MedTech Augmented Reality Cybersecurity
Explore the critical cybersecurity risks associated with augmented reality (AR) medical devices.
Read articleDeep dives on FDA expectations, threat modeling, penetration testing, SDLC, and the standards your team is being asked to meet.
Showing 12 of 360 articles · Page 13 of 30
Explore the critical cybersecurity risks associated with augmented reality (AR) medical devices.
Read article
QNX runs in infusion pumps, imaging consoles, and surgical robots. A MedTech-focused look at QNX vulnerabilities and FDA-aligned mitigation strategies.
Read article
Explore the gripping Homeland episode featuring a pacemaker attack and delve into the realism behind this dramatic plot twist.
Read article
Explore the harrowing tale of the Therac-25 incident, a pivotal case study in medical device failures.
Read article
Discover how robustness and fuzz testing are revolutionizing medical device safety.
Read article
Explore the critical importance of testing medical devices against malformed and unexpected inputs to prevent abuse or misuse.
Read article
Explore the implications of MDCG 2019-16 on medical device cybersecurity, highlighting key guidelines, industry challenges, and strategies for ensuring robust protection in the evolving digital healthcare landscape..
Read article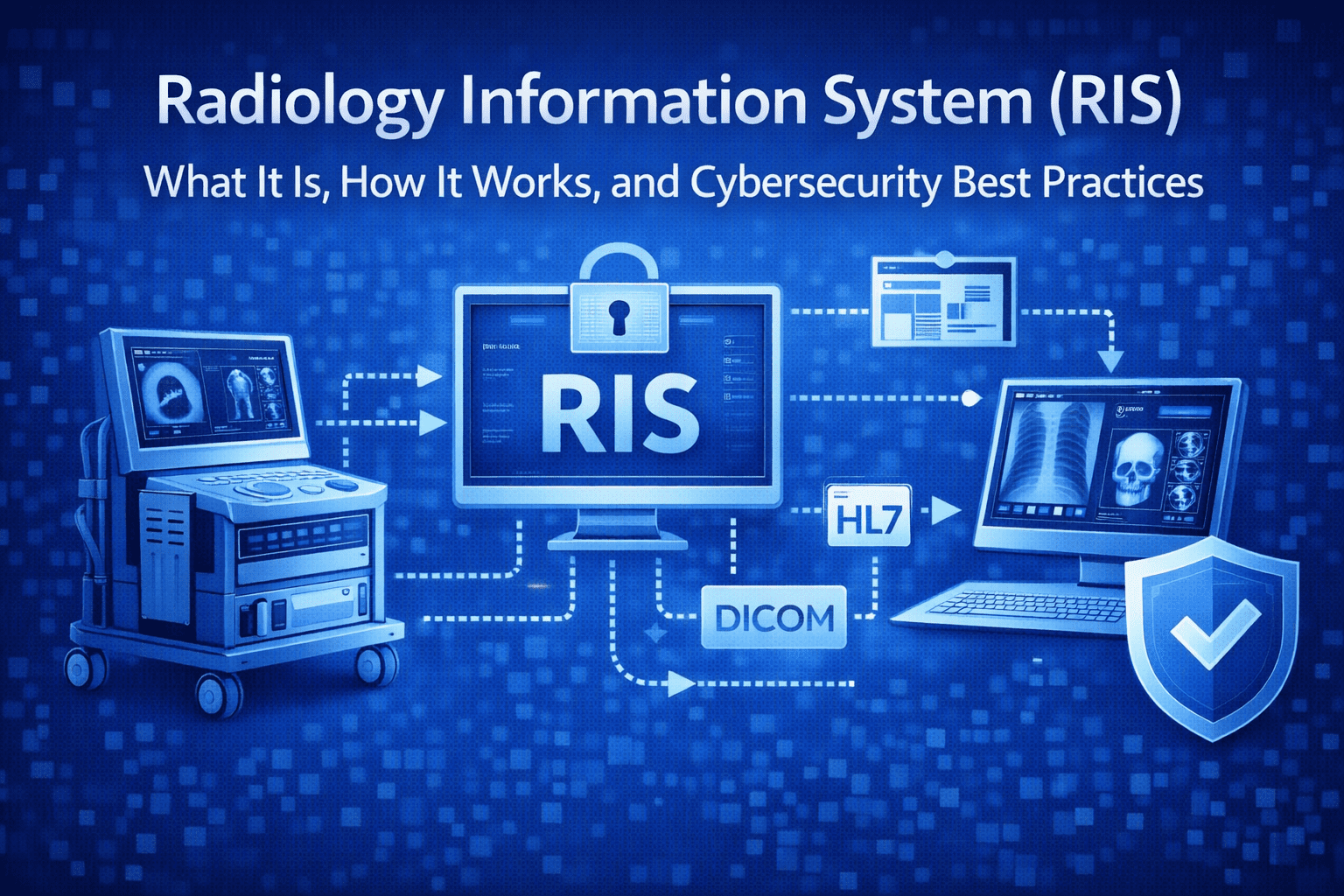
RIS meaning explained: what RIS software does, how RIS integrates with PACS/EHR using HL7 and DICOM, and key cybersecurity controls to reduce risk.
