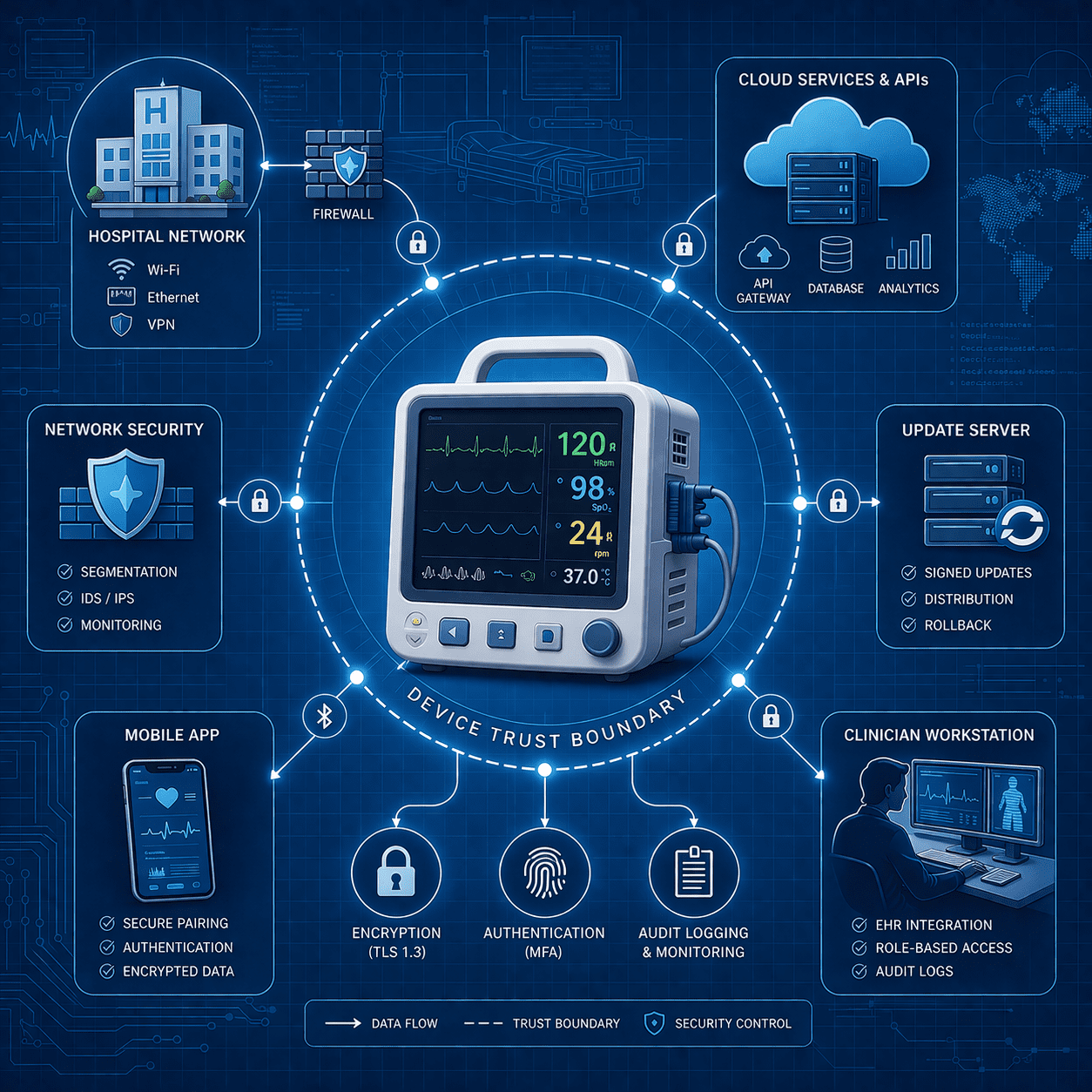
Security Architecture Diagrams for Medical Device Cybersecurity
Learn how security architecture diagrams support FDA-ready medical device cybersecurity, clarify trust boundaries, and reduce review questions.
Read articleEvery article in our archive in Primer.
