one of the highest ROI activities in MedTech cybersecurity-because it drives requirements, controls, and testing.
A good threat model includes:
- Assets (what must be protected)
- Entry points and external interfaces
- Trust boundaries and assumptions
- Realistic attack scenarios (not just generic lists)
- Mapping to mitigations and verification evidence
If the threat model is shallow, everything downstream gets shaky.
Best practice #4: Turn threats into security requirements and traceability
Avoid vague statements like “we use encryption.” Instead, create:
- Security requirements derived from threats and risk
- Controls that implement those requirements
- Traceability from threats/risks → requirements → controls → tests → results
Traceability is what makes your cybersecurity documentation defensible and reviewer-friendly.
Best practice #5: Design security architecture that holds up in the real world
Strong medical device security architecture typically includes:
- Secure defaults and hardening guidance
- Segmentation and network controls recommendations
- Authentication/authorization boundaries (least privilege)
- Encryption for data in transit and (when appropriate) at rest
- Key management that’s designed-not improvised
- Logging hooks that support investigation
- Secure update capability (covered more below)
A clean diagram showing interfaces and trust boundaries can prevent a lot of questions later.
Best practice #6: Get identity and access control right
Weak identity and access management is one of the most common root causes of device compromise. Practical access-control best practices include:
- Unique accounts (avoid shared credentials where possible)
- Least privilege (roles match job functions)
- Strong authentication for privileged access (and MFA where feasible in the environment)
- Secure credential storage (no hardcoded passwords, protect secrets/keys)
- Session management (timeouts, lockouts, audit trails as appropriate)
- A plan for provisioning/deprovisioning in real deployments
If your device uses service accounts, remote support access, or clinician/admin roles, document how access is controlled and monitored.
Best practice #7: Use SBOMs the right way (and keep them operational)
An SBOM is not a one-time deliverable-it’s a lifecycle tool.
Best practices include:
- Machine-readable SBOM tied to each release/build
- Coverage of third-party, open-source, and commercial components
- Continuous monitoring for newly disclosed vulnerabilities
- A clear disposition workflow (not affected / mitigated / patch planned / patched)
- Version mapping (which product versions are impacted)
This is how you respond quickly when a new CVE drops-without scrambling.
Best practice #8: Manage third-party and supplier risk (SOUP/OTS)
Most devices depend on third-party components (libraries, OS, middleware, SDKs, modules). Supplier risk becomes your risk.
Build a repeatable approach:
- Supplier intake requirements (component versions, security notices, support lifecycle/EOL)
- Change control for component updates
- Verification when components change (what must be retested)
- Contractual expectations where possible (notification timelines, patch availability)
- Documentation of rationale when a component cannot be updated immediately
This is also where SBOM monitoring becomes critical: you can’t manage what you can’t inventory.
Best practice #9: Verify with testing that matches your risk
Security testing should align to your threat model and architecture-not just run tools “because compliance.”
A strong approach may include:
- Vulnerability testing with clear disposition and remediation tracking
- Penetration testing for critical interfaces and realistic attack paths
- SAST/DAST where appropriate for your software stack
- Fuzz testing for parsers/protocol handlers (when relevant)
- Retesting after remediation to prove closure
The key is to turn results into clear evidence: what was tested, what was found, what was fixed, and what’s the residual risk.
Best practice #10: Make your update mechanism secure and reliable
If you can’t update safely, you can’t manage risk postmarket.
Update best practices include:
- Signed updates with authenticity and integrity checks
- Secure delivery channels (and replay protection where relevant)
- Rollback strategy (when safe/appropriate)
- Build integrity and release controls (you know what you shipped)
- Clear customer expectations (how updates happen, support windows)
Secure updates are a cornerstone of lifecycle cybersecurity.
Best practice #11: Enable logging and monitoring for response readiness
You can’t respond to what you can’t observe. Logging and monitoring best practices include:
- Log security-relevant events (auth attempts, config changes, update events, critical errors)
- Protect logs from tampering and inappropriate access
- Define retention appropriate to risk and use environment
- Make logs usable (consistent formats, timestamps, identifiers)
- Ensure logging doesn’t leak sensitive information
Even simple logs can dramatically improve incident response speed and quality.
Best practice #12: Operate postmarket cybersecurity like a program (not a scramble)
Postmarket security requires a defined workflow:
- Vulnerability intake (security contact + process)
- Triage and risk assessment (patient safety impact, exploitability, exposure)
- Coordinated vulnerability disclosure (CVD) process
- Remediation plans (patching or compensating controls)
- Customer communications and documentation
- SBOM monitoring and version impact tracking
This is where many organizations struggle-because it’s operational, not theoretical.
Common mistakes to avoid
- Treating cybersecurity as “data privacy only” instead of safety + availability + integrity
- No system-level threat model (or one that doesn’t match the architecture)
- No traceability from threats to controls and testing
- SBOM created once and forgotten
- Tool output pasted into documents with no context or disposition
- Vague postmarket plan with no real workflow or ownership
Conclusion
The best medical device cybersecurity programs are built to do two things well:
- reduce real-world risk to patients and clinical operations, and
- produce clear, test-backed evidence that holds up across the lifecycle.
If you want your cybersecurity program to scale (and your submissions to move faster), focus on a simple, traceable story: threat model → controls → testing evidence → SBOM → postmarket plan.
Schedule a Discovery Call so we can help.
Medical Device Cybersecurity FAQs
How do I get a quote for a medical device test from Blue Goat?
Please schedule a 30-minute Discovery Session with us so we can best understand your objectives.
What insights does Blue Goat Cyber provide related to software testing in the healthcare industry?
Blue Goat Cyber provides several key insights related to software testing in the healthcare industry, focusing on comprehensive methods for various software and medical devices. They emphasize the importance of governance in cybersecurity programs, ensuring that medical software complies with regulatory standards like FDA guidelines and HIPAA. Additionally, Blue Goat Cyber stresses proactive risk mitigation, including strategies for identifying and managing potential vulnerabilities in healthcare software. Their approach also includes educating healthcare organizations on cybersecurity risks and best practices, advocating for a culture of awareness and proactive security measures in the industry.
