
25 Use Cases for White-Box Penetration Testing
This article explores white box penetration testing use cases and their importance in ensuring robust cybersecurity.
Read articleDeep dives on FDA expectations, threat modeling, penetration testing, SDLC, and the standards your team is being asked to meet.
Showing 12 of 360 articles · Page 30 of 30

This article explores white box penetration testing use cases and their importance in ensuring robust cybersecurity.
Read article
Learn how different hacker types - white, gray, black hats - impact medical device security. Understand threat modeling and FDA-compliant pen testing strategies.
Read article
SBOM + SAST explained: learn how component transparency and static code scanning strengthen medical device cybersecurity, align with FDA guidance, and cut risk.
Read article
This blog lists the 50 cybersecurity issues in medical devices and explains how penetration testing could have prevented them.
Read article
In this post, we explore the differences and similarities between threat trees and attack trees, specifically in the context of medical device FDA clearance and cybersecurity.
Read article
Updated April 13, 2025 In the rapidly evolving landscape of medical technology, integrating advanced debugging tools like JTAG (Joint Test Action Group) and UART (Universal Asynchronous Receiver-Transmitter) has become a pivotal aspect of medical device design and maintenance. These tools are not ju
Read article
This blog lists the top 10 medical devices that have been hacked, emphasizing the need for robust cybersecurity in healthcare technology.
Read article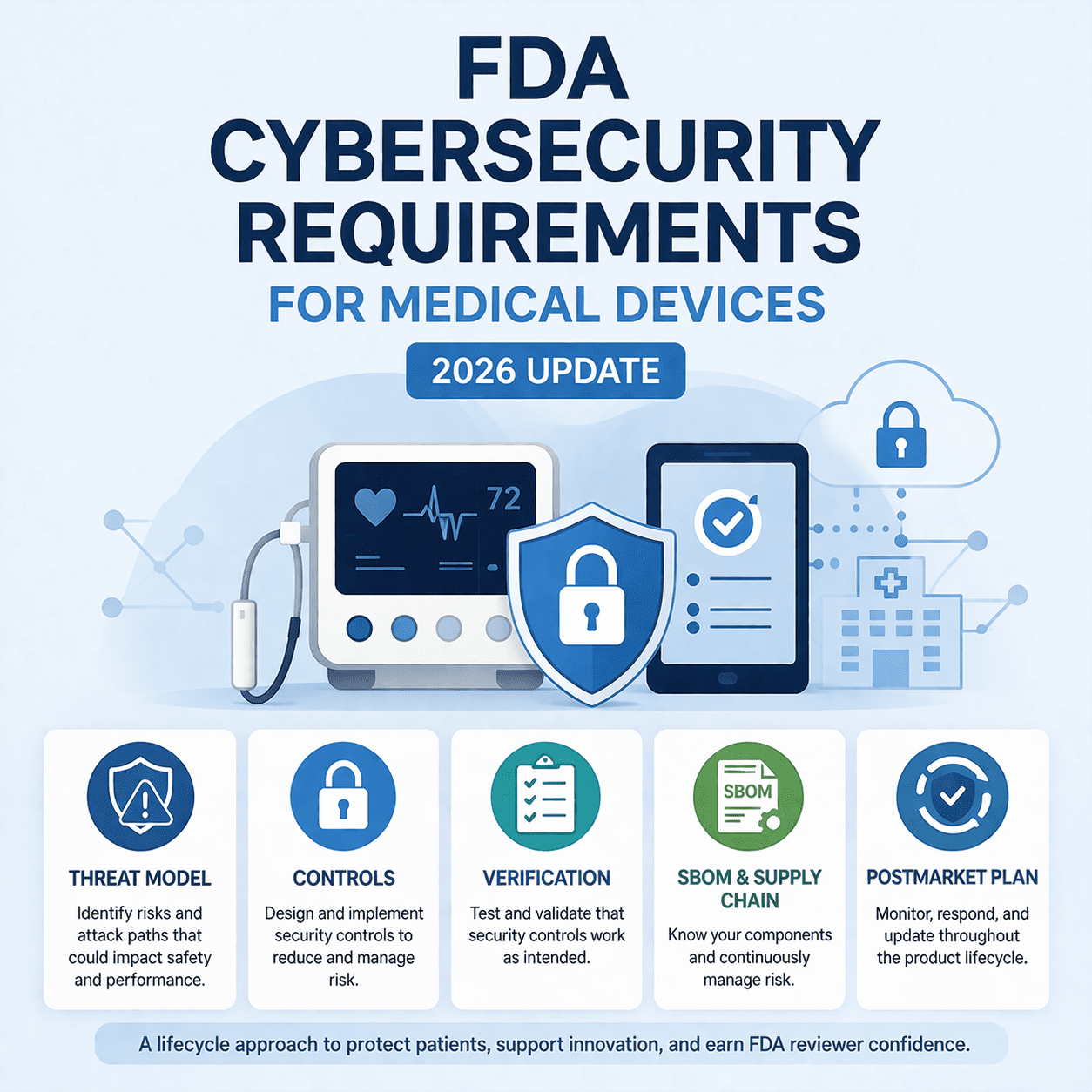
This post explores the FDA's cybersecurity requirements for medical devices, their importance, and the challenges manufacturers face in complying with them.
