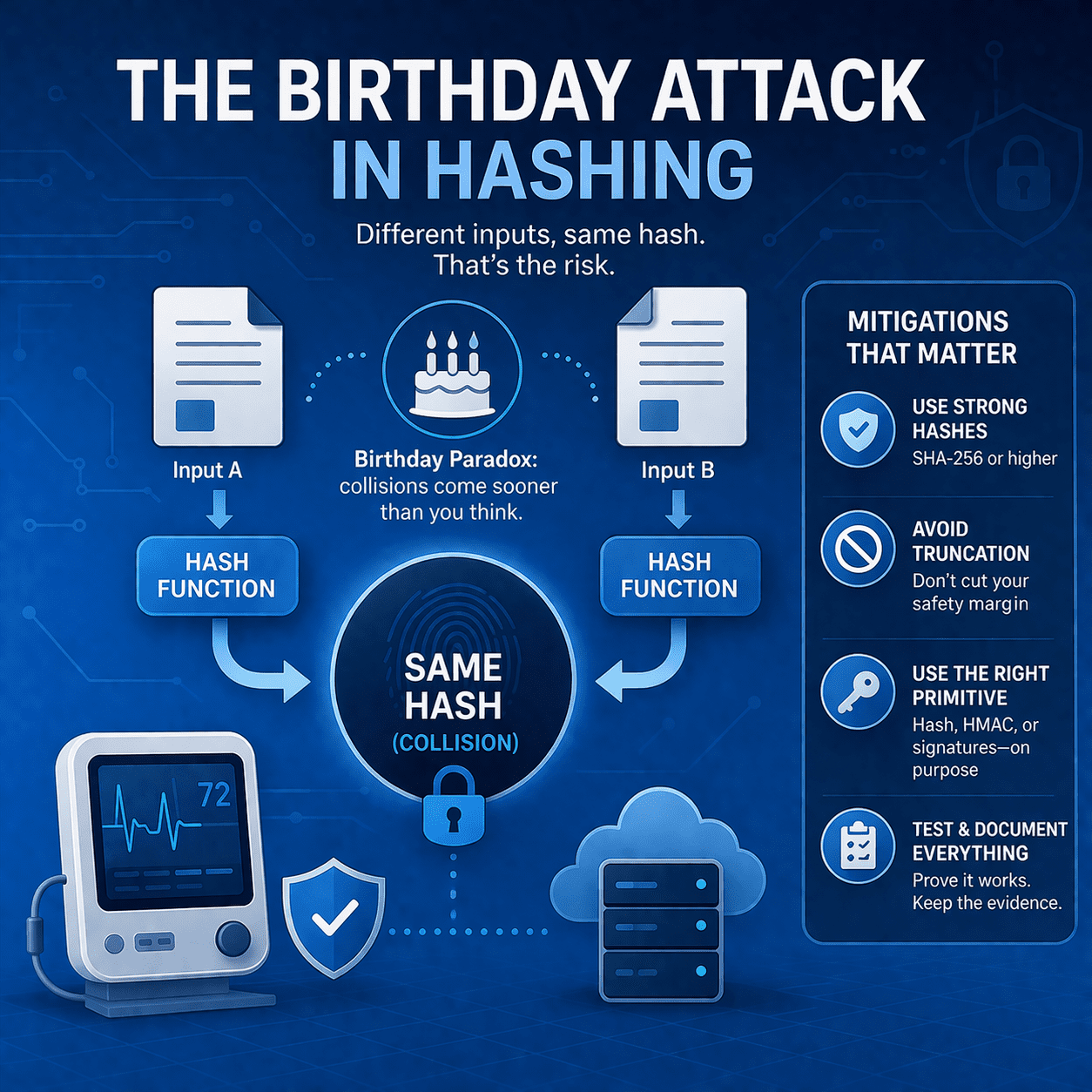
Preventing Hash Collision Risk in Medical Device Cybersecurity
Learn how birthday attacks exploit hash collision probability - and what MedTech teams should do (SHA-256+, signing, truncation rules, testing, evidence).
Read articleEvery article in our archive in Risk.
