Shodan & Medical Devices: Exposing Healthcare Security Risks
Learn how Shodan exposes connected medical devices - and how manufacturers and hospitals can use it to identify risks, improve security, and meet FDA expectations.
Read articleEvery article in our archive in Primer.
Showing 12 of 127 articles in Primer · Page 10 of 11
Learn how Shodan exposes connected medical devices - and how manufacturers and hospitals can use it to identify risks, improve security, and meet FDA expectations.
Read article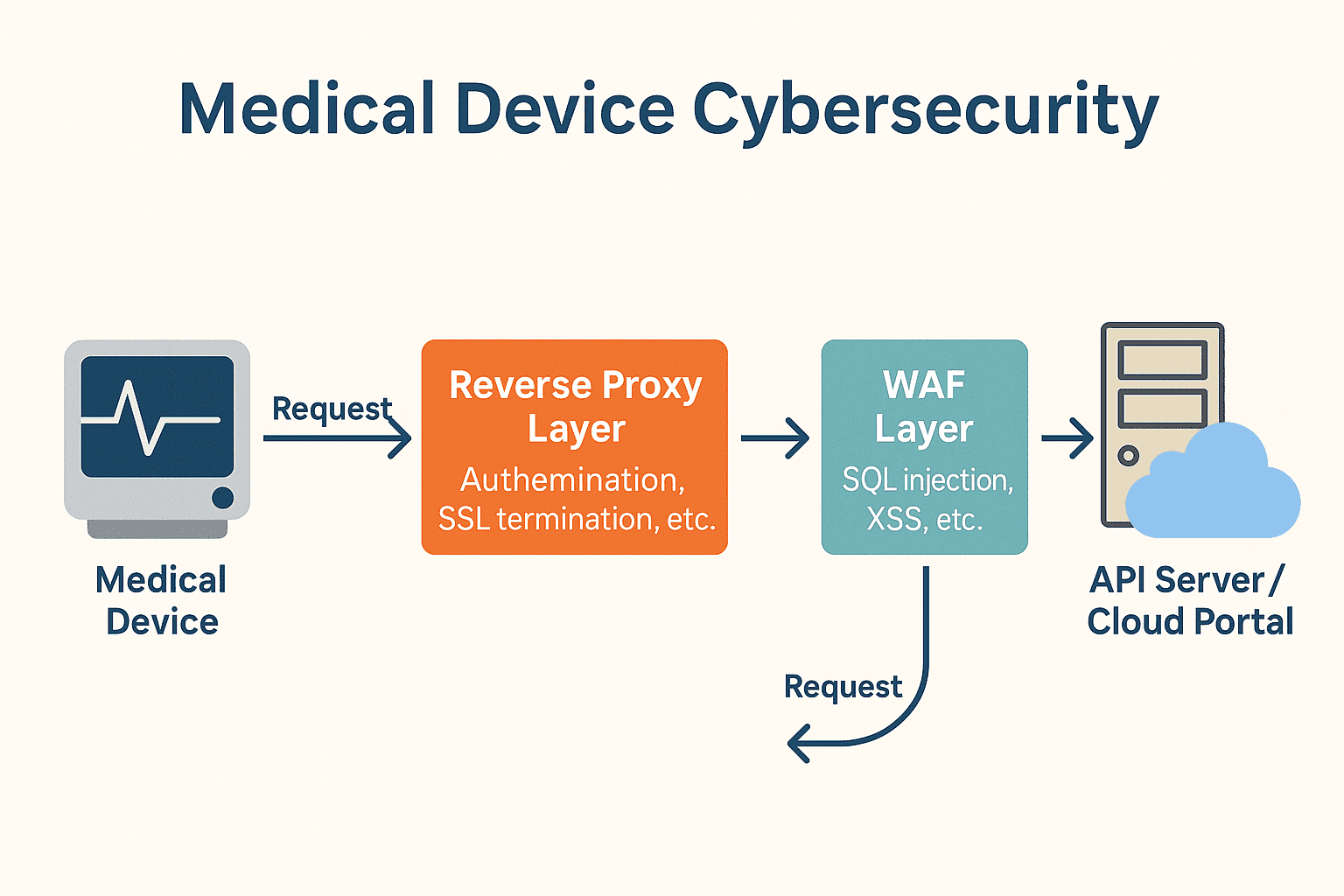
Protect medical devices with WAFs and reverse proxies. Learn the differences, use cases, and FDA-ready best practices for cybersecurity compliance.
