Linux vs Windows: A Security Comparison
Linux vs Windows security for medical devices: isolation, hardening, secure updates, and long-term patching - so teams can choose and defend an OS decision.
Read articleDeep dives on FDA expectations, threat modeling, penetration testing, SDLC, and the standards your team is being asked to meet.
Showing 12 of 360 articles · Page 26 of 30
Linux vs Windows security for medical devices: isolation, hardening, secure updates, and long-term patching - so teams can choose and defend an OS decision.
Read article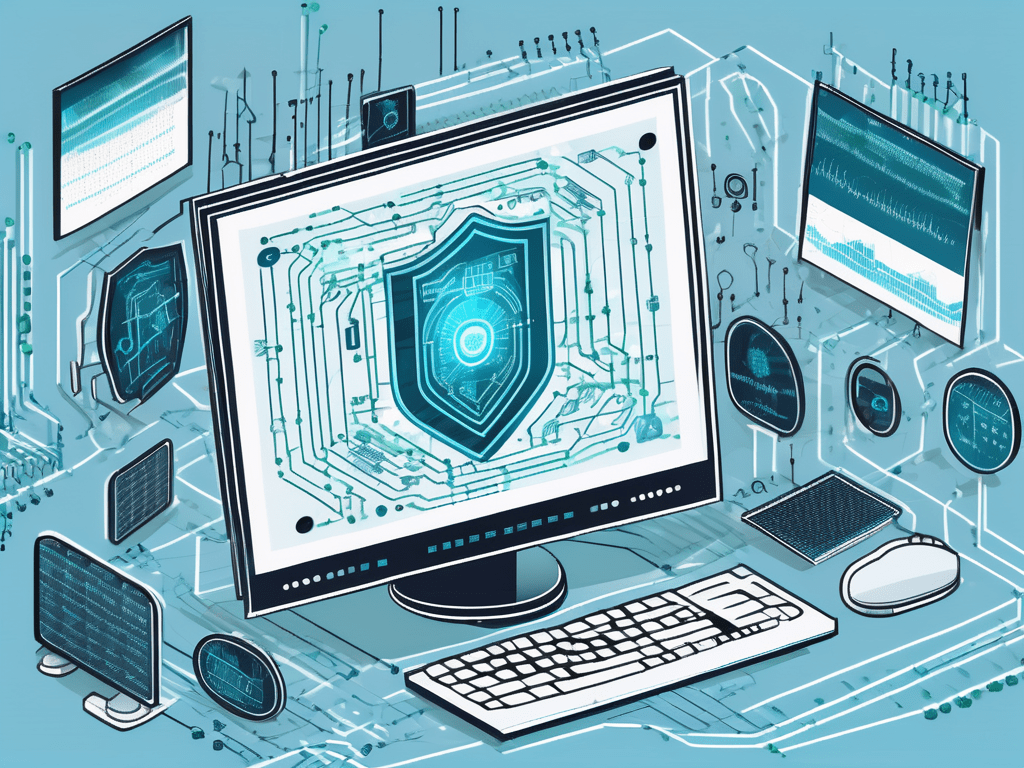
Learn how Shodan exposes connected medical devices - and how manufacturers and hospitals can use it to identify risks, improve security, and meet FDA expectations.
Read article
Protect medical devices with WAFs and reverse proxies. Learn the differences, use cases, and FDA-ready best practices for cybersecurity compliance.
Read article
A 10-point medical device cybersecurity assessment checklist to align with FDA guidance, manage risks, and protect patient safety.
Read article
FDA cybersecurity documentation requirements (2025): 524B cyber device rules, SPDF, SBOM, threat modeling, testing, and a premarket submission checklist.
Read article
Discover cybersecurity best practices for medical device design, from threat modeling to FDA-aligned lifecycle management, to protect patients and data.
Read article
ISO 27001 strengthens medical device cybersecurity, but it must be paired with patient safety standards and FDA guidance to protect patients fully.
Read article
Discover how to navigate the complexities of interoperable medical devices and effectively manage associated risks.
Read article
Discover how emerging technologies are shaping the landscape of medical device cybersecurity.