Showing 7 of 19 articles in Risk · Page 2 of 2
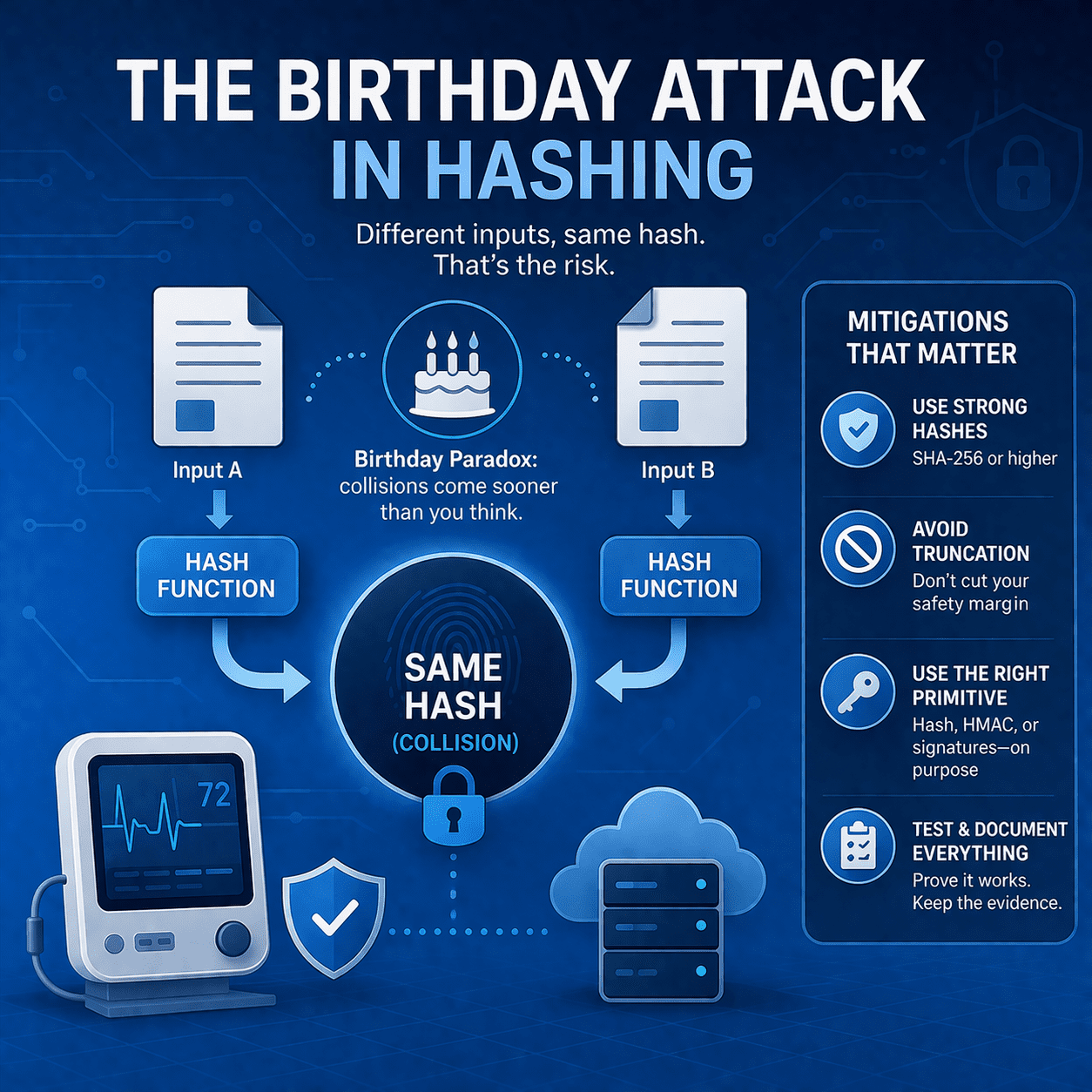
Learn how birthday attacks exploit hash collision probability - and what MedTech teams should do (SHA-256+, signing, truncation rules, testing, evidence).
Read article
Discover how to navigate the complexities of interoperable medical devices and effectively manage associated risks.
