Published: January 6, 2024 · Last reviewed: May 1, 2026
Updated April 8, 2026
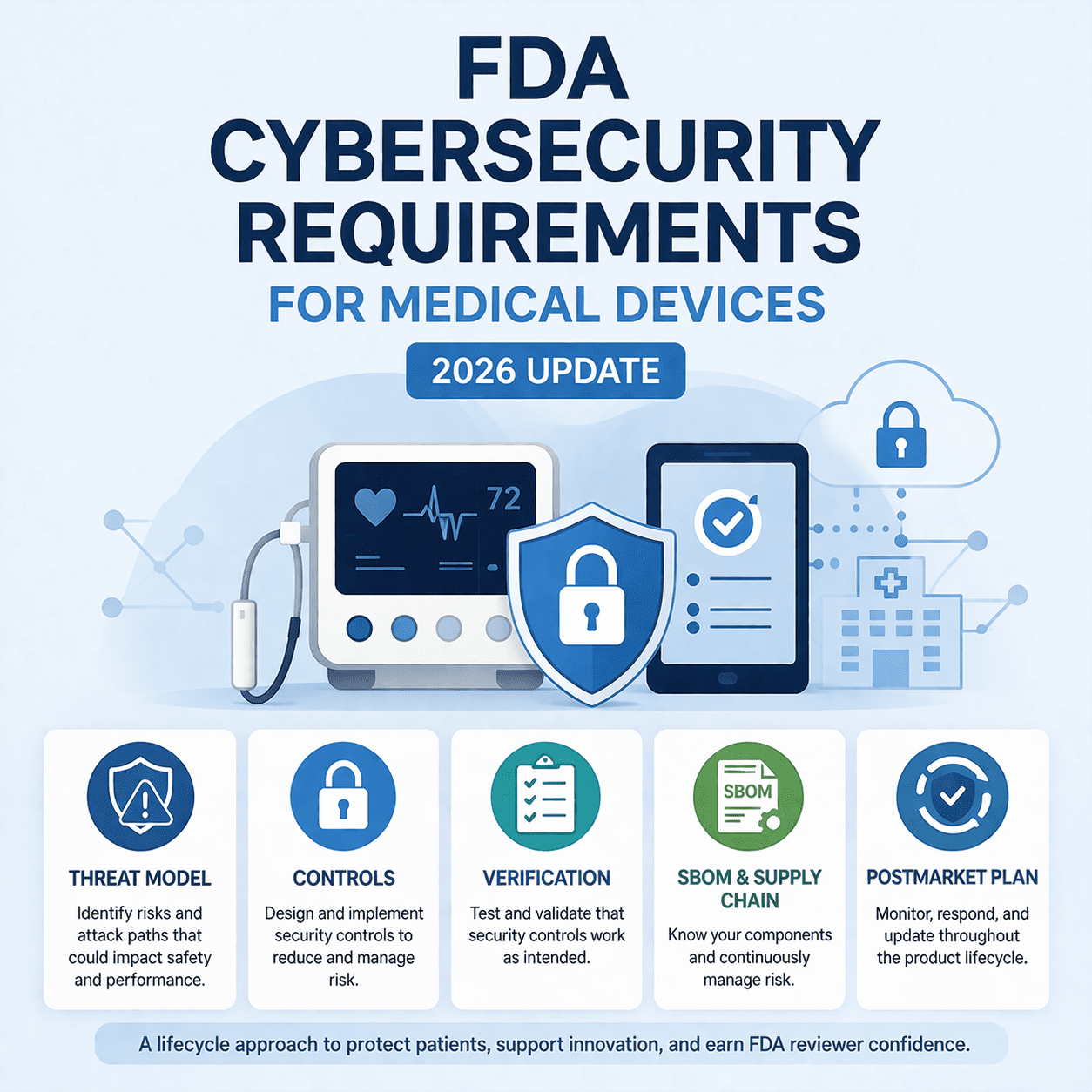
If your medical device has software, connectivity, or a supporting ecosystem (mobile app, cloud services, update server, service tools), the FDA expects cybersecurity to be treated as part of safety and effectiveness, not as a last-minute document. In practice, the fastest path through review is a package that’s easy to follow: a clear system description, a realistic threat model, defensible controls, and test evidence that ties it all together.