What are the security requirements that medical device applicants must now meet?
The U.S. Food and Drug Administration (FDA) has established specific cybersecurity requirements that medical device manufacturers must meet. These include:
-
Secure Product Development Lifecycle: Manufacturers are required to implement a secure product development lifecycle. This involves reducing the number and severity of vulnerabilities throughout the entire lifecycle of their devices, from design and development to distribution, deployment, and maintenance.
-
Threat Modeling and Post-Market Vulnerability Management: Manufacturers must conduct threat modeling and outline plans for addressing post-market vulnerabilities. This includes patching and software updates to respond to potential security issues.
-
Coordinated Disclosure of Exploits and Software Bill of Materials: Details of the methods for coordinated disclosure of exploits must be included. Manufacturers must also supply a software bill of materials (SBOM) that details all third-party commercial, open-source, and off-the-shelf software components used in their devices.
-
Process and Procedures for Postmarket Updates and Patches: Companies must provide details on the processes and procedures for releasing postmarket updates and patches that address security issues. This includes regular updates and out-of-band patches for critical vulnerabilities.
These requirements apply to "cyber devices," which are defined as any devices that run software, have the ability to connect to the internet, and could be vulnerable to cyber threats. As of October 1, 2023, the FDA's refuse-to-accept policy comes into force for pre-market submissions that lack the required cybersecurity information.
Medical device manufacturers should familiarize themselves with the FDA's updated guidance document, "Cybersecurity in Medical Devices: Quality System Considerations and Content of Premarket Submissions," to ensure their products meet the required cybersecurity standards. Failure to meet these requirements could result in the FDA rejecting pre-market submissions.
What new policy has the FDA announced for medical device manufacturers?
According to the recent announcement by the FDA, medical device manufacturers are now required to adhere to a new policy related to cybersecurity. Under this policy, all new applicants for medical devices must submit a comprehensive plan that outlines how they will actively monitor, identify, and address potential cybersecurity issues. This plan should also include steps to ensure that the device in question is adequately protected.
Additionally, the FDA now mandates that applicants establish a reliable process that reasonably assures the device's security. This includes taking necessary measures to make security updates and patches available regularly and in critical situations. The applicants must also provide the FDA with a detailed software bill of materials, encompassing any open-source or other software utilized in their devices.
Overall, this new policy enacted by the FDA emphasizes the importance of cybersecurity in medical devices and aims to ensure that manufacturers take appropriate measures to safeguard patient safety and protect against potential cyber threats.
What is Blue Goat's methodology for medical device cybersecurity assessment for FDA compliance?
Blue Goat uses a two-step Assessment Evolution test/retest approach for optimal outcomes. Within each Evolution, in addition to the actual medical device assessment and testing components, we dedicate access to our cybersecurity team for report clarification and knowledge exchange, assisting in your understanding of the test findings and the remediation strategies.
Post-remediation of Evolution 1, we will again conduct the cybersecurity assessment and penetration test to assess the efficacy of addressing identified vulnerabilities. This second set of reporting demonstrates a more robust security posture and, therefore, a more impactful Letter of Attestation.
Our overall medical device security assessment and testing process involves four high-level phases:
- Discovery
- Security Boundary Definition
- Security Risk Assessment
- Mitigation Strategy
Medical Device Assessment Evolution 1
1. Preparation (Offsite). Before we travel to your facility, we prepare for the onsite visit. Our preparation consists of Discovery, such as a review of the following:
- Design documents
- Data flow diagrams
- Use cases
- Traceability matrix
- Security architecture
- User manuals
- Admin/maintenance manuals
- Installation procedures and guidance
- Risk assessment
- Hazard analysis
- Source code
- Total Product Life Cycle (TPLC) documentation
- Product photos
- Any other relevant device documentation
We intend to get familiar with your product, formulate a plan of action, and develop the Test Plan and Test Cass before our onsite visit. This allows us to optimize our time onsite.
2. T esting (Onsite or at Blue Goat's facility). We travel to your facility to perform the cybersecurity assessment and penetration test against your medical device/system. Testing can also be performed at Blue Goat’s facility if you ship the equipment to us. Our testing consists of identifying all entry points into the system, such as Ethernet, Fiber, WiFi, USB, BTLE, Serial, and HDMI. We assess vulnerabilities associated with each entry point and the exploitation of initial and subsequent vulnerabilities. Any critical findings discovered will immediately be brought to your attention. In addition, due to the nature of our engagement, we can share our test results with you daily as an end-of-day update.
3. Reporting (Offsite). At the end of testing, we generate a medical device cybersecurity assessment and penetration test report that ranks our findings based on criticality. The report will include step-by-step exploitation steps, described with screenshots. The report also includes remediation guidance for each finding.
4. Report Presentation (Offsite). Once the report is completed, we securely send it to you and review it via Zoom.
Between Evolution 1 and Evolution 2, you will work on fixing issues identified in Evolution 1.
Medical Device Assessment Evolution 2
When you are ready for us to retest the medical device, we repeat the applicable steps of Evolution 1 in Evolution 2. This will be completed onsite at Blue Goat or your facility.
At the end of Evolution 2, we will generate a Letter of Attestation that summarizes the medical device's scope, findings, and overall risk rating. The Letter of Attestation is intended to be shared with clients, auditors, regulators, etc.
What is the goal of a penetration test against a medical device?
Blue Goat understands the critical importance of securing your wired or wireless medical devices and protecting your business from cybercriminals. We aim to assess the cybersecurity posture of your devices comprehensively, enabling us to identify vulnerabilities and weaknesses in their networks and infrastructure. By conducting a thorough penetration test, we ensure your patients' safety and reduce the risk your organization faces.