Read article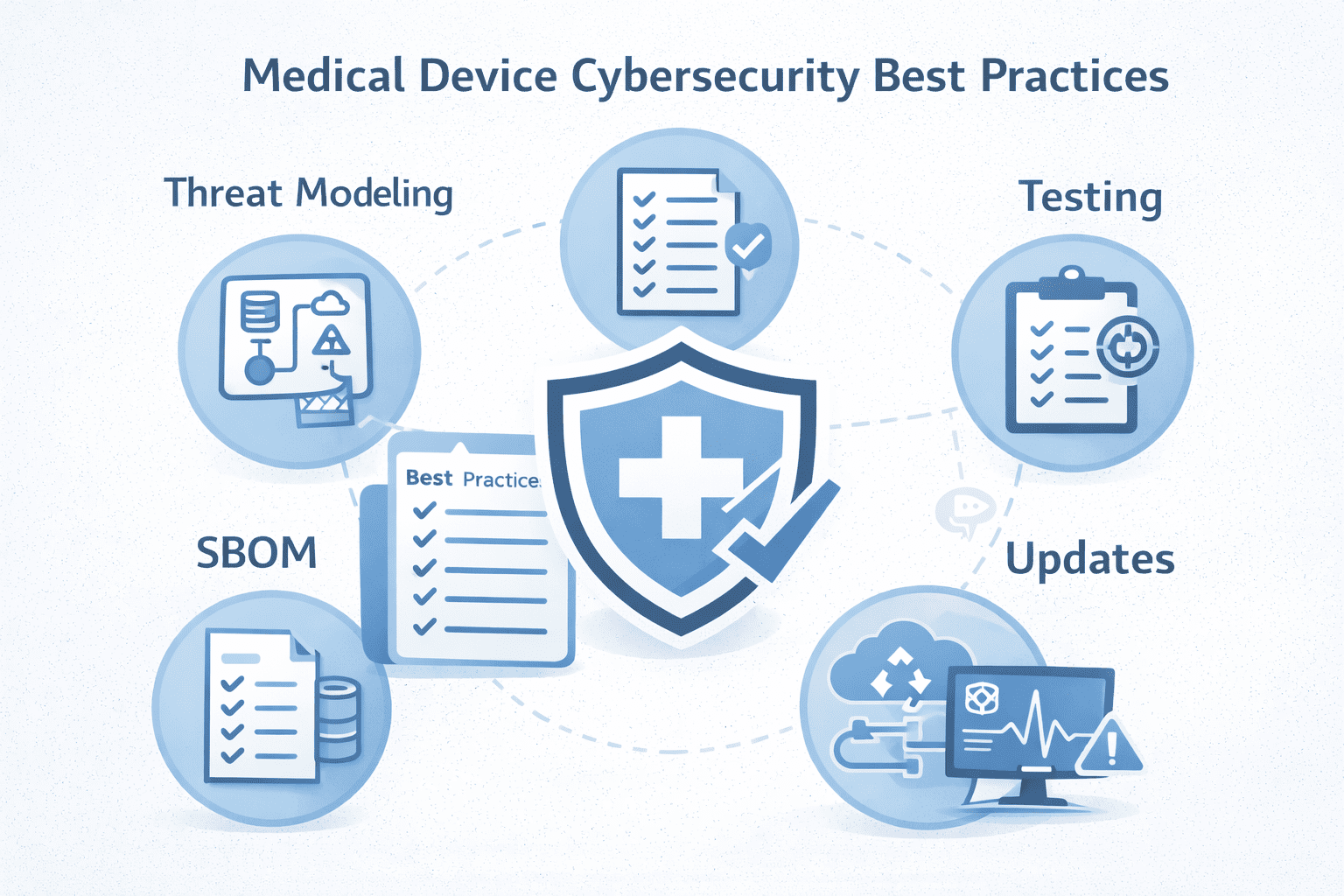
Medical device cybersecurity best practices for 2025: threat modeling, SBOM, penetration testing, secure updates, and FDA 524B/SPDF readiness.
