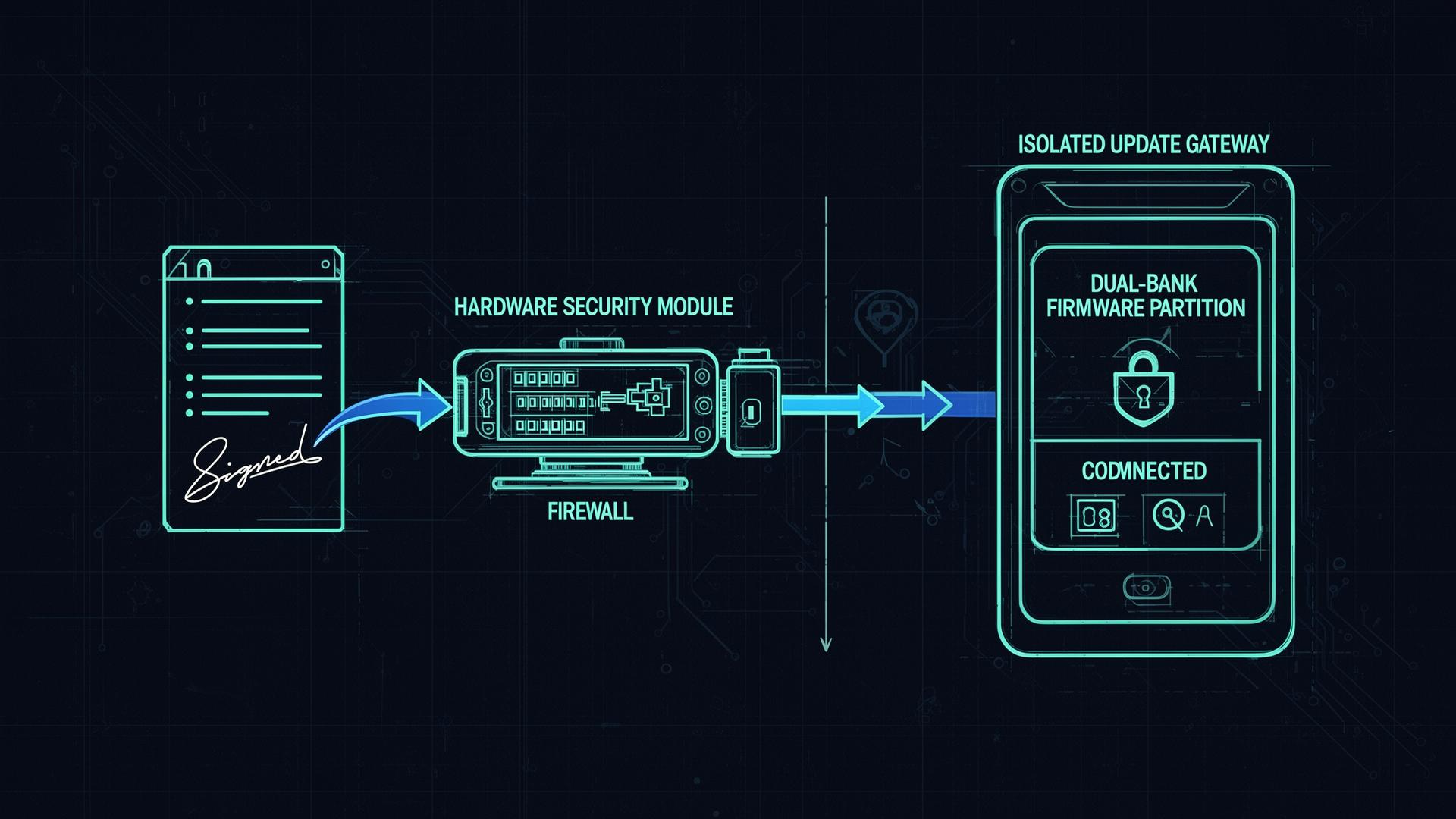
Secure Update Infrastructure for Medical Devices: A Safety-Critical Subsystem
How to design, isolate, and defend the update channel for connected medical devices - signed manifests, dual-bank A/B, rollback protection, HSM-backed signing, TUF/Uptane, and what the FDA expects in the submission.
Read article