During the penetration test, our team will meticulously evaluate the security defenses of your medical devices, seeking out potential entry points for cyber attacks. We leave no stone unturned, examining hardware, software, peripherals, and all other input/output systems. Our experts meticulously fuzz, analyze and test each aspect for flaws that could compromise patient care or the overall integrity of the medical device.
In our quest to fortify your device's security, we pay particular attention to common vulnerabilities and exposures (CVEs) prevalent in the medical device landscape. We delve into the intricacies of bypassing kiosked applications that run on these devices, ensuring that unauthorized access to underlying operating systems is not possible. This process requires thorough effort, often spanning hours or even days, to uncover a chain of flaws that would enable us to bypass these controls successfully.
Going beyond software vulnerabilities, we also explore the physical aspects of the device. Our assessment includes inspecting for alternate ports such as JTAG, UART, or other unprotected ports, additional USB ports, and accessible hard drives.
But our work doesn't stop there. We also conduct forensics and post-exploitation movements, meticulously detonating payloads, pivoting, and adjusting operating systems to simulate real-world scenarios that could impact patient care. Additionally, we delve into reverse engineering proprietary binaries and programs, searching for sensitive keys to validate whether encryption utilizes statically set or dynamically created encryption keys.
This comprehensive penetration test offers you a holistic view of your medical device's security vulnerabilities and weaknesses. Our findings will enable us to provide you with detailed recommendations for patching and strengthening your device's defenses, significantly enhancing patient safety and reducing the risk faced by your organization. With Blue Goat, you can trust that your medical devices are safeguarded against cyber threats with the utmost dedication and expertise.
AAMI TIR57 is a technical information report focused on the principles for medical device security-risk management. It's a guideline from the Association for the Advancement of Medical Instrumentation (AAMI), an organization well-known for its work in medical devices.
Overview
AAMI TIR57, titled "Principles for medical device security-Risk management," offers a structured approach to managing cybersecurity risks in medical devices. This is particularly crucial because medical devices, like any other connected tech, can be vulnerable to cyber threats. This report provides guidance on implementing security measures throughout a device's lifecycle, from design and development to decommissioning.
The "Why"
The importance of TIR57 lies in its focus on patient safety and data security. As medical devices become more interconnected and rely on software, they're increasingly susceptible to cyber threats. These threats can potentially impact the functionality of the devices, leading to patient harm. TIR57 helps manufacturers and healthcare providers mitigate these risks by establishing robust security practices.
Examples and Case Studies
Let's say a hospital uses networked medical devices (like heart rate monitors or insulin pumps). These devices are critical for patient care. If they're hacked due to weak security, the results could range from data breaches to life-threatening situations. Implementing the principles of AAMI TIR57, such as conducting thorough risk assessments and including cybersecurity considerations in the device design, helps prevent such scenarios.
For Blue Goat Cyber, understanding and implementing the guidelines in AAMI TIR57 can be a major value proposition. It means you can offer services that align with these standards, assuring your clients that their medical device security is managed effectively. This includes conducting risk assessments, advising on secure device design, and offering ongoing security support.
Connecting the Dots
In your line of work, AAMI TIR57 is more than just a set of guidelines. It's a framework that helps ensure the security and safety of medical devices-a critical aspect of healthcare cybersecurity. By integrating these principles into your services, you position Blue Goat Cyber as a knowledgeable and trustworthy provider of medical device security, aligning well with your goal of growing the company's revenue.
Understanding and applying AAMI TIR57 can give you an edge, especially when communicating with cybersecurity decision-makers in the healthcare sector. They're looking for experts who understand the technical side of cybersecurity and the unique challenges of medical devices. Your expertise in this area can be a significant differentiator.
What is a Cybersecurity Bill of Materials (CBOM)?
A Cybersecurity Bill of Materials (CBOM) is an essential requirement enforced by the FDA from March 29, 2023, onwards for medical devices. It mandates medical device manufacturers to provide a comprehensive and accurate list of software and hardware components used in their devices, including any third-party software and open source components. This list, known as the CBOM, serves as a self-attestation by manufacturers, indicating the accuracy and completeness of the components used in their medical devices. One critical aspect of the CBOM is the inclusion of a Software Bill of Materials (SBOM), which ensures complete transparency regarding software components used in medical devices. Given the crucial nature of medical devices and the potential risks associated with cybersecurity, having a comprehensive and accurate SBOM is particularly vital in maintaining the security and integrity of these devices.
How can Blue Goat help in generating accurate SBOMs?
Blue Goat has a long-standing record of providing reliable and precise Software Bill of Materials (SBOMs) for its clients for over ten years. We have developed sophisticated tools that enable us to identify components, even at the snippet level, accurately. With our advanced string search algorithms, we can effectively detect all third-party and commercial components. Additionally, Blue Goat offers a comprehensive SBOM-as-a-service solution, which ensures that clients receive complete and accurate SBOMs in standard formats such as SPDX and CDX, which comply with the FDA's requirements. Moreover, Blue Goat can validate internally generated SBOMs or those created by their software supply chain partners, guaranteeing alignment with FDA regulations. By leveraging out expertise and tools, Blue Goat can play a crucial role in assisting organizations to generate reliable and accurate SBOMs.
What's the difference in a CBOM and SBOM?
The terms "Cybersecurity Bill of Materials" (CBOM) and "Software Bill of Materials" (SBOM) are related concepts in the realm of cybersecurity and software management, often used within the context of improving transparency and security of software products and systems, including medical devices. The primary distinction between the two lies in their scope and specific focus:
-
Software Bill of Materials (SBOM): An SBOM is a detailed list that provides an inventory of all components, libraries, and modules that make up a piece of software, including both open-source and proprietary elements. The primary purpose of an SBOM is to give users (which can include end-users, developers, and security professionals) a clear understanding of what software is running in their environment. This transparency is crucial for vulnerability management, license management, and security analysis, enabling users to identify potential security risks, comply with licensing requirements, and perform effective patch management.