Showing 12 of 127 articles in Primer · Page 8 of 11
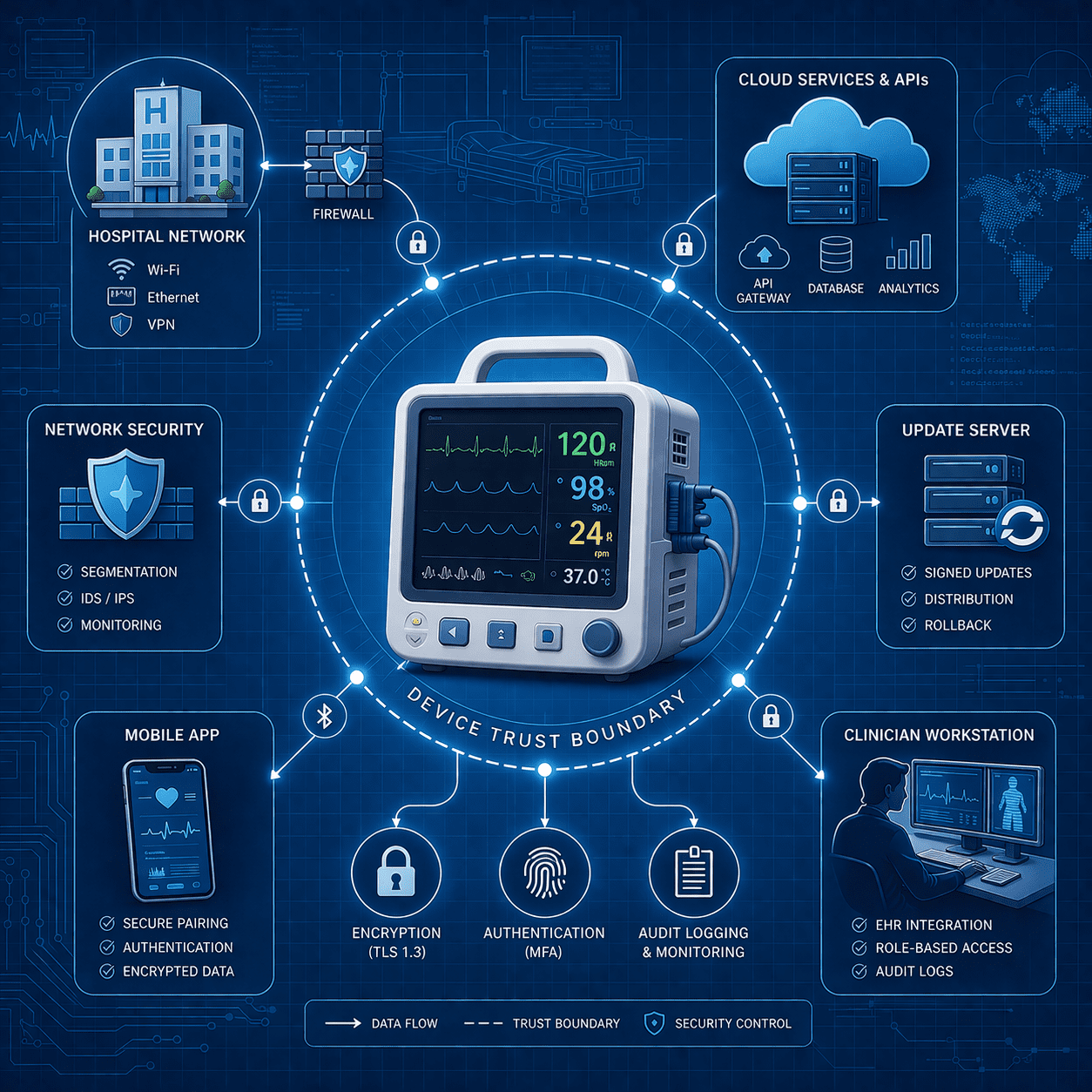
Learn how security architecture diagrams support FDA-ready medical device cybersecurity, clarify trust boundaries, and reduce review questions.