Read article
Discover how medical devices are meticulously designed with patient safety as the top priority.
Read article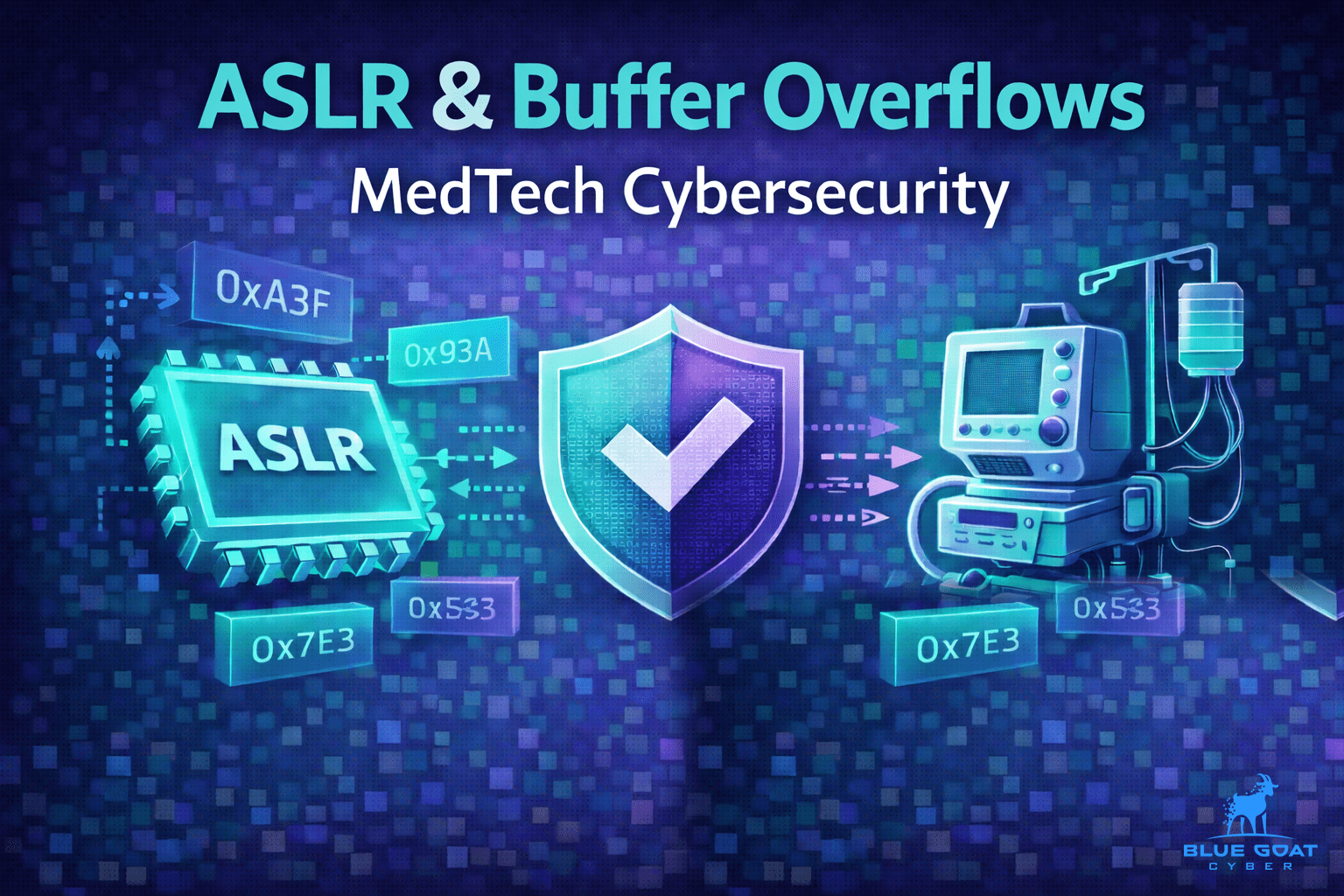
Learn how ASLR reduces buffer overflow impact, where it falls short, and practical controls MedTech teams can use to prevent memory corruption in devices.
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.