
AJAX Vulnerabilities in Medical Device Web Applications
AJAX vulnerabilities in medical device web apps can expose APIs, authentication, & patient data. Learn to align controls with FDA cybersecurity expectations.
Read articleDeep dives on FDA expectations, threat modeling, penetration testing, SDLC, and the standards your team is being asked to meet.
Showing 12 of 360 articles · Page 14 of 30

AJAX vulnerabilities in medical device web apps can expose APIs, authentication, & patient data. Learn to align controls with FDA cybersecurity expectations.
Read article
Learn about the potential cybersecurity risks associated with medical devices in this comprehensive article.
Read article
Learn what an XXE attack is, how it impacts MedTech software, and the practical parser, testing, and lifecycle controls that prevent it.
Read article
Salami attacks 'slice' tiny changes into transactions or data. Learn how they map to medical device cybersecurity, FDA expectations, and practical controls.
Read article
Updated October 26, 2024 As the medical device industry continues to innovate, cybersecurity has become critical to ensuring new products' safety, effectiveness, and market success. With the FDA's evolving requirements, manufacturers must adopt a proactive approach to cybersecurity throughout the pr
Read article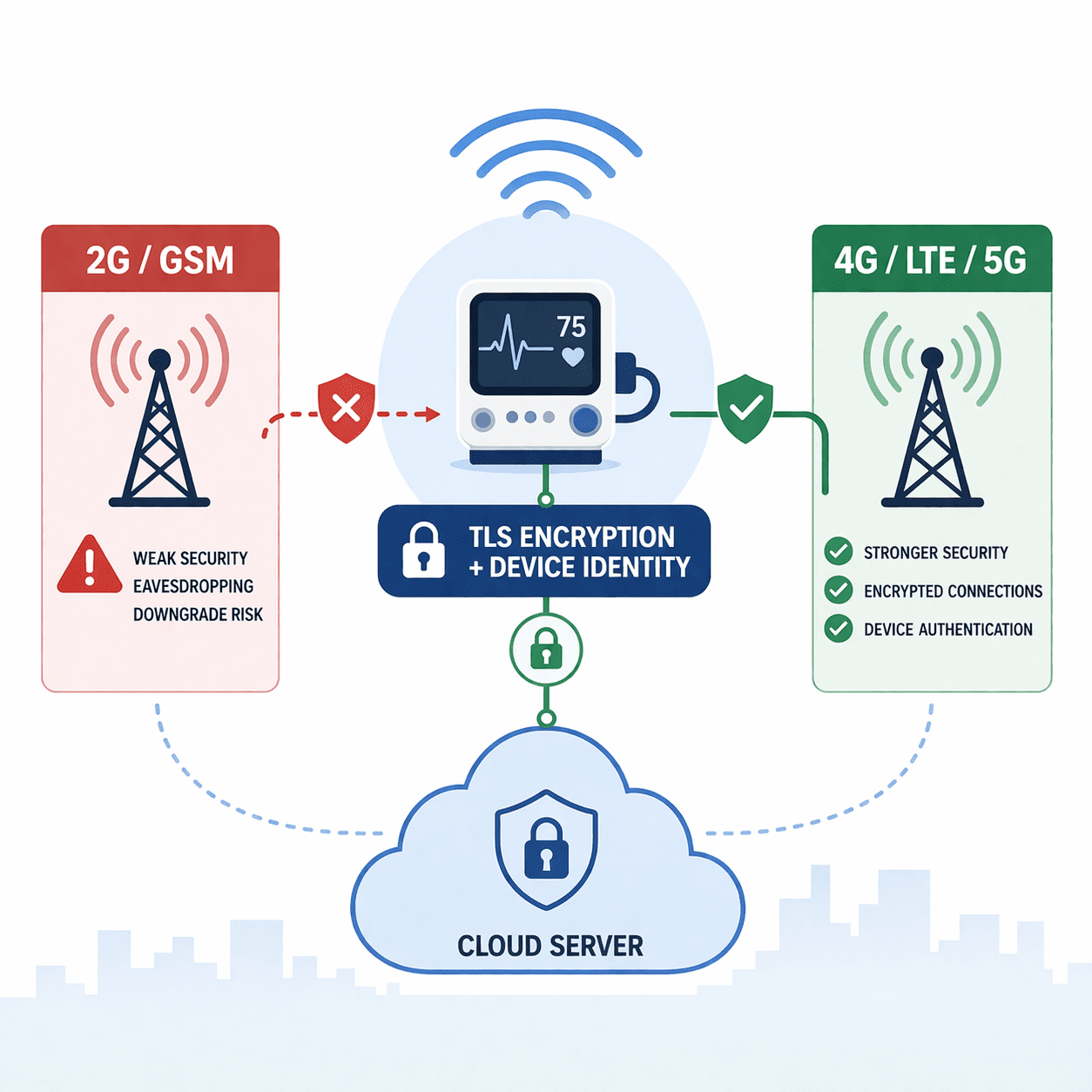
Medical devices using GSM face downgrade and interception risks. Learn practical mitigations: disable 2G, use TLS/mTLS, secure APNs, and FDA-ready evidence.
