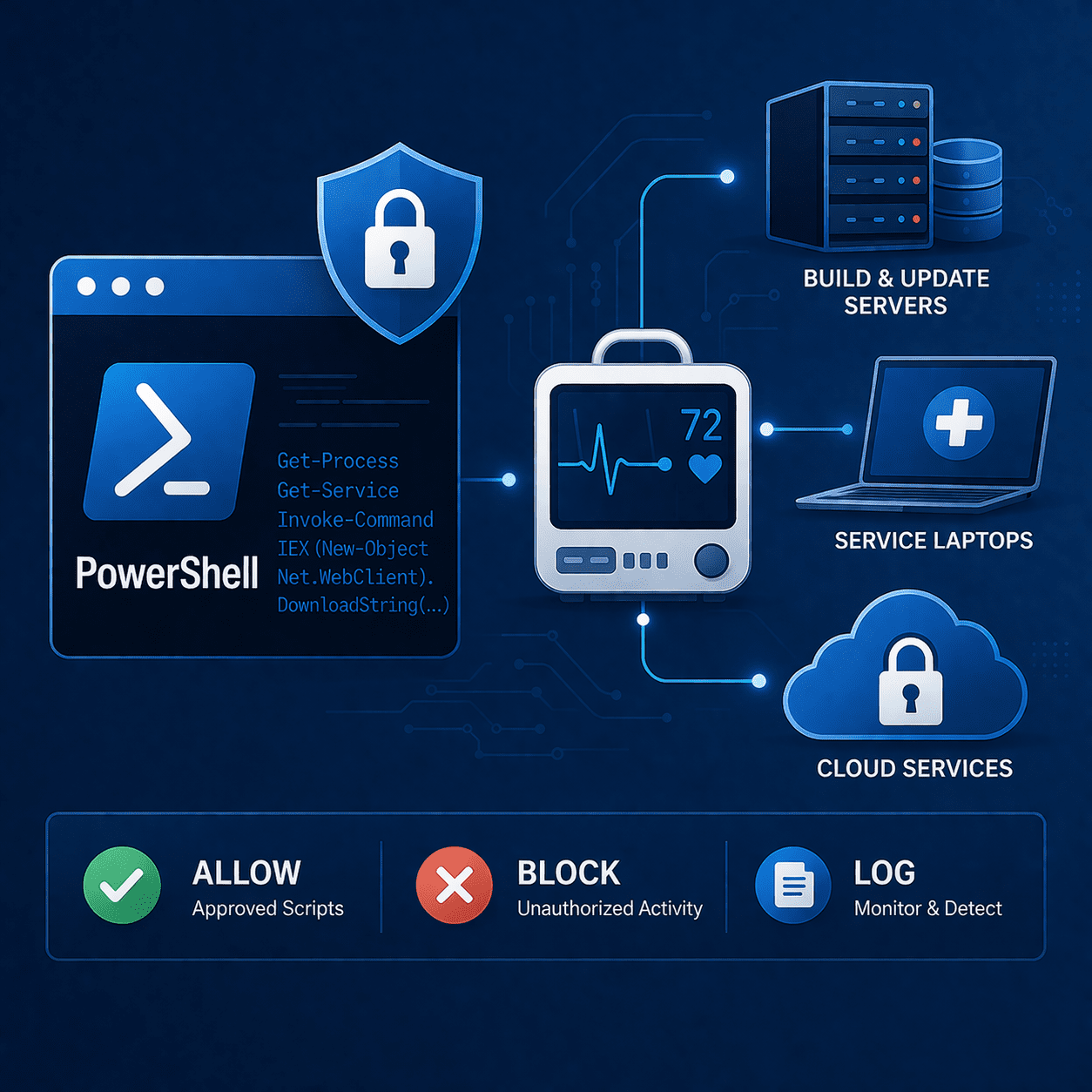
PowerShell in Medical Device Cybersecurity: Abuse & Defenses
Learn how attackers abuse PowerShell in MedTech environments - and how to harden endpoints, logging, and admin access to support FDA-ready cybersecurity evidence.
