Published: February 19, 2024 · Last reviewed: May 1, 2026
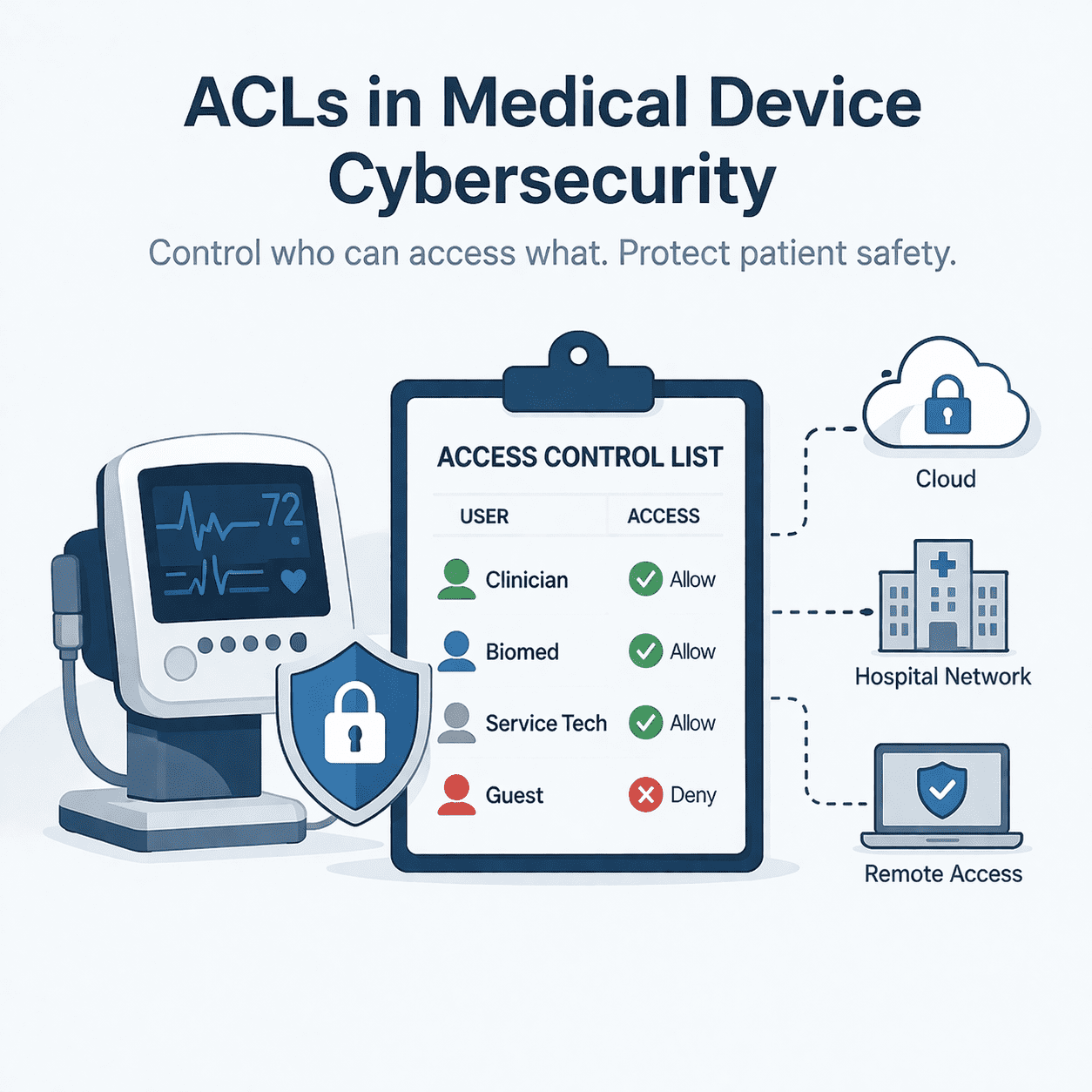
Access Control Lists (ACLs) are fundamental for medical device cybersecurity, defining who can access resources and what actions are permitted. Implementing ACLs across device OS, applications, network, and cloud layers helps enforce authorization and least privilege, reducing the attack surface and preventing unsafe misuse. Proper deployment, verification, and ongoing management of ACLs are critical for demonstrating compliance with the FDA's cybersecurity expectations for medical devices.