Read article
Discover how medical devices are meticulously designed with patient safety as the top priority.
Read article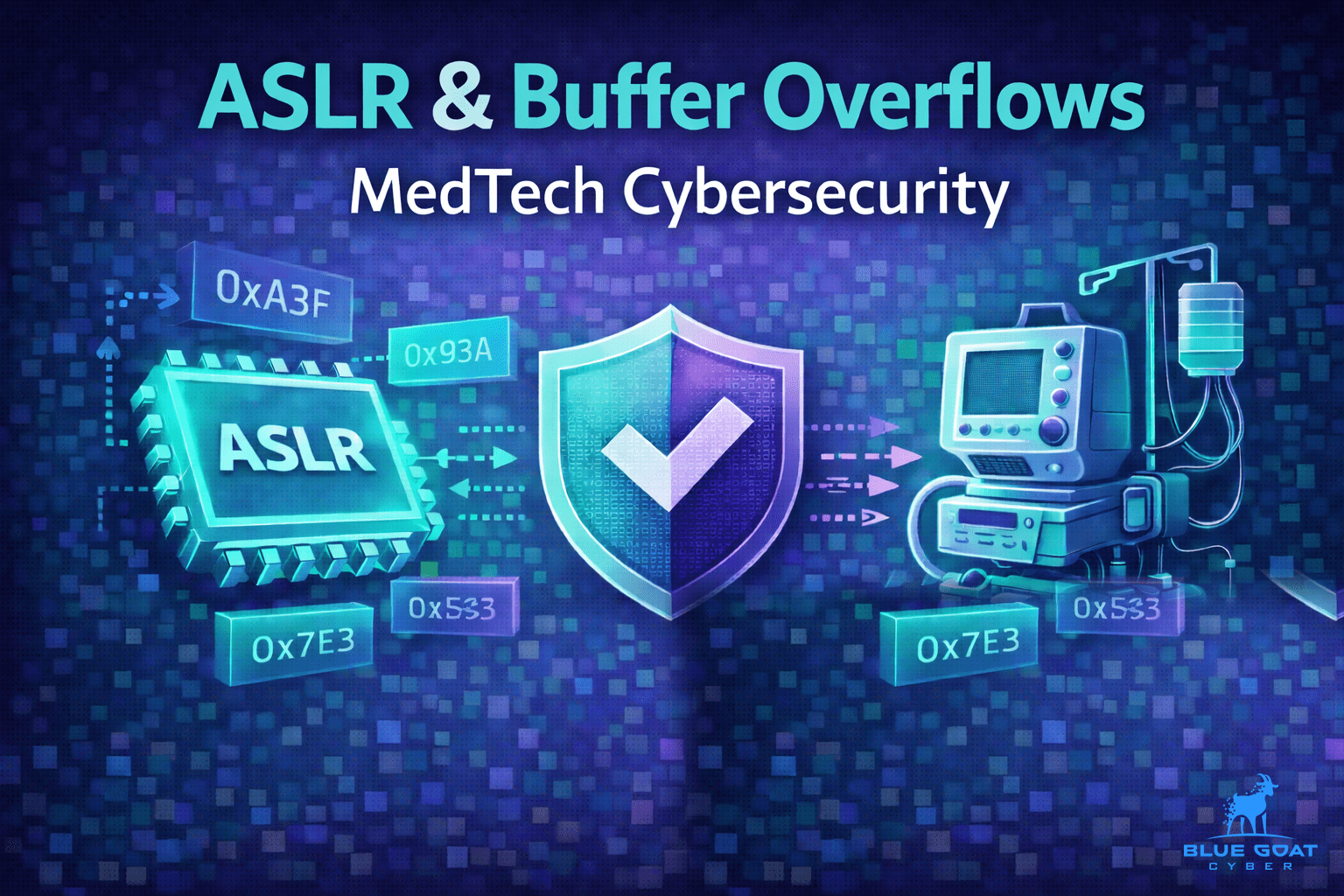
Learn how ASLR reduces buffer overflow impact, where it falls short, and practical controls MedTech teams can use to prevent memory corruption in devices.