This 2026 update reflects two changes that matter right now: the FDA’s updated premarket cybersecurity guidance, issued on February 3, 2026 ( webpage, PDF), and the Quality Management System Regulation (QMSR), effective on****February 2, 2026 ( FDA overview). Together, they push cybersecurity deeper into your quality system and lifecycle processes.
If you need a fully managed, eSTAR-ready package, our FDA Premarket Cybersecurity Services team can help. If you’re building it internally, keep reading.
The most useful mental model: build an evidence package, not a “cybersecurity section”
Most delays come from a simple problem: reviewers can’t quickly find or trust the story. The fix is a package with traceability:
- System reality: what the full device system is (device + apps + cloud + update infrastructure)
- Threat model: realistic misuse/abuse cases that map to patient impact and system impact
- Security requirements and controls: what you built to reduce risk, and where it’s enforced
- Verification evidence: what you tested, why you tested it, and what you did with findings
- Lifecycle readiness: SBOM, vulnerability monitoring, coordinated disclosure, and update delivery
If you want a practical “what goes where” organizer that mirrors eSTAR structure, see FDA Medical Device Cybersecurity 2026: 524B eSTAR Checklist.
Step 1: Confirm whether Section 524B applies and document your rationale
Section 524B (“Ensuring Cybersecurity of Medical Devices”) applies to “cyber devices.” In plain English, if your device includes software and connects (directly or indirectly) to networks, apps, cloud services, update servers, or other systems that affect cybersecurity, assume 524B is relevant unless you can justify otherwise. The FDA’s Cybersecurity in Medical Devices FAQs are a practical place to start, and the statutory expectations matter because missing 524B elements can trigger administrative friction under FDA’s Refuse-to-Accept policy ( Federal Register notice).
What 524B is really asking you to prove is capability, not paperwork:
- You can find problems: monitoring, intake, triage, and coordinated disclosure (see our CVD page for what a practical intake path looks like).
- You can fix problems safely: secure update design, validation, communications, and predictable patch delivery.
- You understand your supply chain: an SBOM that’s accurate, versioned, and operational.
Step 2: Anchor cybersecurity in SPDF and QMSR processes
The FDA’s 2026 guidance explicitly reinforces a lifecycle approach using a Secure Product Development Framework (SPDF). You don’t have to use the FDA’s terminology, but your evidence should show repeatable processes that operate inside your quality system under QMSR ( FDA QMSR overview) and align with global best practice, such as the NIST Secure Software Development Framework (SP 800-218) and the IMDRF cybersecurity principles (N60).
Internally, we break this down in SPDF and FDA Cybersecurity Requirements and the QMSR implications in What the FDA’s QMSR Means for Cybersecurity.
Step 3: The 2026 reviewer-ready cybersecurity package checklist
This is the package that most consistently reduces questions for 510(k), De Novo, and PMA submissions. Scale depth to risk and connectivity, but keep the structure consistent.
1) System scope and cybersecurity context (show the real system)
Start with a system description that matches real deployment. The FDA’s guidance talks about the “medical device system” for a reason. A cloud portal compromise can be just as clinically disruptive as a device compromise.
Include:
- Device + accessories + mobile apps + cloud services + APIs + update servers + service tools
- Interfaces and protocols (Wi-Fi, Ethernet, BLE, USB, serial, NFC, cellular, proprietary radios)
- Environment of use (home, clinic, hospital enterprise network, remote monitoring)
- Data and control flows with trust boundaries (one diagram that’s readable in 60 seconds)
If you want a deeper “deliverables view,” our 18 cybersecurity deliverables breakdown helps teams map artifacts to submission expectations.
2) Threat modeling tied to clinical and system impact
A strong threat model is not a generic framework pasted into a table. It’s a set of realistic abuse cases that map to safety and effectiveness. Examples that reviewers immediately understand:
- Unauthorized therapy parameter changes through weak authorization
- Alarm suppression or delayed alerting due to availability attacks
- Update tampering that alters behavior or disables safety functions
- Credential compromise leading to service tool or remote management abuse
- Third-party component vulnerabilities that create systemic exposure
If you need help building this quickly, our medical device threat modeling services are designed to produce FDA-ready diagrams, misuse cases, and traceability without turning into a months-long exercise.