Read articleDeep dives on FDA expectations, threat modeling, penetration testing, SDLC, and the standards your team is being asked to meet.
Showing 12 of 360 articles · Page 25 of 30
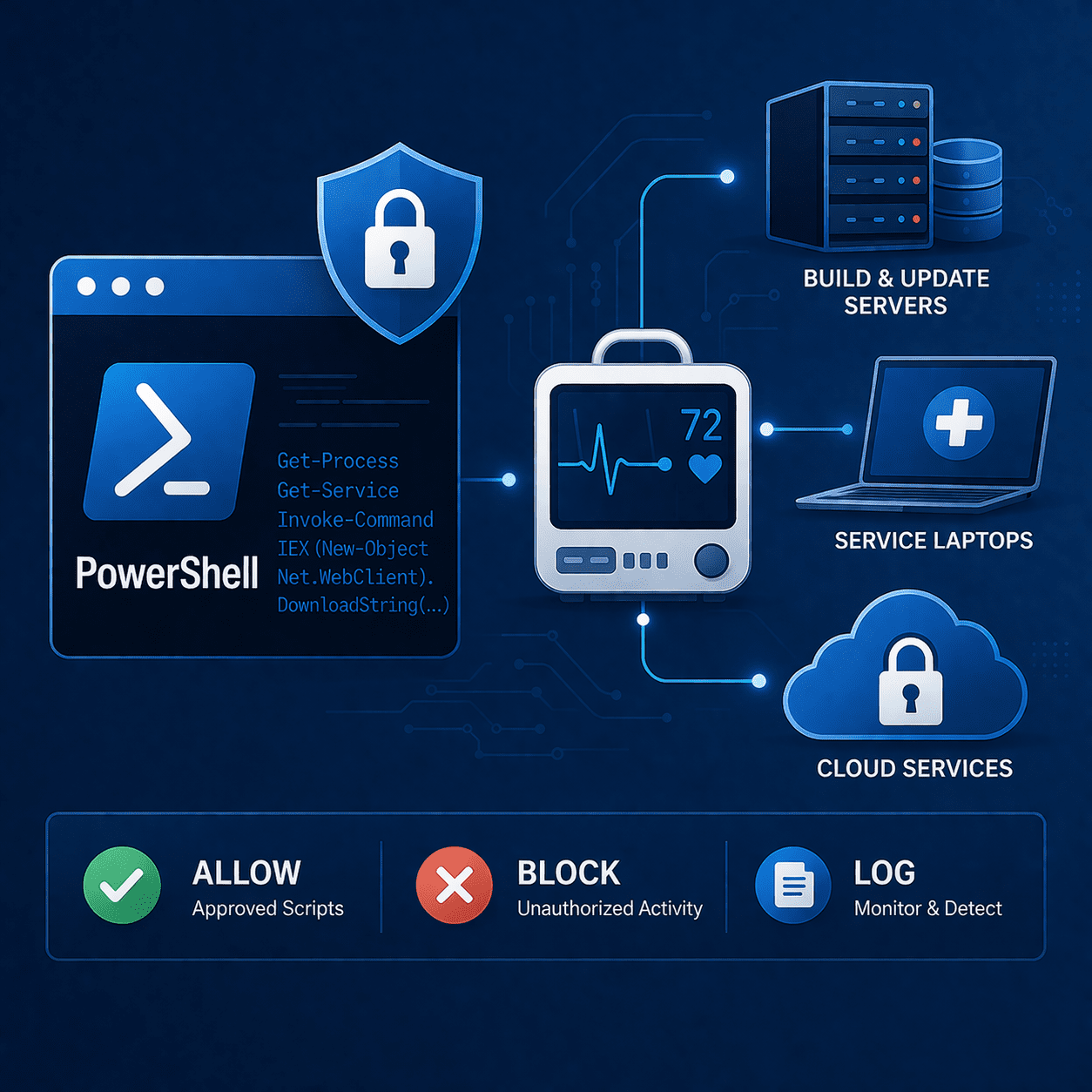
Learn how attackers abuse PowerShell in MedTech environments - and how to harden endpoints, logging, and admin access to support FDA-ready cybersecurity evidence.