-
Cybersecurity Bill of Materials (CBOM): A CBOM extends the concept of an SBOM by including not just software components but also detailing hardware components, network dependencies, and any other elements critical to understanding the cybersecurity posture of a device or system. The CBOM is particularly relevant in contexts where the security of the entire ecosystem, including physical components and network interactions, is critical. For example, understanding the full spectrum of components and dependencies in medical devices or industrial control systems is essential for assessing vulnerabilities, potential attack vectors, and overall system security.
In essence, while an SBOM is specifically focused on software components, a CBOM provides a broader view that encompasses all elements relevant to cybersecurity. Both are tools aimed at enhancing the security and manageability of software and systems, but they do so from slightly different angles. The adoption of SBOMs and CBOMs is encouraged by various cybersecurity frameworks and standards to promote transparency and facilitate better risk management practices.
What is the significance of SBOMs and SPDX in the present and future?
March 29, 2023, marked a significant milestone as the FDA began enforcing cybersecurity requirements for medical devices, urging manufacturers to comply with a Cybersecurity Bill of Materials (CBOM). A crucial element of the CBOM is the inclusion of a Software Bill of Materials (SBOM), which outlines the comprehensive list of software and hardware components utilized within medical devices. This encompasses not only internally developed software but also third-party software and open-source components.
The significance of SBOMs lies in their ability to enhance transparency and accountability in the supply chain of medical devices. By mandating medical device manufacturers to self-attest to the accuracy of their SBOMs, regulators can obtain a holistic view of the components employed in the production of these devices. This promotes better assessment and management of potential security vulnerabilities.
One of the recognized standards for SBOMs is the Software Package Data Exchange (SPDX) format. SPDX provides a consistent and standardized way to document and share SBOMs, enabling efficient communication between various stakeholders, including manufacturers, regulators, healthcare providers, and consumers. This universal language supports interoperability and simplifies the evaluation of SBOMs by allowing for easy comparison and analysis.
The significance of SBOMs and SPDX in the present and future lies in their ability to fortify cybersecurity practices and enhance transparency across industries, not just within the medical field. As highlighted by the National Telecommunications and Information Administration (NTIA), the implementation of SBOMs should extend beyond medical devices, becoming a common practice in other sectors as well. This indicates a growing recognition of the importance of understanding and managing the software components in all connected systems.
With the regulatory enforcement of SBOMs, companies across industries are actively working towards creating compliant SBOMs, with some seeking assistance from third-party providers who specialize in generating accurate and robust SBOMs. These providers, like Synopsys, offer sophisticated tools and solutions that can precisely identify software components used, including third-party and commercial components. They can also ensure that the generated SBOMs align with the specific requirements set forth by regulatory bodies, such as the FDA.
What are the additional elements required by the FDA for an SBOM?
The FDA has established additional requirements for a Software Bill of Materials (SBOM) for medical devices. In addition to the minimum elements defined by the National Telecommunications and Information Administration (NTIA), the FDA mandates including specific information. These additional elements encompass the support level, support end date, and known security vulnerabilities of the software components used in the medical devices.
While open source projects may not have designated support levels or support end dates, these additional elements largely apply to third-party or commercial components integrated within the medical device application. It is crucial to include complete and accurate SBOMs for medical devices, as they enable transparency and focus on cybersecurity.
Blue Goat understands the critical need for compliance regarding medical device software. Our team of experts is well-versed in the intricacies of the security process, ensuring that your organization is protected from costly and dangerous hacks. With years of experience in various types of testing, we are equipped to address the unique requirements of your specific device.
We go beyond just security and take compliance seriously. Our team will guide you through the complex regulatory landscape, including the stringent guidelines the FDA sets. We understand the importance of timely product releases, and our expertise will help you navigate the necessary steps to ensure compliance with required standards and regulations.
Rest assured that with Blue Goat by your side, your medical device software will meet the necessary compliance standards, giving you peace of mind and confidence in the safety and effectiveness of your product. Trust in our experience and dedication to deliver results that meet industry standards.
What tools does Blue Goat use for testing software for medical devices?
Blue Goat Cyber uses a combination of Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) for medical device software testing. SAST involves analyzing the source code to identify vulnerabilities, while DAST tests the running application to find security issues. Both methods are critical for ensuring the security of medical devices, which handle sensitive data and are subject to strict FDA regulations and HIPAA guidelines. Blue Goat Cyber's approach addresses unique concerns related to medical devices, such as compliance with evolving security standards and the protection of critical patient information.
In addition to SAST and DAST, Blue Goat Cyber also incorporates penetration testing and vulnerability assessment tools for comprehensive medical device software testing. Penetration testing tools simulate real-world cyberattacks to identify potential security breaches, while vulnerability testing tools systematically scan for known vulnerabilities. Together, these methods provide a robust framework for ensuring the security and compliance of medical devices, addressing unique challenges such as critical functionality, data sensitivity, and regulatory standards like FDA clearance and HIPAA compliance.
What is some background on medical device vulnerabilities?
Over the past few years, the Internet of Things (IoT), coupled with the ubiquitous nature of Information Technology, has resulted in an ever-expanding attack surface where rapid solution development and enhanced functionality routinely prevail over security. For example, attackers once disrupted most U.S. internet activity using 61 default IoT usernames and passwords. Consumers failed to change them before activating their devices, effectively turning our gadgets into culprits responsible for one of the largest Distributed Denial of Service (DDoS) in the world’s history.
The healthcare industry is rapidly adopting IoT devices (often called the Internet of Medical Things (IoMT)) to enhance patient safety and healthcare workers' treatment delivery. From medication administration to remote sensor monitoring, embedded medical devices are improving the quality of care and increasing interaction with their providers. While this technology was created with good intentions, the lack of security in product design phases is a major concern that will likely materialize into malicious action with grave consequences.
The consequences became clear in 2017 as researchers were able to acquire equipment (from $15 - $3,000) and intercept the radio frequencies from cardiac devices. With this capability, they could reprogram the devices to modify the patient’s heartbeat and drain the internal battery. As a result, the FDA recalled almost 500,000 pacemakers and enforced in-person firmware updates. Researchers have also demonstrated similar capabilities on infusion pumps and MRI systems.