What is an ACL?
An Access Control List (ACL) is a set of rules that defines who can access a resource and what actions they can take. A resource might be a file, process, API endpoint, database record, device function, or network service. Actions might include read, write, execute, configure, update, or administer.
In medical device environments, ACLs typically appear in multiple places:
- On-device OS and file system: controlling access to logs, configs, cryptographic material, update packages, and safety-critical data.
- Application layer: enforcing which roles can invoke commands (e.g., “calibrate,” “change dose limits,” “start remote session”).
- Network layer: firewall/router ACLs and segmentation rules restricting inbound/outbound traffic to required flows only.
- Cloud and APIs: API gateway policies, microservice rules, object storage policies, and IAM policies.
- Service and manufacturing tools: limiting who can run diagnostics, load firmware, or access factory/admin functions.
Why ACLs matter for medical device cybersecurity (and FDA expectations)
The FDA’s premarket cybersecurity guidance emphasizes cybersecurity as part of device safety and lifecycle risk management, including strong authentication/authorization, secure architecture, and evidence that controls are implemented and verified. ACLs are one of the most direct ways to enforce authorization and least privilege across the system.
Practically, well-designed ACLs help you:
- Reduce attack blast radius: limit lateral movement by blocking unnecessary ports, services, and commands.
- Prevent unsafe misuse: keep non-clinical or non-privileged users from changing safety-critical parameters.
- Support serviceability without overexposure: enable remote support and field service with tight boundaries and audit trails.
- Produce clearer submission evidence: map threats → requirements → controls → verification results with traceability.
For help building end-to-end cybersecurity evidence, see our FDA premarket cybersecurity services package.
ACLs vs RBAC vs ABAC: what’s the difference?
RBAC (Role-Based Access Control) defines access in terms of roles (e.g., Clinician, Biomed, Service Tech, Cloud Admin). ABAC (Attribute-Based Access Control) uses context and attributes (e.g., location, device state, time, patient context).
ACLs are often the enforcement mechanism that implements RBAC/ABAC decisions at a specific resource. In other words:
- RBAC/ABAC helps you decide who should be allowed.
- ACLs implement what is actually allowed at each control point.
If you’re working through roles and permission models, you may also like: Permissions vs Rights: Access Control for Medical Device Security.
Implementation playbook: ACLs that hold up in real device ecosystems
1) Start with the full system (not just the device)
Define the ecosystem: device, mobile/desktop app, cloud services, update infrastructure, customer network dependencies, service tooling, and any third-party components. This is the foundation for consistent ACLs and for meaningful threat modeling.
If you need a structured approach, our medical device threat modeling services focus on entry points, trust boundaries, and realistic abuse paths.
2) Define roles and service accounts that match real workflows
Medical devices usually require multiple “personas” beyond a simple admin/user split:
- Clinician / operator
- Biomed / hospital IT
- Field service (manufacturer)
- Manufacturing / provisioning
- Cloud operations / support
- Patient (where applicable)
Document what each role must do, and what it must never be allowed to do. Then implement that policy using ACLs at each enforcement point.
3) Identify safety-critical resources and “high consequence” actions
Not all access decisions are equal. Flag actions that could directly impact clinical performance or safety (e.g., therapy configuration, calibration, alarm thresholds, firmware updates). These should have stricter ACLs, stronger authentication, and stronger logging.
4) Place ACLs at multiple layers (defense in depth)
- Network ACLs: allow only required protocols/ports between defined endpoints (and deny everything else).
- OS/app ACLs: restrict local access to configs, secrets, logs, and privileged functions.
- API ACLs: enforce endpoint-level permissions and validate claims/roles server-side (never trust the client).
