
Updated December 27, 2025
Modern medical devices are increasingly reliant on complex software to deliver safe and effective care. While software drives innovation, it also introduces new risks — particularly cybersecurity threats that can impact patient safety, regulatory compliance, and brand reputation.
IEC 62304, the internationally recognized standard for medical device software lifecycle processes, provides a structured framework for developing, maintaining, and retiring medical device software. When applied effectively, it not only ensures functional quality but also strengthens cybersecurity by embedding secure development practices into every stage of the lifecycle.
For manufacturers, aligning with IEC 62304 is a practical and effective way to meet the FDA’s 2025 Cybersecurity Guidance, the EU MDR, and other global requirements, while protecting patient safety.
What Is IEC 62304?
IEC 62304 is the internationally recognized standard that defines the software development lifecycle (SDLC) for medical device software. It outlines the processes that manufacturers should have in place to develop, maintain, and control software used in or as a medical device.
IEC 62304 covers key lifecycle processes, including:
- Development – Planning, requirements, architecture and design, implementation, integration, and verification
- Maintenance – Updates, patches, and bug fixes are released after the device is on the market
- Risk Management – Identifying, analyzing, and controlling software-related risks, typically in coordination with ISO 14971
- Configuration Management – Ensuring software integrity, version control, and full traceability across requirements, code, and tests
- Problem Resolution – Systematically handling anomalies, defects, and field issues
The standard also introduces software safety classes (A, B, C) based on the potential harm that software failures could cause. Higher classes (e.g., Class C) require more rigorous controls and documentation.
While IEC 62304 was not created as a cybersecurity standard, its structured, lifecycle-focused approach makes it an ideal foundation for integrating security into medical device software development. When combined with an SPDF (Secure Product Development Framework) and ISO 14971 risk management, IEC 62304 helps manufacturers:
- Build cybersecurity controls into the SDLC
- Generate evidence for FDA and EU MDR submissions
- Maintain secure, traceable software over the entire device lifecycle
Why IEC 62304 Matters for Cybersecurity
Regulators, including the FDA and EU authorities, now explicitly expect cybersecurity to be part of a device’s overall assessment of safety and effectiveness. For medical device software, this means that security cannot be an afterthought—it must be built into the IEC 62304 software lifecycle from the outset.
By embedding cybersecurity into IEC 62304 processes, manufacturers can:
- Reduce exploitable vulnerabilities
Capture security requirements alongside functional requirements, design with least privilege and secure architectures, and apply secure coding practices as part of the standard 62304 development workflow. - Verify security controls through rigorous testing
Treat authentication, encryption, logging, and update mechanisms as software items that require formal verification, integration testing, and (where appropriate) penetration testing—traced back to IEC 62304 work products. - Maintain secure operation via timely updates and patches
Use IEC 62304 maintenance and problem resolution processes to manage vulnerability remediation, regression testing, and controlled deployment of security patches over the device’s lifetime. - Demonstrate regulatory compliance during reviews and audits
Show regulators and auditors that cybersecurity risk controls are built into the same documented SDLC that already supports your safety and performance claims, rather than existing in a separate, ad-hoc “security track.”
📌 Blue Goat Cyber Insight
Adding cybersecurity late in development almost always leads to costly redesigns, schedule slips, and uncomfortable review questions. Using IEC 62304 as the backbone for “security by design” enables you to integrate cybersecurity with ISO 14971 and your Secure Product Development Framework, ensuring that security decisions are made when they are most effective and cost-efficient—not at the end, when changes are most detrimental.
Integrating Cybersecurity into IEC 62304 Processes
Here’s how IEC 62304 can be adapted to build strong cybersecurity into your medical device software lifecycle:
1. Secure Requirements Definition
Capture cybersecurity requirements alongside functional requirements in your IEC 62304 documentation. Specify needs such as authentication, authorization/RBAC, encryption (in transit and at rest), logging, time sync, update mechanisms, and performance constraints when security features are active. Ensure that each security requirement is traceable to hazards outlined in ISO 14971 and to corresponding verification tests.
2. Threat Modeling in Design
During architecture and design, perform structured threat modeling to identify attack vectors, trust boundaries, and high-value assets. Incorporate mitigations directly into the software architecture (e.g., segmented services, least privilege, secure communications) and document these design decisions as part of your IEC 62304 design outputs.
3. Secure Coding Practices
Adopt recognized secure coding standards (such as MISRA C, CERT C, OWASP) and build them into your development procedures. Require security-focused code reviews, static analysis, and clear handling of input validation, error handling, and crypto use. Treat secure coding as a standard 62304 activity, not a separate “side process.”