Non-networked medical devices may be operating at a higher level of risk. Ease of access and the availability of RFID cloners contribute to a relatively weak physical security posture. In 2018, researchers demonstrated the capability to emulate and alter a patient’s vital signs in real-time using an electrocardiogram simulator they found on eBay for $100.
In late 2018, the Department of Health and Human Services Office of the Inspector General (IG) critiqued FDA procedures in assessing post-market cybersecurity risk to medical devices. To fortify the FDA's core mission “to ensure there is a reasonable assurance that medical devices legally marketed in the United States are safe and effective for their intended uses,” they outlined their ongoing efforts in enhancing medical device security.
According to the FDA, “Healthcare Delivery Organizations (HDOs) are responsible for implementing devices on their networks and may need to patch or change devices and/or supporting infrastructure to reduce security risks. Recognizing that changes require a risk assessment, the FDA recommends working closely with medical device manufacturers to communicate necessary changes.”
Blue Goat can help HDOs transfer that risk by evaluating the cybersecurity posture on your wired or wireless medical devices.
Contact us today and inquire about our full-range penetration testing.
We can significantly increase your patient’s safety while reducing your organization’s risk.
What are some reasons for the lack of security in many medical devices?
The lack of security in many medical devices can be attributed to several key factors. One significant factor is the increased scrutiny over the vulnerabilities of these devices, which ultimately forced regulatory bodies like the FDA to reassess their cybersecurity requirements. A report by the FBI revealed that a staggering 53% of digital medical devices and internet-connected products had critical vulnerabilities, exposing patients and medical providers to various security risks. These vulnerabilities were often found in unpatched and outdated devices, which served as the weak link in the cybersecurity chain. Moreover, research suggests that 88% of healthcare cyberattacks involved an IoMT (internet of medical things) device, further underscoring the urgent need for robust security measures.
Inadequate security controls in medical devices have long been a pressing issue. Many of these devices have been designed with a primary focus on their medical functions, with security measures being added as an afterthought, if at all. These "bolted on" security controls have proven to be less than adequate, leaving vulnerabilities that malicious actors can exploit. Additionally, the lack of mandatory requirements and accountability in the past has contributed to the lax approach towards security in the industry. However, recent changes have brought about a much-needed shift in mindset. Introducing new regulations and the potential for costly fines for non-compliance have made it clear that the days of overlooking security are over.
What is the purpose of the new cybersecurity regulations implemented by the FDA?
The FDA's new cybersecurity regulations have been put in place to ensure the security of medical devices. Section 524B (c) of these regulations defines a device that falls within the scope of these requirements. According to this section, a device is considered to be within the regulations if it includes software that is validated, installed, or authorized by the sponsor of the device or within it. Additionally, the device must be able to connect to the internet and possess technological characteristics that have been validated, installed, or authorized by the sponsor. This definition highlights the potential vulnerability of these devices to cyber threats. The purpose of these regulations is to address these vulnerabilities and establish a higher level of accountability and responsibility among medical device manufacturers. By mandating compliance and introducing potentially costly fines for non-compliance, the FDA aims to ensure that these regulations have a tangible and meaningful impact on the security of medical devices. The focus on accountability signifies a shift from the previous voluntary compliance approach, making it clear that laxity in cybersecurity measures is no longer acceptable in the medical device industry.
What testing needs can Blue Goat Cyber cover?
Blue Goat Cyber is a reliable partner that can meet a wide range of testing needs, ensuring the utmost satisfaction of our clients. Our expertise extends to various areas, including penetration testing, network penetration testing, web application penetration testing, API penetration testing, HIPAA penetration testing, SOC 2 penetration testing, PCI penetration testing, application penetration testing, internal penetration testing, black box penetration testing, gray box penetration testing, white box penetration testing, and mobile application penetration testing.
But that's not all. We understand the importance of cybersecurity in today's digital landscape, especially in industries like healthcare. That's why we offer specialized services to address the unique testing needs of medical device software. Our dedicated healthcare testing professionals are well-versed in verifying the quality of medical device software requirements and conducting thorough testing at the API, integration, and system levels. With a focus on security, we ensure that software architecture is robust and impervious to vulnerabilities.
To further enhance the reliability and security of medical device software, our team performs extensive software code review and code analysis, leaving no stone unturned to ensure top-notch quality. We go beyond the technical aspects and conduct user acceptance testing to ensure that the software meets the usability requirements of healthcare professionals and end-users.
But it doesn't stop there. Our compliance experts, including FDA and HIPAA, are well-versed in the regulatory landscape. They work closely with our clients to ensure their medical device software meets the required standards and regulations. With detailed reporting and comprehensive test documentation that aligns with ISO 13485 and ISO/IEC/IEEE 29119-3:2021, we provide full transparency in our testing activities.
In addition to our expertise in healthcare and medical device software testing, we offer a wide range of services to bolster cybersecurity. Our offerings include medical device cybersecurity, cyber threat awareness training, enterprise cybersecurity audit, static application security testing (SAST), dynamic application security testing (DAST), vulnerability assessment services, CISO-as-a-Service, physical security assessment, phishing services, and HIPAA security risk analysis (HIPAA SRA).
At Blue Goat Cyber, we take pride in catering to diverse testing needs, ensuring our clients receive comprehensive and reliable solutions. Our expertise and commitment to excellence assure you that your software and systems are robust, secure, and compliant.
Blue Goat offers comprehensive solutions to help organizations protect their assets and networks while ensuring safer medical devices are developed. Organizations partnering with Blue Goat can access various services and expertise to establish a robust security testing program.
Through their extensive experience and knowledge in cybersecurity, Blue Goat can provide organizations with a comprehensive assessment of their current security measures. They can identify vulnerabilities and potential risks within the network infrastructure and recommend effective strategies to strengthen the overall security posture. Organizations can better protect their assets and networks from cyber threats by implementing these measures.
