Picture a seasoned enterprise CISO handed responsibility for a fleet of connected infusion pumps and networked imaging systems. They reach for familiar tools: EDR agents, patch managers, a NIST-aligned risk framework, and an annual compliance audit cycle. Within weeks, the tools don’t install. The patches won’t deploy without clinical validation cycles that take months. The FDA documentation requirements look nothing like any compliance program they’ve run before. The playbook doesn’t work here.
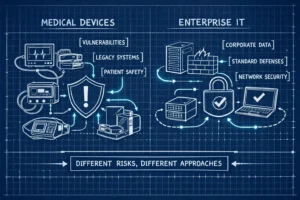
Medical device security versus enterprise security isn’t just a difference in tools or frameworks, it’s a difference in fundamental operating rules, risk consequences, and regulatory obligations. Both disciplines share some vocabulary: vulnerabilities, threat models, access controls. But applying enterprise methodology to medical devices doesn’t just fall short; it creates real gaps in safety, documentation, and regulatory compliance. This is precisely why firms like Blue Goat Cyber exist, built exclusively around medical device cybersecurity, because general IT security expertise doesn’t transfer cleanly into this space. Read more on the topic of Traditional vs Medical Device Cybersecurity to understand why a different playbook is required.
The sections below break down the principal technical, regulatory, and operational differences between medical device security and enterprise security so security leaders can make better decisions about how they approach device security, and understand what kind of expertise that actually requires.
Patient Safety Changes the Entire Risk Calculus in Medical Device Security vs Enterprise Security
Enterprise security failures cost money, reputation, and data. Medical device security failures can cost lives. A compromised infusion pump doesn’t just expose records; it can alter drug dosing. A ransomware infection that locks imaging systems delays diagnosis for patients who can’t afford that delay. These aren’t theoretical edge cases. They’re the reason cybersecurity is treated as a safety function in medical devices, not just an IT function. For a deeper look at how safety and security interact in medical devices, see Medical Device Safety vs Security Risks.
This reframes availability as a clinical obligation. In enterprise IT, availability is an SLA concern. On a ventilator or cardiac monitor, downtime is a patient harm event. The standard CIA triad still applies, but the weighting shifts sharply: availability and integrity dominate because they map directly to patient outcomes, while confidentiality takes a secondary role to keeping devices operational and accurate.
The FDA ties cybersecurity explicitly to device safety and effectiveness under the FD&C Act, not to data protection alone. Every security decision, authentication tradeoffs, update timing, network segmentation strategy, gets evaluated against potential clinical impact. That constraint doesn’t exist anywhere in enterprise security architecture, and it changes nearly everything downstream.
FDA Regulatory Obligations That Enterprise Compliance Doesn’t Touch
Enterprise IT frameworks like NIST CSF and ISO 27001 are advisory. They represent best practices organizations choose to adopt for certification or operational maturity. FDA cybersecurity requirements for cyber devices are binding for market access. Without compliant documentation, a device doesn’t reach patients.
Premarket submissions, whether 510(k), PMA, or De Novo, must include threat models, penetration testing evidence, vulnerability assessments, a Cybersecurity Management Plan, and a Software Bill of Materials. The SBOM requirement stands out: it must enumerate every software component in the device, commercial, open-source, and off-the-shelf, with version and supplier metadata for vulnerability tracking. Enterprise IT has no equivalent hard requirement tied to market entry.
The Feb 2026 updated FDA guidance expands this scope further, covering servers, cloud infrastructure, and third-party integrations that affect patient safety, while requiring standardized documentation sets submitted through eSTAR. Postmarket obligations are equally demanding. Manufacturers must maintain continuous vulnerability monitoring, operate coordinated vulnerability disclosure programs, and issue patches for critical vulnerabilities within 60 days. The FDA requires cybersecurity testing and reevaluation every six months until end-of-support. Compare that to the annual audit cycles of SOC 2 or ISO 27001, which are certification-oriented and not tied to patient safety obligations. EU MDR imposes parallel requirements under Annex I GSPR, creating a second compliance layer for manufacturers seeking CE marking. None of this maps to anything enterprise security teams typically operate.
Hardware and OS Constraints: Where Device Security vs Enterprise Security Diverges Most Sharply
Most enterprise endpoint security tools make three core assumptions: a general-purpose OS, available compute resources, and the ability to install agents. Medical devices invalidate all three. They run lightweight real-time embedded operating systems or proprietary firmware, prioritize stability over updates, and carry MCUs with limited CPU headroom, minimal memory, and, in implantable or portable devices, strict battery constraints. There’s no standard API surface for agents. There’s no supported patch channel. Active monitoring processes would compete for resources the device needs for clinical function.