Read article
The complete guide to NFC and RFID cybersecurity for FDA-regulated medical devices - vulnerabilities, threat modeling, test evidence, and §524B / SPDF documentation.
Read article
Learn how to protect medical devices using the CoAP protocol with our comprehensive guide on ensuring cybersecurity.
Read article
Discover the critical role of Near Field Communication (NFC) in safeguarding medical devices from cyber threats.
Read article
Discover how the Narrowband IoT protocol is revolutionizing cybersecurity for medical devices.
Read article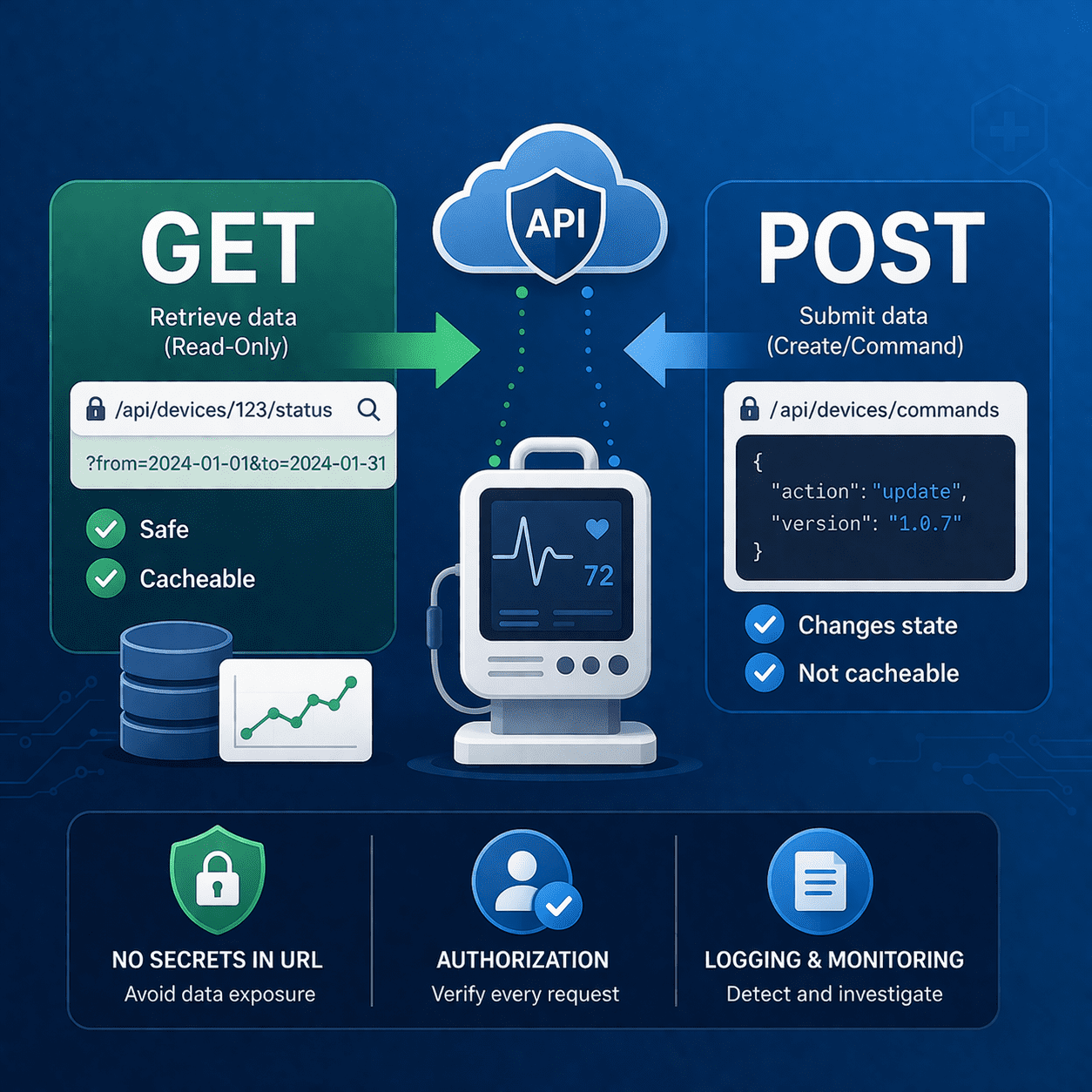
Choose GET vs POST correctly for medical device APIs to prevent data leaks, unsafe replays, and auth gaps - plus an FDA-friendly evidence checklist.
Read article
Discover the inner workings of interpreted programming languages and how they differ from compiled languages.
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.