Read article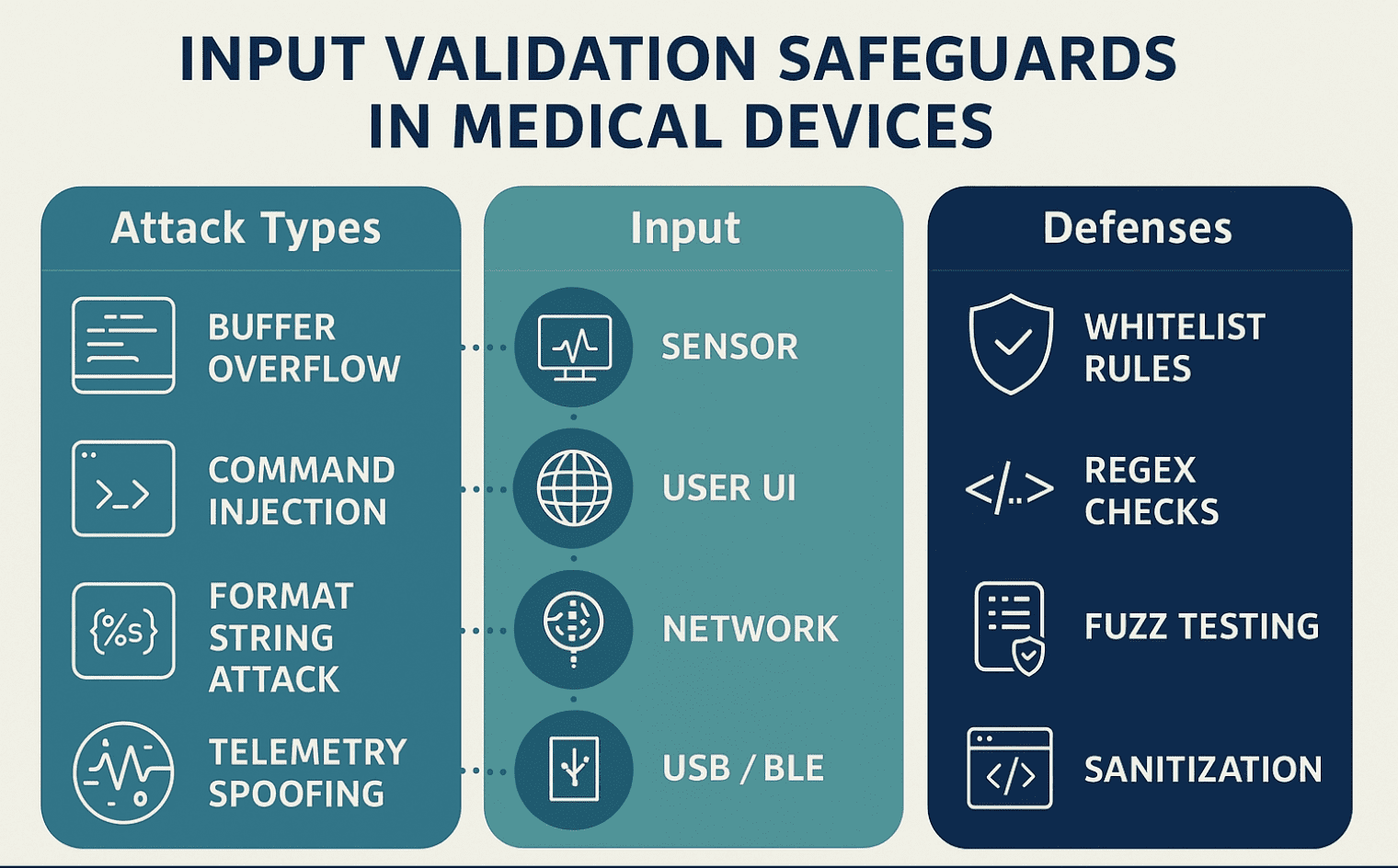
Learn how input validation in medical devices prevents buffer overflows, command injections, and supports FDA cybersecurity compliance.