Moreover, Blue Goat offers specialized guidance to the healthcare industry to ensure the production of safer medical devices. They understand the unique security challenges medical device manufacturers face and can provide tailored solutions to mitigate these risks effectively. Their expertise in securing medical devices can assist organizations in adhering to FDA regulatory compliance requirements and industry best practices, reducing the likelihood of device vulnerabilities and potential data breaches.
What is the FDA's new requirement for connected medical devices?
The FDA has introduced a new requirement for connected medical devices, which went into effect on March 29, 2023. This requirement focuses on cybersecurity and aims to enhance the safety and security of these devices. One component of this requirement is the implementation of a Cybersecurity Bill of Materials (CBOM).
Under the CBOM, manufacturers of medical devices will need to attest to the accuracy of a comprehensive list of software and hardware components utilized in their devices. This list should include the components developed by the manufacturer and any third-party software and open-source components incorporated into the device.
Specifically, the FDA emphasizes the significance of a Software Bill of Materials (SBOM) within the CBOM framework. An SBOM is essential for connected medical devices as it provides a complete and accurate inventory of all software components used. It allows for better tracking of potential vulnerabilities and aids in efficient response and mitigation of any possible cybersecurity incidents.
By enforcing this new requirement, the FDA aims to ensure that manufacturers prioritize cybersecurity in developing and maintaining connected medical devices. Ultimately, this initiative seeks to enhance these devices' overall safety and security, benefiting healthcare professionals and patients alike.
How can cybersecurity vulnerabilities in medical devices lead to patient data breaches?
Patient Monitors: Devices monitoring vital signs like heart rate and blood pressure are susceptible to data interception and manipulation, posing a significant risk to patient data security. The vulnerabilities in these devices can be exploited by cyber criminals, allowing them to intercept and manipulate the data being collected. This manipulation can lead to misdiagnosis or delayed treatment, endangering the safety and well-being of patients.
MRI Machines: MRI machines play a critical role in diagnostic imaging. However, they are not immune to cybersecurity threats. Cyber-attacks targeting these machines can disrupt their operation, potentially leading to incorrect imaging data or even complete operational failure. Such disruptions can have serious consequences, affecting diagnosis accuracy and treatment plans.
Radiation Therapy Systems: The potential hacking of radiation therapy systems poses a significant threat to patient safety. These systems are used in the treatment of cancer patients, and any unauthorized access to their controls can result in incorrect radiation doses. This can have severe repercussions, either by delivering insufficient radiation for effective treatment or by subjecting patients to dangerously high doses, leading to serious harm.
Diagnostic and Imaging Equipment: Sophisticated medical equipment like CT scanners and ultrasound machines are not immune to cyber threats. If these devices are compromised, they can provide false diagnostic information, leading to incorrect treatment decisions. The manipulation of diagnostic data can have detrimental effects on patient care, potentially delaying appropriate treatment or subjecting patients to unnecessary procedures.
Surgical Robots: Surgical robots have revolutionized minimally invasive surgeries, but their reliance on precise controls makes them vulnerable to cyber-attacks. Unauthorized access or manipulation of these devices can result in loss of control or the manipulation of movements during surgery. Such interference can lead to surgical errors, compromising patient safety and potentially causing harm.
Defibrillators: External defibrillators are critical life-saving devices used in emergency situations. However, they are not immune to cybersecurity vulnerabilities. In the event of a cyber-attack, these defibrillators can be hacked to disrupt their lifesaving shocks or drain their batteries. Such malicious interference can render the devices useless during critical moments, jeopardizing patient outcomes.
Hospital Networking Equipment: While not directly involved in patient care, hospital networks are vital for the operation of all connected medical devices. A breach in network security can have widespread consequences, including dysfunction of medical devices and loss of critical patient data. The interconnected nature of healthcare systems magnifies the impact of a cyber-attack on networking equipment, potentially disrupting the entire healthcare infrastructure.
These vulnerabilities underscore the pressing need for robust cybersecurity measures and safeguards in the healthcare sector. The implementation of up-to-date software, encryption protocols, and strong password security is crucial to protect patient data and ensure the safe and effective operation of medical devices.
What are the consequences of cyberattacks on medical devices?
The consequences of cyberattacks on medical devices are grave and can have a significant impact on patient safety and healthcare institutions. Direct interference with device operations can lead to incorrect treatment, posing severe health risks to patients. These security breaches not only pose immediate dangers but also erode confidence in the reliability and safety of medical devices and healthcare institutions as a whole.
Recovering from a cyberattack can be a costly and time-consuming process. It often involves device recalls, software upgrades, and potential legal implications. These measures are necessary to address the vulnerabilities exploited during the attack and prevent further breaches in the future. Healthcare institutions must invest in robust cybersecurity measures to safeguard networked medical devices and protect patient health.
Moreover, the potential for cyber attackers to gain remote control of medical devices is a cause for concern. This unauthorized access allows them to manipulate device settings, administer incorrect doses of medication, or disrupt the vital functions of life-support machines. Such malicious actions can have life-threatening consequences for patients, underscoring the urgent need for enhanced cybersecurity measures.
It is imperative that the medical profession prioritizes the security and safety of networked medical devices. Steps must be taken to reduce the risk of cyberattacks, ensure the integrity of medical devices, and maintain patient trust in healthcare institutions. By promoting a proactive approach to cybersecurity, we can mitigate the potential harm caused by cyberattacks on medical devices and safeguard patient well-being.
What are networked medical devices and why is cybersecurity important for them?
Networked medical devices are interconnected devices used in healthcare settings that rely on wireless technologies. These devices play a crucial role in patient care, such as insulin pumps, pacemakers, infusion pumps, patient monitors, MRI machines, and more. They enable doctors and healthcare professionals to remotely monitor and manage patients, providing efficient and minimally invasive procedures.