3) Cybersecurity risk assessment that aligns with safety risk management
The FDA’s cybersecurity review is not a privacy-only lens. Reviewers want to see how cyber risk can create hazardous situations, especially through integrity and availability loss. Many teams use ISO 14971 as the backbone ( ISO 14971:2019 standard page) and then layer security-specific guidance, such as AAMI TIR57 for security risk management and AAMI TIR97 for postmarket security risk management.
Make assumptions explicit. A large percentage of “cybersecurity deficiencies” are really “your assumptions are unclear” problems.
4) Security requirements and traceability
If you do one thing to reduce FDA questions, do this: create traceability from threats to requirements to controls to tests to results. It turns a pile of artifacts into a story.
- Threats/risks → security requirements
- Requirements → controls and design decisions
- Controls → verification activities (tests, analyses, reviews)
- Verification → results summary + supporting evidence attachments
Traceability is also where QMSR helps. Your requirements, V&V, supplier controls, and change control all become easier to defend when cybersecurity lives inside your quality system ( QMSR overview).
5) Security architecture evidence (show where controls are enforced)
For connected devices, reviewers want to know where controls live and what stops compromise from crossing boundaries. A practical structure is to describe controls using categories that map cleanly to the FDA’s guidance and common security frameworks, such as NIST SP 800-53:
- Authentication and authorization: user roles, privileged paths, service access
- Cryptography and key management: data in transit and at rest, secure storage
- Integrity: signed updates, secure boot (where applicable), configuration integrity
- Logging and detection: what you log, where it’s stored, how it’s used
- Resilience and recovery: safe failure behavior, restoration priorities, backup/restore
- Secure updates: delivery method, integrity checks, rollback behavior, field constraints
For devices that rely heavily on device-to-cloud communications, TLS configuration is an easy place to be specific and credible, using references like NIST SP 800-52 (TLS guidance) for defensible choices.
6) Cybersecurity verification and validation (prove it works)
Tool output alone is not evidence. Evidence is scope, method, pass/fail criteria, results, and what you did with findings. A reviewer-friendly V&V package includes:
- Security test plan mapped to threats and requirements
- Vulnerability testing summary with disposition and rationale
- Penetration testing or adversarial testing summary when appropriate
- Remediation and retest evidence for anything you fixed
- Negative tests for failure modes that commonly drive questions (cert validation, auth boundaries, update integrity)
For many manufacturers, a scoped engagement with FDA-compliant vulnerability and penetration testing closes the loop between “we think we’re secure” and “we can prove it.”
7) SBOM and third-party software evidence (make it operational)
The FDA’s guidance leans hard into third-party component management. An SBOM is not a checkbox, it’s how you keep pace with new vulnerabilities. Use authoritative sources like NIST’s National Vulnerability Database (NVD) and prioritize what’s actively exploited using CISA’s Known Exploited Vulnerabilities (KEV) Catalog.
What “good” looks like:
- Machine-readable SBOM (SPDX or CycloneDX are common)
- SBOM tied to each software release (not a one-time export)
- Component lifecycle context (maintained vs end-of-support, and what you’ll do about it)
- Monitoring and triage workflow, including out-of-cycle response for high-risk issues
If you need SBOM help that’s aligned to FDA and eSTAR packaging, see FDA-compliant SBOM services for MedTech and the practical format discussion in Navigating FDA’s SBOM requirements.
8) Postmarket cybersecurity plan (critical under 524B)
The FDA wants to see how you’ll stay safe after launch. Your plan should cover intake, triage, remediation, and communications, as well as how updates will be delivered safely. Many teams align postmarket processes with AAMI TIR97 and secure development maturity models such as OWASP SAMM, especially when the product includes cloud services and APIs.
Internal guidance: Postmarket cybersecurity management requirements and our managed service offering at FDA postmarket cybersecurity management services.
9) Cybersecurity transparency and labeling
Labeling is where manufacturers often lose credibility. Reviewers want customers to be able to deploy and maintain devices securely. That means clear guidance for secure configuration, network requirements, patching behavior (including rollback), and where users can get cybersecurity information. FDA’s emphasis on transparency is one reason cybersecurity labeling has become a frequent focus area ( FDA medical device cybersecurity labeling requirements).