Read article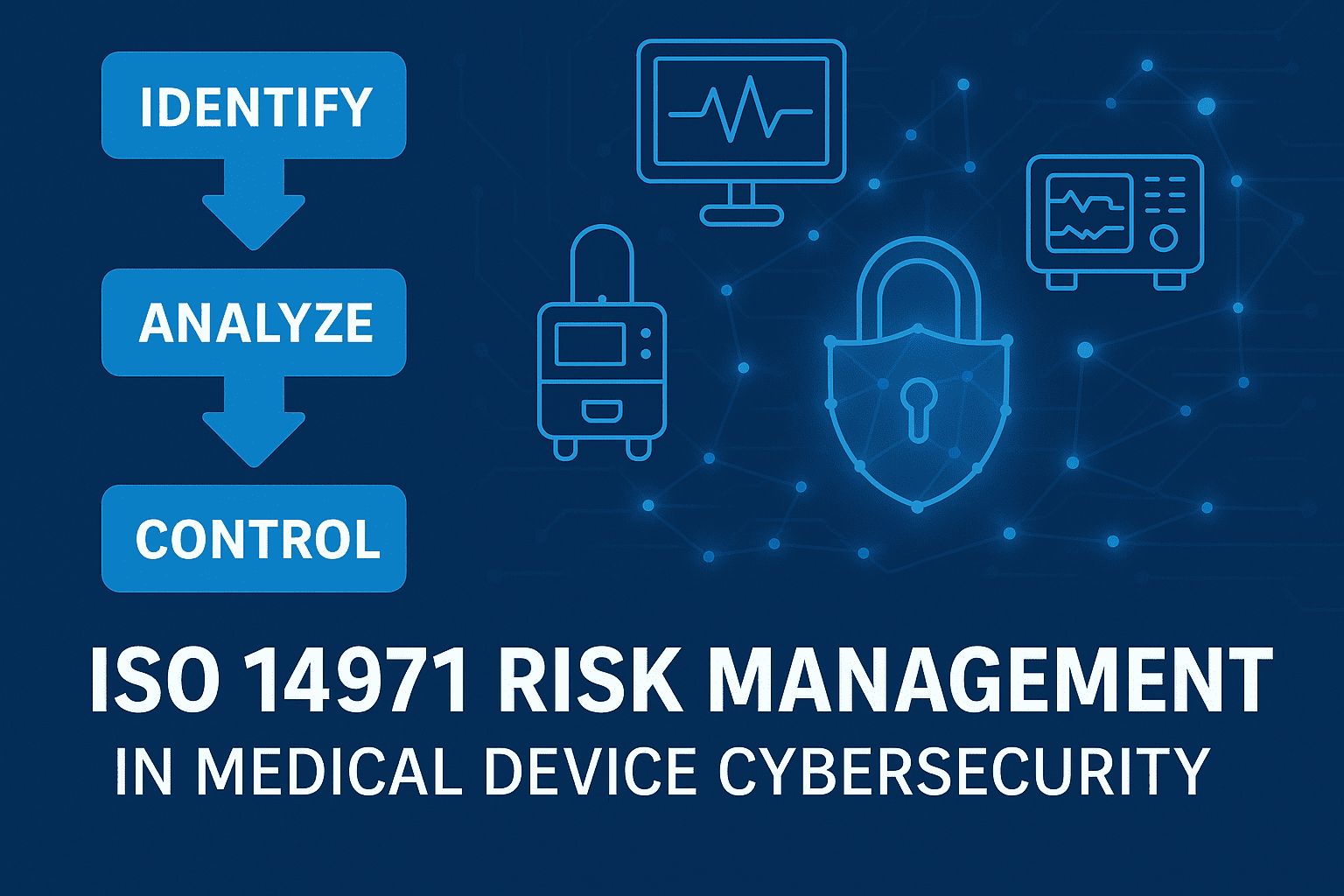
Learn how ISO 14971 risk management applies to medical device cybersecurity - identify cyber hazards, control residual risk, and align with FDA expectations.
Read article
This blog lists the 50 cybersecurity issues in medical devices and explains how penetration testing could have prevented them.
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.