Read article
A 10-point medical device cybersecurity assessment checklist to align with FDA guidance, manage risks, and protect patient safety.
Read article
Discover how emerging technologies are shaping the landscape of medical device cybersecurity.
Read article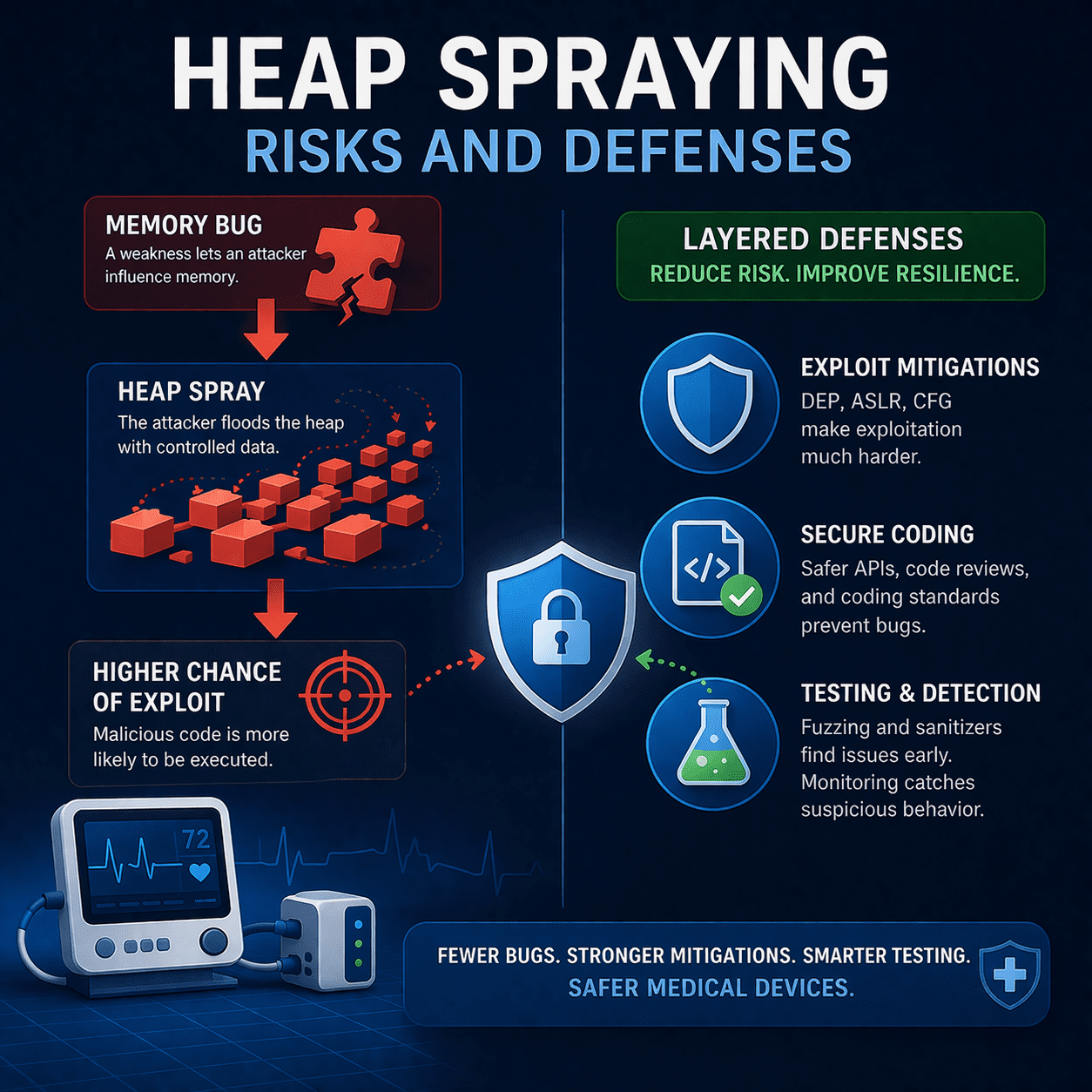
Heap spraying increases exploit reliability for memory bugs. Learn MedTech defenses: patching, mitigations, secure coding, fuzzing, and FDA-ready evidence.