4. Security Verification & Validation
Extend IEC 62304 verification and validation to explicitly cover security controls. This can include static application security testing (SAST), dynamic analysis (DAST), fuzzing, and targeted penetration testing of critical interfaces (wireless, APIs, cloud services). Trace these tests back to your cybersecurity requirements, providing clear evidence for the FDA and notified bodies.
5. Maintenance & Patch Management
Use IEC 62304 maintenance and problem resolution processes to manage vulnerability handling. Define procedures for monitoring SBOM components for new CVEs, assessing risk, developing and testing patches, and deploying updates safely and securely. Ensure that these activities are linked to ISO 14971 risk management and your Secure Product Development Framework (SPDF).
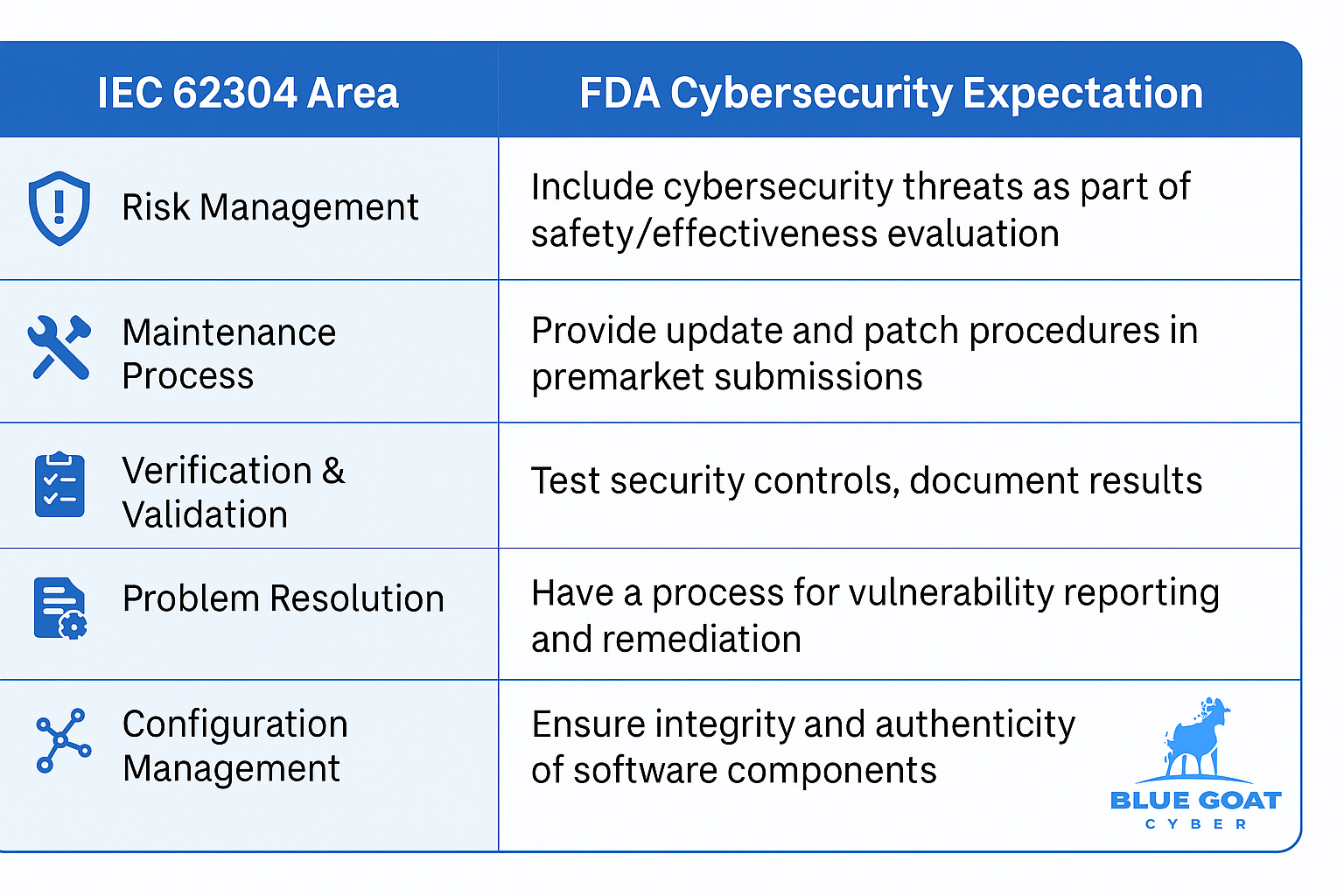
How IEC 62304 Aligns with FDA Cybersecurity Guidance
Case Study: Securing a Class II Connected Device
A mid-sized manufacturer approached Blue Goat Cyber while preparing an FDA premarket submission for a Class II diagnostic device with wireless connectivity.