Read article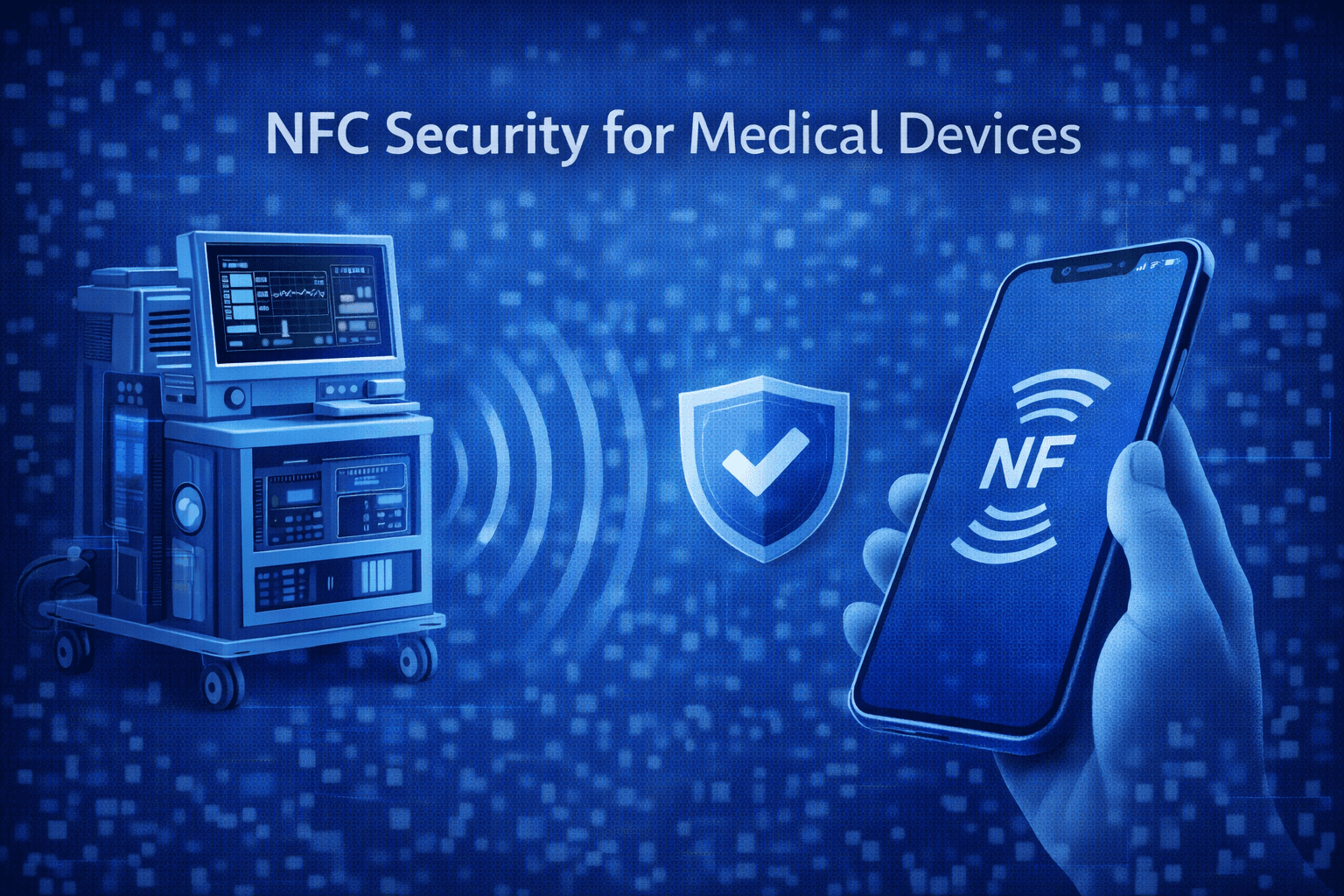
NFC security for medical devices: common threats like eavesdropping, relay, and tag tampering - plus practical mitigations for design, testing, and evidence.
Read article
Discover the innovative world of QIH devices in medical technology. Learn about their unique features, applications, and the potential impact on patient care.
Read article
Delve into the world of binary software composition analysis and its crucial role in medical device testing.
Read article
Discover everything you need to know about IRT medical devices in this comprehensive guide.
Read article
Uncover the significance of the CE marking in the world of medical devices.
Read article
Learn all about DICOM in medical devices with this comprehensive guide.
Read article
PACS systems handle protected health information across imaging workflows. Cybersecurity considerations for MedTech manufacturers integrating with PACS.
Read article
Learn what a write blocker is, when MedTech teams need one, and how it supports defensible evidence collection during device cyber incidents.
Read article
Steganography is a growing threat to medical devices. Learn how hidden code affects firmware, telemetry, and compliance - and how to defend against it.
Read article
Uncover the importance and implications of Software as a Medical Device (SaMD) in the healthcare industry.
Read article
Updated October 26, 2024 One of the hardest parts of the security process is the initial discovery phase of understanding what could go wrong. Cyber threats are constantly changing, with old attacks slowly becoming less common while new attacks rapidly pop up. Modern attack techniques target new tec
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.