
Salami Attacks in Medical Device Cybersecurity: Tiny Changes
Salami attacks 'slice' tiny changes into transactions or data. Learn how they map to medical device cybersecurity, FDA expectations, and practical controls.
Read articleEvery article in our archive in Primer.
Showing 12 of 127 articles in Primer · Page 4 of 11

Salami attacks 'slice' tiny changes into transactions or data. Learn how they map to medical device cybersecurity, FDA expectations, and practical controls.
Read article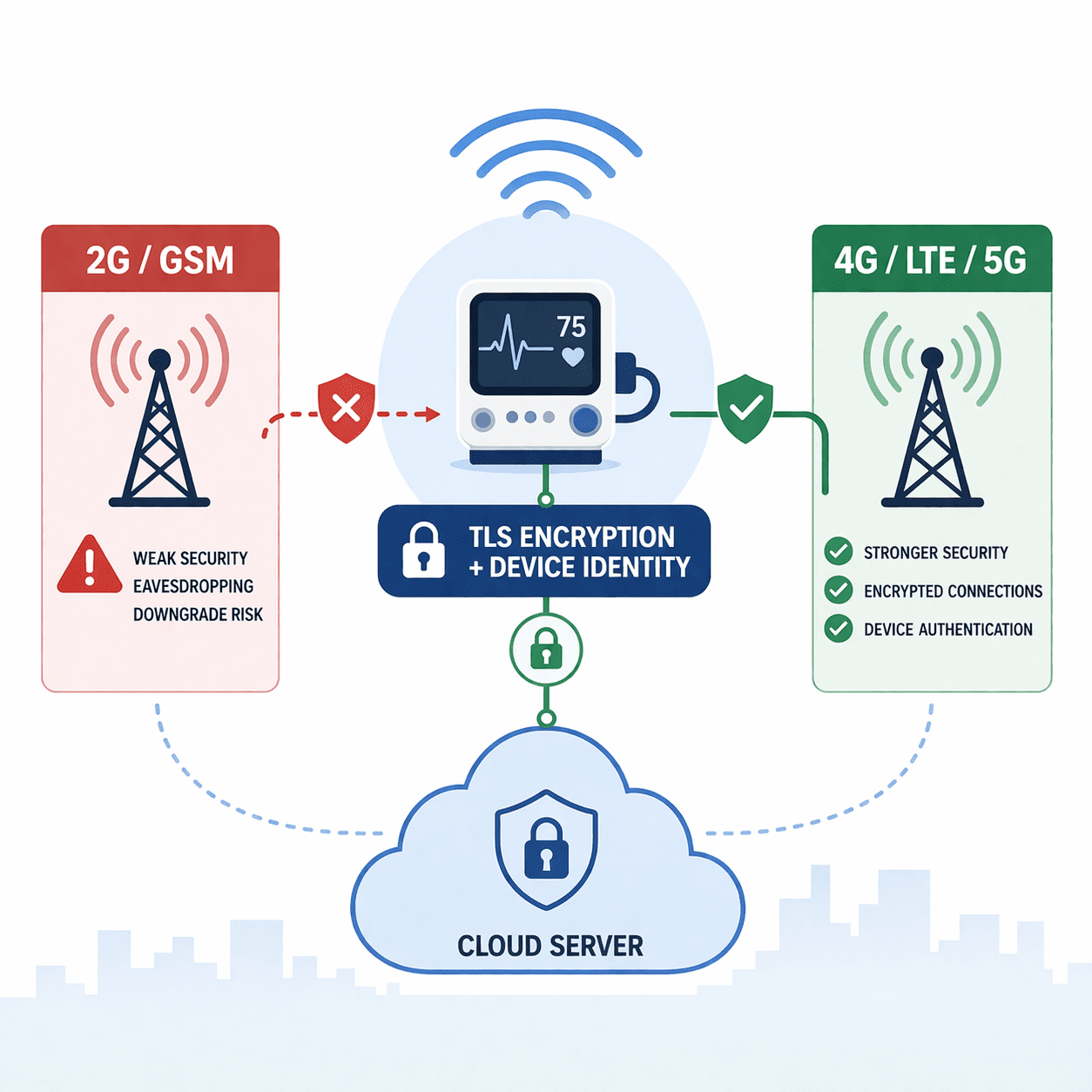
Medical devices using GSM face downgrade and interception risks. Learn practical mitigations: disable 2G, use TLS/mTLS, secure APNs, and FDA-ready evidence.
Read article
Discover the critical role of Near Field Communication (NFC) in safeguarding medical devices from cyber threats.
Read article
Discover the inner workings of interpreted programming languages and how they differ from compiled languages.
Read article
Discover the potential risks and vulnerabilities associated with M2M communication in medical devices, and the critical importance of cybersecurity in safeguarding patient safety and data privacy.
Read article
Discover the ins and outs of the IVD Regulation in medical device cybersecurity in this insightful article.
Read article
JavaScript RCE can compromise device backends, portals, and update services. Learn common causes and FDA-aligned controls to prevent it.
Read article
Updated November 10, 2024 In the medical device industry, Good Manufacturing Practices (GMP) form the foundation for ensuring the safety, effectiveness, and quality of devices that enter the market. These practices are crucial for maintaining regulatory compliance and meeting the high standards expe
Read article
Updated November 16, 2024 The latest FDA medical device cybersecurity update from the Food and Drug Administration (FDA) covers many security controls. Along with specific guidelines, the agency has also provided practical recommendations. This article will review the code, data, and execution integ
Read article
CVD is mandated by Section 524B(b)(1) for FDA cyber device submissions. A practical guide to building a compliant CVD process for MedTech.
Read article
Updated October 26, 2024 Medical devices are often designed to connect to other devices and systems. This opens up extended functionality and the ability to rapidly move information and help patients in new ways. Unfortunately, this also expands a system's attack surface and often gives attackers th
Read article
Learn how UEFI Secure Boot protects medical device systems from bootkits and tampering, plus key management, updates, pitfalls, and testing tips.
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.