However, the increasing interconnectedness of these devices has raised cybersecurity concerns that cannot be ignored. When networked medical devices are compromised, they become vulnerable to malicious attacks by hackers. This poses a significant risk to patient safety, potentially resulting in severe harm or even death. The urgent need for robust cybersecurity in healthcare technology is underscored by several high-profile instances of medical device hacking.
For instance, insulin pumps have been manipulated remotely, exposing patients to the risk of insulin overdose. Pacemakers, essential devices for regulating heart rhythms, have vulnerabilities that can be exploited by hackers to alter heart rhythms or deplete the battery, leading to life-threatening situations. The infamous WannaCry ransomware attack on the UK's National Health Service demonstrated how cyber-attacks on hospital networks can indirectly impact patient care and safety.
These vulnerabilities clearly highlight the critical importance of enhanced security protocols, regular software updates, and vigilant monitoring. By implementing these measures, healthcare providers can protect patient safety and ensure the reliability of these essential networked medical devices. It is imperative to address these cybersecurity concerns to maintain the trust and integrity of the healthcare industry while harnessing the benefits and advancements offered by interconnected medical devices.
What recommendations are given to prevent medjacking and secure networked devices?
To prevent medjacking and ensure the security of networked devices, the following recommendations are provided:
1. Promptly address existing devices: Take immediate action to remediate any potential infections on your networked devices.
2. Swiftly implement software/hardware fixes: Develop a strategic plan to efficiently integrate and deploy the necessary updates and fixes provided by medical device manufacturers.
3. Seek expert consultation: Engage competent HIPAA consultants to evaluate and assess your compliance program, providing on-site guidance and expertise. If needed, request a quote for a thorough HIPAA audit.
4. Prioritize cybersecurity-minded vendors: Evaluate medical device vendors based on their commitment to cybersecurity. Choose vendors that allow you to modify passwords, offer regular updates, and are willing to conduct quarterly reviews with you.
5. Manage device access: Implement strict access control measures, particularly through USB ports. Consider utilizing one-way memory sticks to prevent the spread of infections among similar devices.
6. Establish secure network zones: Isolate devices within dedicated, secure network zones. Protect them further by implementing an internal firewall that only permits access to specific services and authorized IP addresses.
7. Address end-of-life for medical devices: Regularly assess the efficacy and longevity of your medical devices. Dispose of devices that are no longer supported by manufacturers or are unable to handle malware effectively. Prior to disposal, ensure the secure wiping or destruction of any patient data stored on the devices.
By following these recommendations, you can significantly enhance the prevention of medjacking incidents and strengthen the overall security of your networked devices.
Why don't traditional cyber defense tools work with medical devices?
Traditional cyber defense tools are not compatible with network connected medical devices for several reasons. Firstly, these devices often lack the necessary infrastructure to support the installation and operation of security tools. Unlike standard computers or mobile devices, medical devices have limited processing power, memory, and storage capacity. This makes it impractical, if not impossible, to run resource-intensive security software on such devices.
Additionally, applying any software modifications to these medical devices could be perceived as tampering and may potentially impact their compliance with regulations, specifically those set by the Food and Drug Administration (FDA). The FDA has emphasized the importance of manufacturers implementing adequate security measures, but restrictions on modifying devices make it challenging to enhance their security post-production.
Furthermore, traditional security tools are typically designed to protect more conventional systems and networks. They may not have been specifically developed or adapted to address the unique vulnerabilities and intricacies associated with medical devices. As a result, these tools may not effectively identify and mitigate the specific threats targeting medical devices, leaving them vulnerable to cyberattacks.
Given the critical nature of medical devices and the potential risks posed by cybersecurity breaches, it is important for manufacturers to integrate proper security tools directly into the design and production of these devices. This would ensure that they are secure from the outset and comply with FDA regulations.
Who is responsible for maintaining security within medical devices?
Maintaining security within medical devices is the responsibility of manufacturers. The FDA emphasizes that manufacturers are required to stay diligent in identifying and addressing risks and hazards associated with their devices, including those related to cybersecurity. However, it is noted that not all manufacturers take this responsibility seriously.
What types of medical devices are at the highest risk of being hacked?
The types of medical devices that are most vulnerable to hacking are stationary devices. While it is unsettling to contemplate the possibility of internally embedded medical devices being hacked and tampered with, it is important to note that the primary motivation for hackers is financial gain rather than terrorism. These cybercriminals primarily target stationary devices because they present the highest potential for stealing valuable patient data in large quantities.
What is medjacking and how does it pose a threat to healthcare organizations?
Medjacking, also known as medical device hijacking, is a serious cybersecurity issue that puts healthcare organizations at risk. It involves hackers compromising networked medical devices, including consumer health monitoring devices, wearables, embedded devices, and stationary devices, which are all connected to the internet.
One of the primary reasons why medjacking poses a threat is the valuable patient health data that these devices contain. Stationary devices like medical x-ray scanners and chemotherapy dispensing stations are particularly vulnerable, as they hold sensitive information that cybercriminals can exploit. In fact, medical data carries a higher value in the black market compared to credit card data, making these devices an attractive target for hackers.
The main factor contributing to the vulnerabilities in medical devices is the lack of security prioritization from manufacturers. These devices often do not come with robust built-in security measures, making them easy targets for hackers. Furthermore, the use of cyber defense tools is limited when it comes to medical devices, exacerbating the security risks.
Making matters worse, the government has not taken strong action against manufacturers or enforced strict security measures to mitigate these risks. This lack of regulatory pressure leaves healthcare organizations more exposed to potential medjacking incidents.
Another challenge in addressing medjacking is the difficulty in patching and fixing vulnerabilities in devices that are constantly in use. Healthcare organizations rely on these devices for critical functions and may face logistical challenges in implementing necessary security updates.
The consequences of medjacking can be severe for healthcare organizations. They are at risk of violating HIPAA regulations, which can lead to legal and financial penalties. Additionally, data breaches resulting from medjacking incidents can have serious implications for patient data security and confidentiality.