Read article
Explore the intersection of IATF 16949 standards and medical device cybersecurity, uncovering how automotive quality management principles can enhance the safety and security of medical technologies in an increasingly connected world..
Read article
LIS platforms exchange PHI with diagnostic devices. What MedTech manufacturers need to know about LIS security and FDA interoperability expectations.
Read article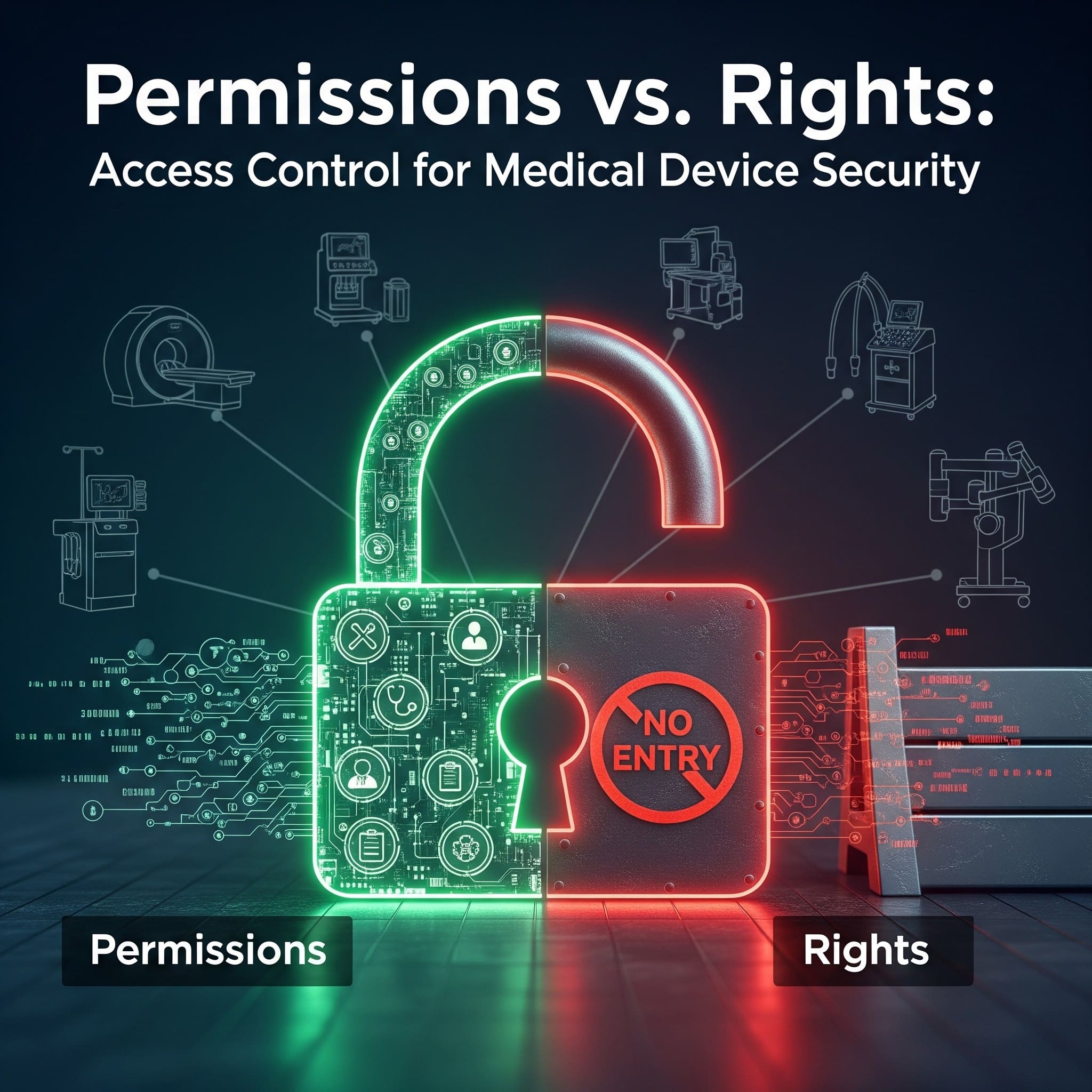
Permissions vs rights explained for medical device cybersecurity: how to model access, enforce least privilege, and align with FDA expectations using RBAC.
