Hashing shows up everywhere in modern medical device ecosystems: firmware/software updates, digital signatures, integrity checks, artifact storage in CI/CD, API tokens, and (sometimes) password storage. When hashing is used correctly, it helps you prove integrity—“this is the exact file/config/data we intended.”
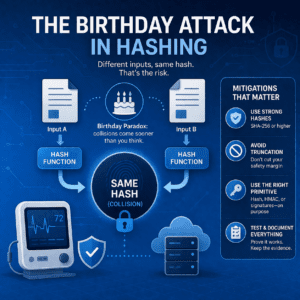
But there’s a catch: even strong hash functions can produce collisions in theory. The birthday attack is the reminder that collisions become likely much sooner than most people intuitively expect—and that design choices like hash truncation or legacy algorithms can quietly reduce safety margins.
What is a birthday attack in hashing?
A birthday attack is a collision-finding strategy based on the birthday paradox. The attacker doesn’t need to match a specific hash; they just need any two different inputs that produce the same hash output.
The key takeaway is the scaling: for an n-bit hash output, generic collision-search effort is roughly on the order of 2^(n/2). In plain language, collision resistance is “about half the hash length.” That’s why modern security designs commonly use SHA-256 (and above) for collision-sensitive use cases.
Why MedTech teams should care (even if you “use SHA-256”)
Birthday-attack thinking matters because medical device organizations often introduce collision risk indirectly—especially across manufacturing, test, and release tooling. Common culprits include:
- Truncating hashes (e.g., keeping only 64 bits “to save space”)—this drastically reduces collision resistance.
- Legacy algorithms (MD5, SHA-1) lingering in update tools, scripts, or integrations.
- Using a plain hash where you needed a keyed construction (e.g., SHA-256 when you really needed an HMAC to prevent forgery).
- Using hashes as “unique IDs” without considering scale over years of devices, builds, and artifacts.
Where collision risk shows up in medical device ecosystems
1) Firmware/software updates
Updates commonly use hashes for integrity checks and as part of signing workflows. Collision resistance matters because integrity and authenticity are only as strong as the weakest link in the update chain.
2) Digital signatures and signed artifacts
Signatures typically operate over a hash of a message/artifact. If a weak hash is used in a signing workflow, collisions can create confusion about “what was actually signed.”
3) CI/CD artifact registries and SBOM workflows
CI/CD systems use hashes for deduplication, integrity verification, and artifact tracking. If you truncate, downgrade, or reuse hashes across different purposes, you can create subtle integrity gaps that are painful to defend during incident response.
Mitigation checklist: reducing birthday-attack exposure
1) Use modern, approved hash functions
For collision-sensitive use cases, favor the SHA-2 family (e.g., SHA-256/384/512). NIST provides authoritative references for approved hash functions and standards:
2) Don’t truncate hashes unless you’ve quantified the tradeoff
Truncation explicitly trades away collision resistance. If you need ~128-bit collision resistance, don’t truncate below a 256-bit output without a strong, documented rationale and a quantified risk argument.
3) Use the right primitive for the job
- Integrity check (non-adversarial): a hash may be sufficient (still use modern algorithms).
- Integrity check (adversarial): use signatures or HMAC depending on the trust model.
- Password storage: use a purpose-built password hashing approach (not a fast general hash).
4) Treat crypto choices as part of your SPDF
Capture crypto requirements early (approved algorithms, truncation rules, key management boundaries, update signing design, logging) and verify them with test evidence. This aligns with secure-by-design expectations in FDA’s current premarket cybersecurity guidance:
FDA: Cybersecurity in Medical Devices (Feb 2026)
How to document hashing decisions for FDA-facing cybersecurity evidence
For reviewer-friendly documentation, aim for a clean thread from risk → requirement → design → verification. For hashing/collision risk, that usually includes:
- Architecture: where hashes are used (updates, signing, artifact integrity, logs, APIs).
- Risk analysis: what a collision could enable (integrity confusion, acceptance of wrong artifacts, audit gaps).
- Requirements: approved algorithms, “no truncation” rules, when to use HMAC/signatures.
- Verification: tests confirming algorithms and configurations in shipped builds and toolchains.
- Lifecycle plan: how you’ll handle algorithm transitions (e.g., deprecations) without disrupting fielded devices.
Internal resources (Blue Goat Cyber)
- FDA Premarket Cybersecurity Services
- Medical Device Threat Modeling Services
- Medical Device Cybersecurity Penetration Testing
- FDA Medical Device Cybersecurity 2026: 524B eSTAR Checklist
Key takeaways
- A birthday attack targets hash collisions; collisions become likely sooner than most people expect.
- Collision resistance is roughly half the hash output length—choose output sizes accordingly.
- Truncation and legacy hashes (MD5/SHA-1) are common sources of avoidable risk.
- Use the correct primitive: hash vs HMAC vs signatures, based on the threat model.
- Document design choices and verification evidence to strengthen FDA-facing cybersecurity credibility.
FAQs
How many tries does it take to find a hash collision?
In the generic case, the work grows roughly with the square root of the output space. For an n-bit hash, collision-search effort is on the order of 2^(n/2).
Does SHA-256 “prevent” birthday attacks?
Birthday attacks reflect collision probability—you don’t eliminate the math. But SHA-256 provides strong practical collision resistance for modern threat models when implemented correctly and not truncated.
Why is SHA-1 considered risky?
SHA-1 is no longer recommended for collision-sensitive security uses due to demonstrated collision feasibility and modern deprecation guidance.
Is truncating a hash ever acceptable?
Sometimes, but only with a documented security-strength rationale. Truncation reduces collision resistance quickly, so quantify the tradeoff and document why it’s acceptable for the specific use case.
Where do hash collisions matter most in medical devices?
Anywhere integrity and authenticity decisions depend on hashes—especially firmware/software updates, signing workflows, and artifact integrity in build and release systems.
Book a Discovery Session
If you want a quick assessment of where hashing choices create hidden risk (firmware updates, CI/CD, signing workflows, cloud APIs) and how to document fixes for FDA review, we can help.
Conclusion
The birthday attack isn’t a niche academic idea—it’s a reminder that collision probability is a design constraint. For MedTech teams, the practical path is straightforward: use modern approved hash functions (e.g., SHA-256+), avoid truncation without a quantified rationale, choose the right primitive (hash vs HMAC vs signatures), and verify the implementation in shipped builds and toolchains. Document those decisions with traceability and test evidence, and you reduce real-world integrity risk while strengthening your FDA-facing cybersecurity story.
Related: Key Exchange in Medical Device Cybersecurity: TLS, PKI, and Keys