Read article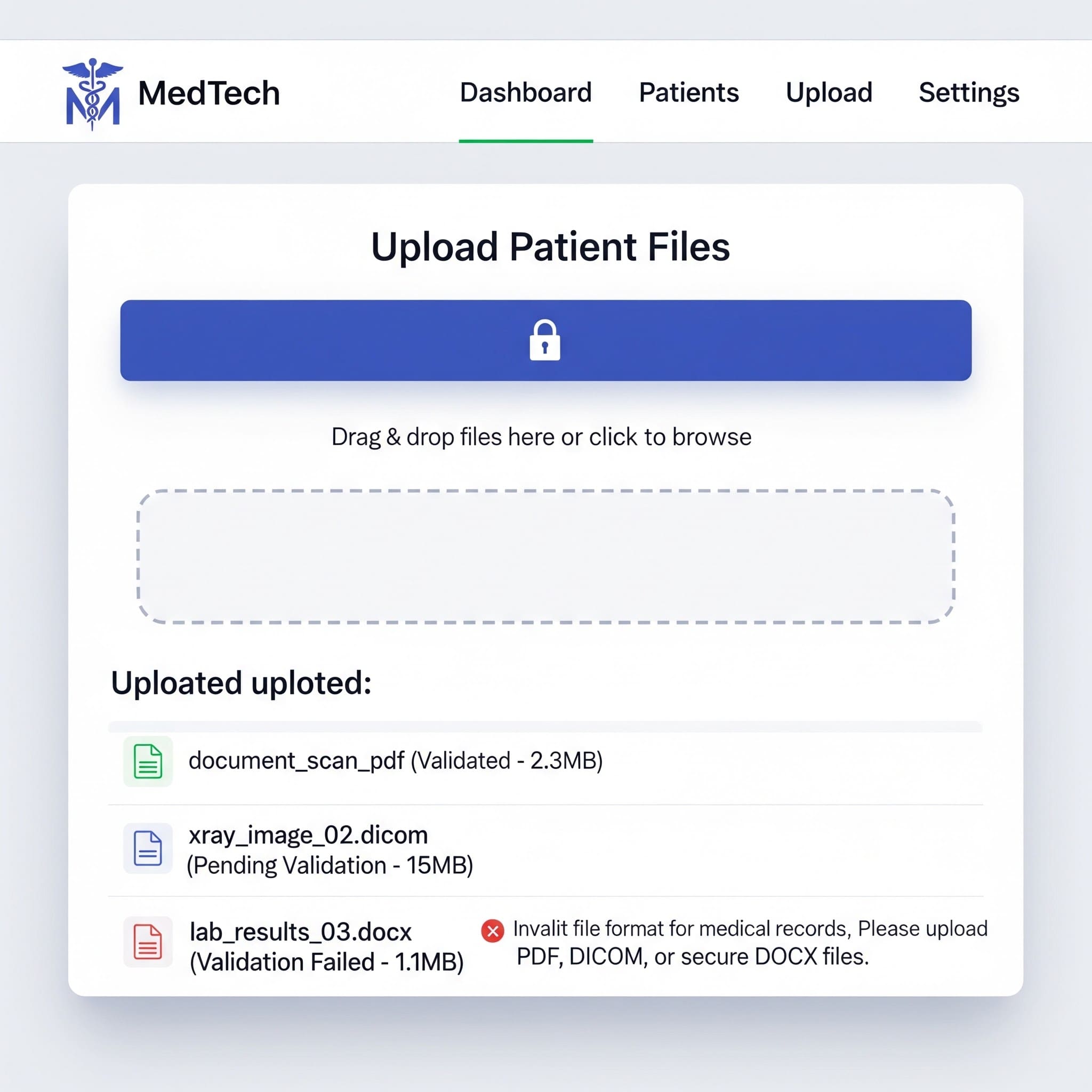
Learn OWASP-aligned file upload validation techniques - type checks, storage isolation, malware scanning, and testing - tailored for regulated environments.