Read article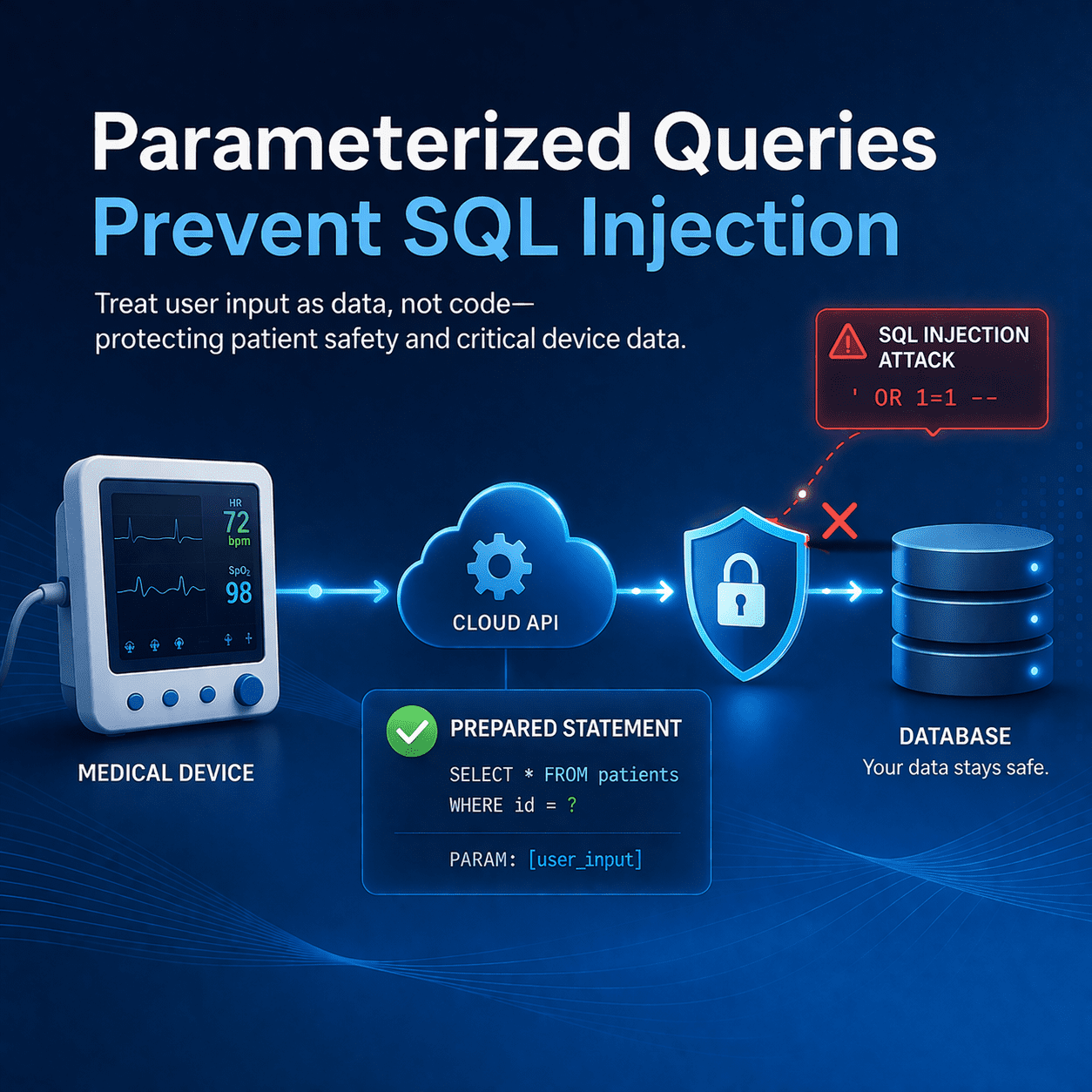
Stop SQL injection (CWE-89) in medical device software using parameterized queries, testing, and FDA-aligned secure development evidence.
Read article
Learn how to conduct a comprehensive medical device inventory to strengthen cybersecurity in healthcare settings.
Read article
Why IDS/IPS agents don’t work for medical devices and what FDA-aligned alternatives like segmentation, gateways, and monitoring mean for patient safety.
Read article
Learn how nonrepudiation in medical device cybersecurity protects patient safety, ensures data integrity, and aligns with FDA guidance.
Read article
Healthcare IoT and IoMT devices must be secured to avoid cybersecurity threats that could compromise patient safety and PHI.
Read article
Why medical device cybersecurity matters: protect patients, prevent disruptions, and meet FDA expectations with lifecycle security from design to postmarket.
Read article
In this post we're diving into a critical yet often shadowed aspect of healthcare cybersecurity – MedHacking and its various forms, including Medjacking
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.