Unpatched Vulnerabilities and Legacy Exposure
Standard network inventory scanners miss devices running proprietary operating systems entirely. According to Claroty’s 2023 research, 53% of networked medical devices carry known unpatched vulnerabilities precisely because standard patch management can’t reach them, and 60% of hospital-connected devices are end-of-life and unpatchable by any conventional method. For enterprise security teams trained on active endpoint management, passive network-based monitoring is often the only viable detection posture, and that’s a fundamentally different security model.
Cryptographic Constraints in Embedded Devices
Cryptography faces the same resource limitations. Enterprise endpoints support full PKI, large key sizes, and frequent certificate rotations. Medical devices with low-power MCUs and battery-dependent designs need lighter approaches: AES symmetric encryption, elliptic curve cryptography for its efficiency at smaller key sizes, hardware security modules to offload crypto from the main processor, and Cryptographic Key Management Services to enforce policy across software components. Key management must be designed into device architecture from the start. The FDA requires manufacturers to justify cryptographic tradeoffs in submissions, which means ad hoc retrofits don’t satisfy regulatory scrutiny even if they work technically. Many embedded systems constraints are also documented in clinical- and engineering-focused studies of embedded device security challenges.
Lifecycle Management and the Patching Trap
Enterprise IT hardware refreshes on 3, 5 year cycles. Software patches deploy quarterly or monthly. Medical devices run for 10, 20 years on the same firmware, sometimes longer. That gap alone creates a structural problem with no clean enterprise analog.
Patching a medical device isn’t like pushing a Windows update. Every patch requires engineering analysis, bench testing, clinical validation, and in many cases, FDA notification or recertification, depending on the change’s scope. By the time a vulnerability patch clears that process, months have passed. In enterprise IT, that lag is a risk management failure. In medical devices, it’s the expected operating condition, and security strategy has to account for it from the beginning. Practical approaches to medical device patch management emphasize compensating controls, staged validation, and coordinated disclosure to minimize clinical disruption.
According to the Cynerio 2022 State of IoMT Cybersecurity Report, 73% of hospital-connected devices are classified as legacy systems with limited or no vendor support for security updates. Enterprise security teams often treat a legacy device as a manageable edge case. In healthcare environments, it’s the majority of the fleet. Securing legacy devices requires network segmentation to limit exposure, compensating controls at the network layer, and postmarket monitoring programs built around the reality that endpoint-centric tools won’t reach these devices. Blue Goat Cyber’s legacy device security work addresses exactly this scenario for cleared devices, applying controls that don’t require firmware access or disrupt clinical operation.
Why Generalist Firms Create Risk: Medical Device Security vs Enterprise Security Expertise
Most enterprise cybersecurity firms know how to secure infrastructure, applications, and endpoints. Very few have navigated an FDA premarket submission, structured an SBOM to FDA standards, or run penetration testing against embedded device firmware. These are specialized skills that don’t develop from general IT security work.
A generalist firm applying enterprise methodology to medical device security doesn’t merely fall short, it produces documentation gaps, misaligned risk models, and regulatory deficiencies that delay or block clearance. FDA cybersecurity deficiencies are among the most common reasons 510(k) submissions stall. The firms that consistently avoid them are those who work exclusively in this space and understand where reviewers look, what documentation needs to demonstrate, and how to structure submissions that don’t invite additional information requests.
Blue Goat Cyber is built around exactly this model. The firm works exclusively with medical device manufacturers and MedTech companies, navigating FDA cybersecurity requirements, from SPDF development and threat modeling through penetration testing and eSTAR-ready submission documentation. The team has handled hundreds of FDA submissions, which means they recognize deficiency patterns before documentation is filed, not after a rejection lands. Their full-lifecycle approach integrates security at design, carries it through premarket documentation, tests it against FDA expectations, and maintains it postmarket through ongoing vulnerability monitoring and patching programs. For additional background on premarket considerations and developer-focused guidance, see Medical Device Cybersecurity Insights.
Organizations that recognize the distinction between medical device security and enterprise IT security need a partner who has operated within that difference for years. Learning on the engagement, in a domain where documentation errors cost months and security failures cost lives, isn’t an acceptable option.
The Distinction That Matters in Medical Device Security vs Enterprise Security
Patient safety stakes, FDA premarket and postmarket obligations, hardware and OS constraints, and lifecycle complexity aren’t variations on enterprise IT security. They’re a separate discipline with its own frameworks, standards, tooling, and expertise requirements. The tools and processes that protect enterprise environments don’t map onto medical devices without significant adaptation, and in many cases they fail entirely.
Whether you’re a CISO at a health system, a regulatory affairs lead at a device manufacturer, or a VP of IT at a MedTech company, understanding the difference between medical device security and enterprise security is the first step to making better decisions. The second step is building a program, or finding a partner, with the right kind of expertise for this specific domain.
If you recognize the gap and need a partner who works exclusively in medical device cybersecurity, reach out to Blue Goat Cyber. Medical device security demands specialized expertise, not an enterprise security playbook with a healthcare header on it.
Related: The Rising Tide of Cyber Threats in Medical Devices: Understanding the Risks