10) Interoperability and API security (don’t ignore the ecosystem)
Modern devices act as nodes in larger systems. If your ecosystem includes APIs, cloud portals, or integrations, reviewers may effectively be asking: “Is the whole system safe?” A simple way to avoid blind spots is to sanity-check against the OWASP API Security Top 10 (2023) and show how you prevent high-impact issues like broken object level authorization and weak auth patterns in remote management workflows.
Step 4: Make it eSTAR-friendly (packaging matters)
Even strong cybersecurity work gets slowed down when evidence is hard to locate. FDA’s eSTAR program pushes structured responses. “eSTAR-friendly” typically means:
- Your attachments match questions with obvious file names.
- You include a one-page “reviewer roadmap” that points to each artifact.
- Your diagrams, threat model, and tests tell the same story.
If you’re responding to a deficiency letter or AI request and need to move fast, our FDA cybersecurity deficiency response service is built for rapid remediation plus clean, submission-ready narrative updates.
Common gaps that trigger FDA cybersecurity questions
- Generic threat model: no device-specific misuse cases, no trust boundaries, no clinical impact linkage.
- SBOM without a program: no monitoring plan, unclear ownership, no end-of-support strategy.
- Testing that isn’t traceable: results exist, but reviewers can’t see what risks were tested and why.
- Update story is vague: no integrity chain, rollback behavior, or field constraints.
- Labeling is thin: customers can’t deploy or maintain the device securely from your guidance.
Key takeaways
- In 2026, the FDA expects a lifecycle story, supported by the Feb 3, 2026, premarket cybersecurity guidance and reinforced by QMSR (effective Feb 2, 2026).
- The fastest way to reduce questions is traceability: threats → requirements → controls → tests → results.
- SBOM only helps if it’s operational, backed by monitoring sources like NVD and CISA KEV.
- Packaging matters. A reviewer roadmap and consistent diagrams routinely reduce review cycles.
FAQs
Do all 510(k) submissions need cybersecurity documentation?
If your device has software and cybersecurity risk, expect to provide cybersecurity evidence. The depth should scale with connectivity, complexity, and potential impact to safety and effectiveness, consistent with the FDA’s 2026 guidance.
What’s the fastest way to reduce the risk of a cybersecurity deficiency?
Provide a reviewer roadmap plus traceability. Most deficiencies are “missing story” problems, not “one missing control” problems. If you’re already in review, deficiency response support can help you close gaps quickly and present clean evidence.
Is an SBOM required under Section 524B?
For cyber devices, 524B includes SBOM expectations. The FDA’s FAQ page is a helpful starting point, and the 2026 guidance explains how SBOM should be used as part of lifecycle risk management.
Do we need penetration testing?
For many connected devices, yes. The key is to justify scope based on threats and to present results clearly with remediation and retest evidence. If you need an FDA-aligned report structure, see medical device penetration testing services.
How should we handle cybersecurity after clearance?
Run a repeatable postmarket program: monitor, intake, triage, remediate, communicate, and keep documentation current as the product evolves. FDA expects lifecycle capability, and guidance like AAMI TIR97 is a solid reference for postmarket security risk management.
Need a 2026-ready cybersecurity package?
If you want a second set of eyes on your package before submission, or you want it fully managed end-to-end, we can help. Start with our FDA premarket cybersecurity services, or if you’re already shipping and need lifecycle coverage, see FDA postmarket cybersecurity management services.
Related: Medical Device Cybersecurity: A Complete Lifecycle Guide
The Med Device Cyber Podcast
Follow Blue Goat Cyber on Social
Sources & references
Primary sources cited in this article. Links open in a new tab.
- webpage- U.S. FDA
- PDF- U.S. FDA
- FDA overview- U.S. FDA
- Cybersecurity in Medical Devices FAQs- U.S. FDA
- NIST Secure Software Development Framework (SP 800-218)- NIST
- IMDRF cybersecurity principles (N60)- IMDRF
- ISO 14971:2019 standard page- ISO
- AAMI TIR57- AAMI
- AAMI TIR97- AAMI
- NIST SP 800-53- NIST
- NIST SP 800-52 (TLS guidance)- NIST
- NIST’s National Vulnerability Database (NVD)- NIST
- CISA’s Known Exploited Vulnerabilities (KEV) Catalog- CISA
- OWASP SAMM- OWASP
- OWASP API Security Top 10 (2023)- OWASP
- eSTAR program- U.S. FDA