Read article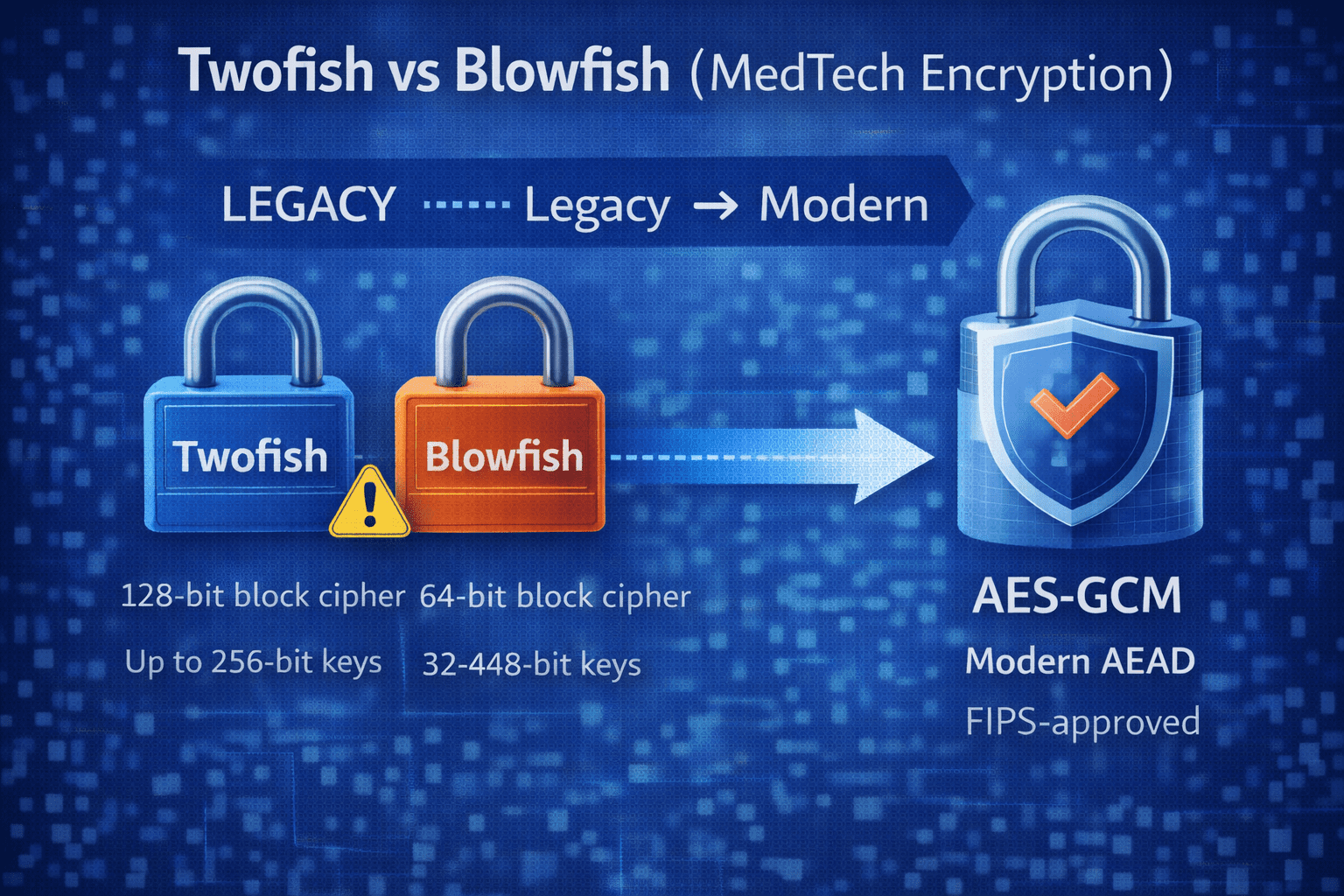
Twofish vs Blowfish in medical devices: what’s viable for legacy, why 64-bit block ciphers are risky at scale, and when to move to AES-GCM.
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.