Challenges Identified
- No formal process for secure software updates
- Missing SBOM for third-party component tracking
- Inconsistent secure coding practices
- Weak verification of authentication and encryption features
Blue Goat Cyber’s Solution
- Conducted a gap assessment against IEC 62304 and FDA guidance
- Added cybersecurity requirements to design documentation
- Built a complete SBOM and integrated it into development workflows
- Introduced SAST, DAST, and penetration testing
- Developed and validated a rapid patch deployment process
Results
- Reduced vulnerability patch time from 8 weeks to 3 weeks
- Improved FDA reviewer feedback due to strong cybersecurity integration evidence
- Increased trust from hospital procurement teams
IEC 62304 Cybersecurity Integration Checklist
Use this checklist to ensure your medical device software lifecycle meets IEC 62304 and modern cybersecurity expectations:
✅ Requirements: Document functional and security requirements
✅ Design: Perform threat modeling and specify security architecture
✅ Implementation: Apply secure coding standards and automated code scanning
✅ Verification: Conduct SAST, DAST, and penetration testing
✅ Maintenance: Maintain SBOM, monitor vulnerabilities, deploy timely patches
✅ Problem Resolution: Implement a vulnerability disclosure process
✅ Configuration Management: Verify software authenticity and integrity
📌 Tip: Keep this checklist as a living document to adapt to evolving threats and regulations.
How Blue Goat Cyber Can Help
At Blue Goat Cyber, we help medical device manufacturers implement IEC 62304-compliant cybersecurity practices that satisfy FDA, EU MDR, and other global requirements. Our services include:
- Gap assessments and remediation planning
- SBOM creation and vulnerability monitoring
- Pre-submission compliance documentation
- Postmarket cybersecurity maintenance strategies
Your device’s security depends on more than just its code — it depends on your process. Contact us today to ensure both are secure, compliant, and ready for the market.
IEC 62304 FAQs
IEC 62304 is an international standard that defines the software development lifecycle for medical device software, covering planning, development, risk management, maintenance, and problem resolution.
While not a dedicated cybersecurity standard, IEC 62304 requires risk management processes that can and should include cybersecurity threats. Integrating security into the software lifecycle aligns with FDA expectations.
The FDA’s 2025 guidance expects manufacturers to integrate cybersecurity into design, development, and maintenance processes. IEC 62304 provides a recognized framework for meeting those expectations.
IEC 62304 is widely recognized by global regulators and often required for market access, especially for devices with software components. While not a legal requirement in all regions, compliance is highly recommended.
IEC 62304 focuses on the software development lifecycle, while ISO 14971 addresses overall medical device risk management. Together, they ensure both software and safety risks are effectively managed.
A Software Bill of Materials (SBOM) helps track and manage third-party components, which is critical for patching vulnerabilities and maintaining security postmarket — both important for IEC 62304 alignment.
By establishing documented, validated update and patch deployment processes, verifying authenticity of software, and continuously monitoring for vulnerabilities.
Short answer: higher-class software typically needs more rigor—stronger traceability, tighter verification evidence, and more disciplined change control for security fixes.
In the same places as other requirements: software requirements, architecture/design outputs, verification plans, and traceability—so security isn’t “extra,” it’s built into lifecycle work products.
By mapping threats → potential harms/clinical impacts → risk controls, and documenting the rationale. This keeps the link to safety clear without abusing terminology.
SOUP (third-party/legacy software) is often where vulnerabilities show up first. SBOM + monitoring helps you identify affected versions fast and manage patching and residual risk.
Threat-model-driven testing, SAST/DAST where relevant, fuzzing for parsers/protocols, and penetration testing on critical interfaces—plus clear traceability back to security requirements.
Use a defined maintenance workflow: triage → risk decision → implementation → verification/regression → controlled release → documentation updates (including SBOM and traceability).
It’s how you prevent “mystery builds” in the field: version control, build integrity, release baselines, and ensuring the right software (and security fixes) ship to the right customers.
Usually: missing traceability, weak security requirements, unclear update mechanism evidence, outdated SBOMs, and testing that doesn’t map to the threat model.
It’s a smart add. A defined intake/triage path for vulnerability reports supports problem resolution and postmarket security expectations.
Yes—when your cybersecurity evidence is traceable, test-backed, and integrated into lifecycle documentation (instead of being a separate “security packet” with gaps).