5) Design “break-glass” access without breaking your security model
Medical devices may require emergency access or contingency workflows. If you implement break-glass capabilities, make them deliberate and auditable:
- Time-bound elevation
- Strong authentication
- Just-in-time approvals (where feasible)
- High-fidelity logging and review triggers
6) Verify ACL behavior with testable evidence
Don’t stop at policy statements. Create verification that demonstrates:
- Denied actions are actually denied (negative testing)
- Allowed actions work reliably for intended roles
- Privilege escalation paths are blocked
- Logs capture who did what, when, and from where
Penetration testing can help confirm your ACLs behave under adversarial conditions. Learn more about our medical device penetration testing.
7) Operate the ACLs: audit, review, and update
ACLs fail in practice when they drift from reality. Build a lightweight operating rhythm:
- Periodic access reviews (especially privileged roles and service accounts)
- Timely deprovisioning and credential rotation
- Configuration change control for ACL rulesets
- Monitoring for abnormal access patterns
Common ACL pitfalls in medical device environments
- Over-permissive “temporary” rules that become permanent (e.g., broad network allows for troubleshooting).
- Shared accounts that destroy accountability and auditability.
- Device-to-cloud trust that’s too broad (services can access more than they need).
- Remote service pathways without tight scoping, logging, and disablement mechanisms.
- Inconsistent enforcement across device, app, and cloud (gaps attackers love).
What to include in your premarket submission (practical evidence)
When ACLs are a key control, your submission story is stronger when you can show traceability across:
- Architecture: where ACLs are enforced (device, network, cloud, APIs) and why those are the right control points.
- Risk management: threats/abuse cases that ACLs mitigate, tied to safety and security risks.
- Requirements: clear authorization requirements (who can do what) with rationale for least privilege.
- Verification: test cases (including negative tests) and supporting results.
- Postmarket readiness: plans to manage access changes over time and respond to vulnerabilities.
For broader context, reference:
- FDA: Cybersecurity in Medical Devices (Premarket Guidance)
- NIST SP 800-53 Rev. 5 (Security Controls)
- NIST SP 800-207 (Zero Trust Architecture)
Key Takeaways
- ACLs are one of the most direct ways to enforce authorization and least privilege in a medical device ecosystem.
- Implement ACLs at multiple layers: device OS/app, network, and cloud/API enforcement points.
- High-consequence actions (settings, calibration, updates) require tighter rules, stronger auth, and better logging.
- FDA-ready evidence comes from traceability: threats → requirements → ACL controls → verification results.
- ACLs are not “set and forget”-they need ongoing review, deprovisioning, and change control.
FAQs
Are ACLs required for FDA medical device cybersecurity?
FDA generally expects manufacturers to implement effective authorization and least-privilege controls appropriate to risk. ACLs are a common and practical way to enforce those decisions across device, network, and cloud components.
Where should ACLs be implemented in a connected medical device?
Usually in multiple places: on-device OS/app controls, network segmentation/firewall rules, and cloud/API policies. The goal is layered enforcement so one failure doesn’t expose the entire system.
How do ACLs relate to RBAC?
RBAC defines roles and the permissions they should have. ACLs often implement those permissions at the resource level (files, APIs, services, device functions).
How do you handle remote service access safely?
Use narrowly scoped service roles, time-bound access, strong authentication, and high-quality logging. Avoid permanent “wide open” rules created for troubleshooting.
What kind of testing supports ACL claims?
Include role-based functional tests, negative tests (prove denial), privilege escalation checks, and-where appropriate-penetration testing that validates ACL enforcement under adversarial conditions.
Book a Discovery Session
If you want help designing ACLs that are practical for real clinical workflows and produce strong submission evidence, we can help.
Conclusion
ACLs aren’t just a networking concept-they’re a concrete way to enforce authorization across the medical device lifecycle. When you treat ACLs as part of your secure architecture (not a last-minute configuration task), you reduce risk, improve auditability, and strengthen the credibility of your cybersecurity evidence.
Related: Medical Device Cybersecurity: A Complete Lifecycle Guide
Sources & references
Primary sources cited in this article. Links open in a new tab.