Read article
Discover how weak cybersecurity left medical devices exposed to hackers - and how FDA guidance and secure design can prevent future breaches.
Read article
There are two main types of software testing with medical devices: static and dynamic. Static testing combs over the code base to look for vulnerable code snippets and provide alternative, secure code. Dynamic testing looks for vulnerabilities in the running application through various types of test
Read article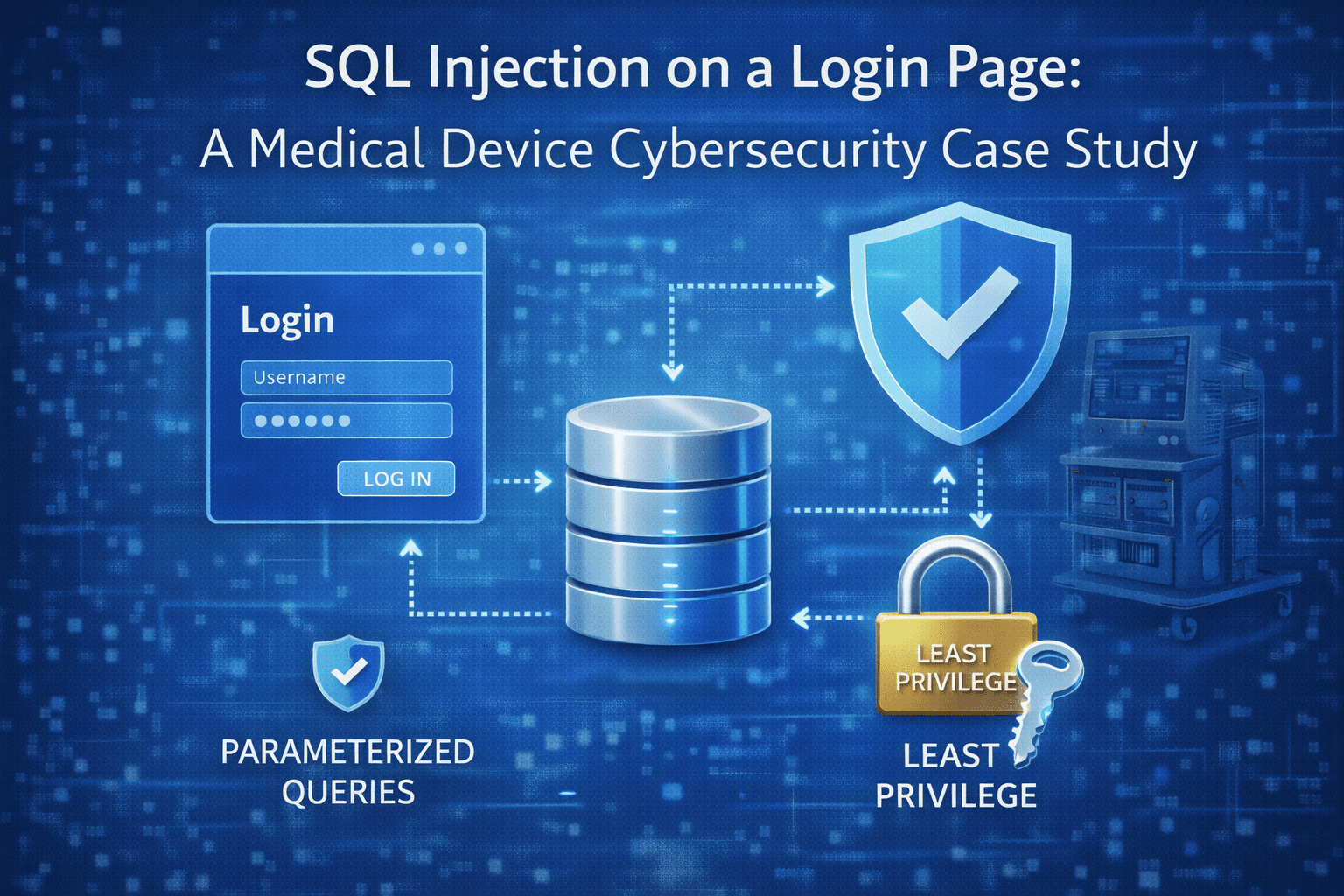
A real-world SQL injection case study showing how login flaws can escalate to system compromise - plus prevention and verification steps for medical device teams.
Read article
The Blue Goat Cyber blog offers detailed insights into cybersecurity, focusing on areas like healthcare cybersecurity trends, hacker profiles and motivations, medical device cybersecurity, and methods of initial access by attackers.
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.