To combat the threat of medjacking, healthcare organizations should take proactive measures. This includes remediating infected devices, seeking fixes and updates from manufacturers, consulting with HIPAA experts to ensure compliance, evaluating vendors with a strong focus on cybersecurity, managing device access, isolating devices in secure network zones, and properly disposing of outdated devices.
What is medical device software testing?
Medical device software testing is a critical process aimed at ensuring that software embedded within or designed to control medical devices functions accurately, reliably, and in compliance with regulatory standards. This testing verifies the software's adherence to its intended functionality, user interface, integration, and overall performance requirements as dictated by medical device regulations, such as the FDA's 21 CFR Part 11 and the internationally recognized IEC 62304 standard. The objective is multifaceted, encompassing the removal of defects in software architecture and code, ensuring the software meets strict regulatory compliance, and ultimately contributing to the production of world-class, safe medical devices.
Key components of medical device software testing include:
-
Functional Testing: This evaluates the software's operational aspects to ensure it performs its intended functions correctly. It involves detailed testing of the software's features and capabilities.
-
Device Verification Testing: It verifies that the device as a whole, including its software, meets all specified requirements. This testing ensures that the product is designed correctly and works as expected.
-
Security Testing: Given the sensitivity of medical data and the potential impact of cybersecurity threats, testing for security vulnerabilities is essential. It helps in identifying and mitigating potential security risks.
-
Interoperability Testing: This ensures that the medical device can operate compatibly and safely with other systems or devices. It's crucial for devices that are part of a larger ecosystem of medical equipment.
-
Usability Testing: Focused on the human-device interaction, usability testing ensures that the device can be used efficiently, effectively, and satisfactorily by the intended users.
-
Performance Testing: This assesses the software's stability, speed, and scalability under various conditions. It is crucial for ensuring that the software can handle its intended workload without failure.
-
Compliance Testing: Ensures the software meets all relevant regulatory and industry standards, focusing on safety, quality, and reliability requirements specific to medical devices.
Medical device software testing follows a rigorous methodology that includes planning, requirement analysis, test case development, execution of tests, and thorough documentation throughout the testing cycle. This methodology is designed to identify and address any defects or anomalies in the software architecture, code, or performance before the device reaches the market, thereby ensuring the safety and efficacy of medical devices. The process involves a combination of automated and manual testing techniques and requires a deep understanding of both the technical and regulatory aspects of medical device development.
What are common medical device vulnerabilities?
Common medical device vulnerabilities encompass a range of issues that can compromise the safety, privacy, and effectiveness of medical devices. These vulnerabilities are often related to software flaws, outdated operating systems, or insecure interfaces, which cyber attackers can exploit to gain unauthorized access, steal sensitive data, or disrupt device functionality. Some of the most prevalent vulnerabilities include:
- Insecure Network Connections: Many medical devices connect to healthcare networks via Wi-Fi or Bluetooth, making them susceptible to eavesdropping or unauthorized access if they are not properly secured.
- Outdated Software and Firmware: Devices running on outdated software or firmware are vulnerable to known exploits that have not been patched. This includes operating systems that are no longer supported by their vendors.
- Weak Authentication and Authorization Controls: Insufficient authentication mechanisms can allow unauthorized users to gain access to medical devices, potentially leading to misuse or the alteration of critical healthcare information.
- Lack of Encryption: Failure to encrypt sensitive data both at rest and in transit can expose patient health information (PHI) and other confidential data to interception and misuse.
- Third-Party Software Components: The use of vulnerable third-party software components can introduce additional risks, as device manufacturers may not always regularly update or patched these components.
- Configuration and Customization Errors: Improper configuration or customization of medical devices can leave them open to attacks. This includes default passwords never changed or security features that are disabled for convenience.
- Physical Security: Physical access to medical devices can also pose a threat, especially if devices are not adequately secured within the healthcare facility, allowing for tampering or theft.
Addressing these vulnerabilities requires a comprehensive cybersecurity strategy that includes regular software updates and patches, strong encryption methods, robust authentication and authorization controls, and vigilant monitoring of network connections. Additionally, collaboration between device manufacturers, healthcare providers, and cybersecurity professionals is essential to ensure the ongoing protection of medical devices against emerging threats.
FAQs
What is an SPDF in medical device cybersecurity?
An SPDF (Secure Product Development Framework) is a repeatable process to integrate security into every stage of the medical device lifecycle. It includes security risk management, design reviews, secure coding practices, security verification, and postmarket workflows.
How does the FDA view cybersecurity for medical devices?
The FDA emphasizes a total product lifecycle approach to medical device cybersecurity, requiring manufacturers to address security from design through postmarket. This includes proactive risk management, strong security controls, and plans for vulnerability management and updates as detailed in the February 3, 2026 final guidance.
Why is threat modeling important for medical devices?
Threat modeling is crucial because it identifies potential attack paths and patient impacts, allowing manufacturers to derive specific security requirements and controls. A strong threat model ensures that security efforts are focused on the most relevant risks.
What is an operational SBOM?
An operational SBOM (Software Bill of Materials) is a machine-readable list of all software components used in a medical device, continuously updated and monitored for new vulnerabilities. It enables rapid identification and disposition of newly disclosed vulnerabilities, supporting an effective postmarket program.
Does the FDA require penetration testing for medical devices?
The FDA's February 3, 2026 final guidance on premarket cybersecurity does not explicitly mandate penetration testing. However, it expects verification and validation activities commensurate with risk, which may include penetration testing for critical interfaces or high-risk devices to demonstrate security effectiveness.
How do medical device manufacturers manage third-party software risk?
Manufacturers manage third-party software risk by establishing intake requirements for suppliers, controlling changes to components, verifying security when components are updated, and documenting rationale for component selection. Continuous SBOM monitoring is essential for tracking vulnerabilities in third-party software.
Sources & references
Primary sources cited in this article. Links open in a new tab.
- modern FDA expectations- U.S. FDA