Read article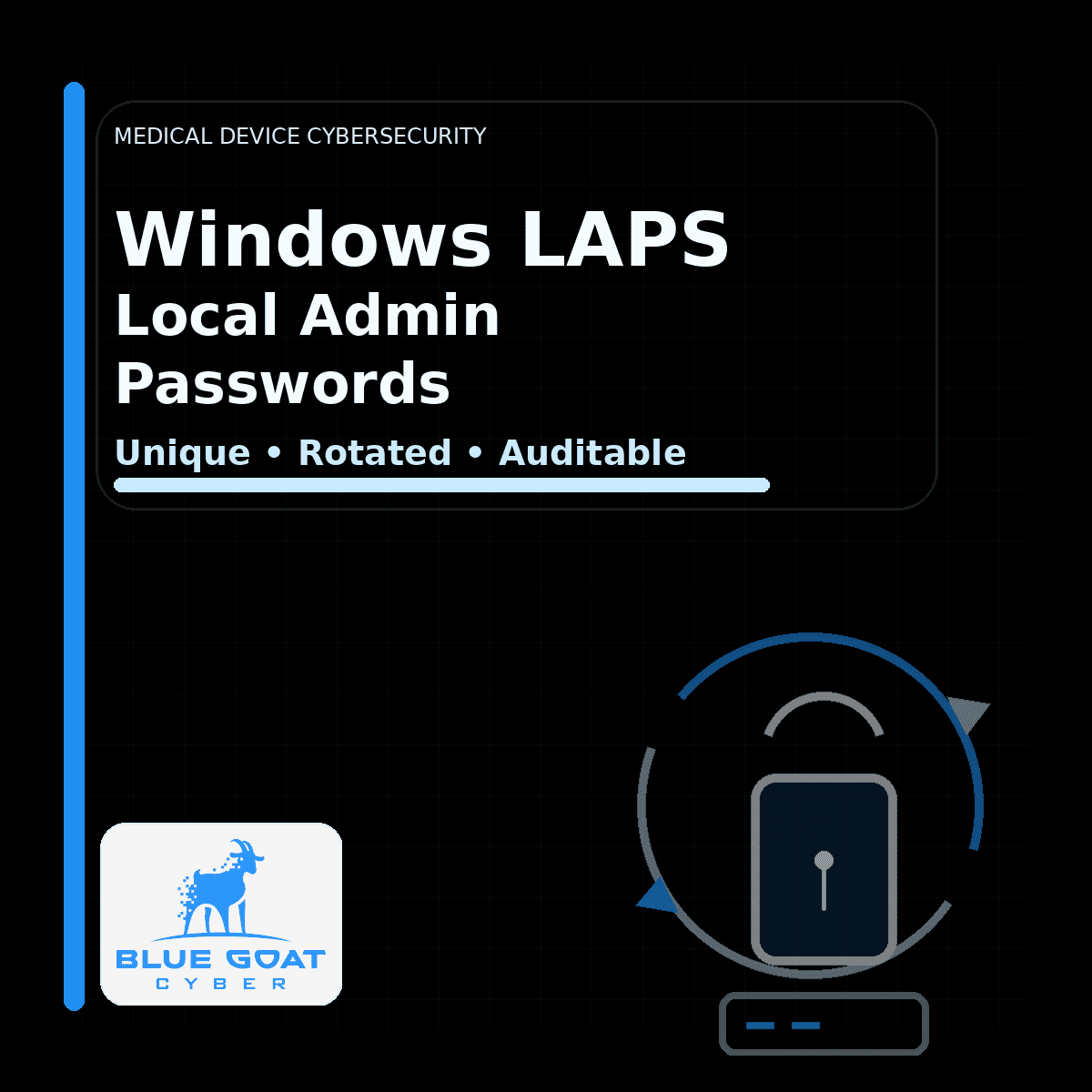
Manage local admin passwords on Windows-based medical devices safely. Why GPP is risky, and how Windows LAPS supports rotation, control, and audits.
Read article
Learn what return-to-libc attacks mean for medical device cybersecurity - and how to reduce risk with memory protections, secure coding, and testing.
Read article
Safer alternatives to Tor for MedTech teams: dark web monitoring, breach intel, and postmarket-ready workflows to reduce risk in IoMT ecosystems.
Read article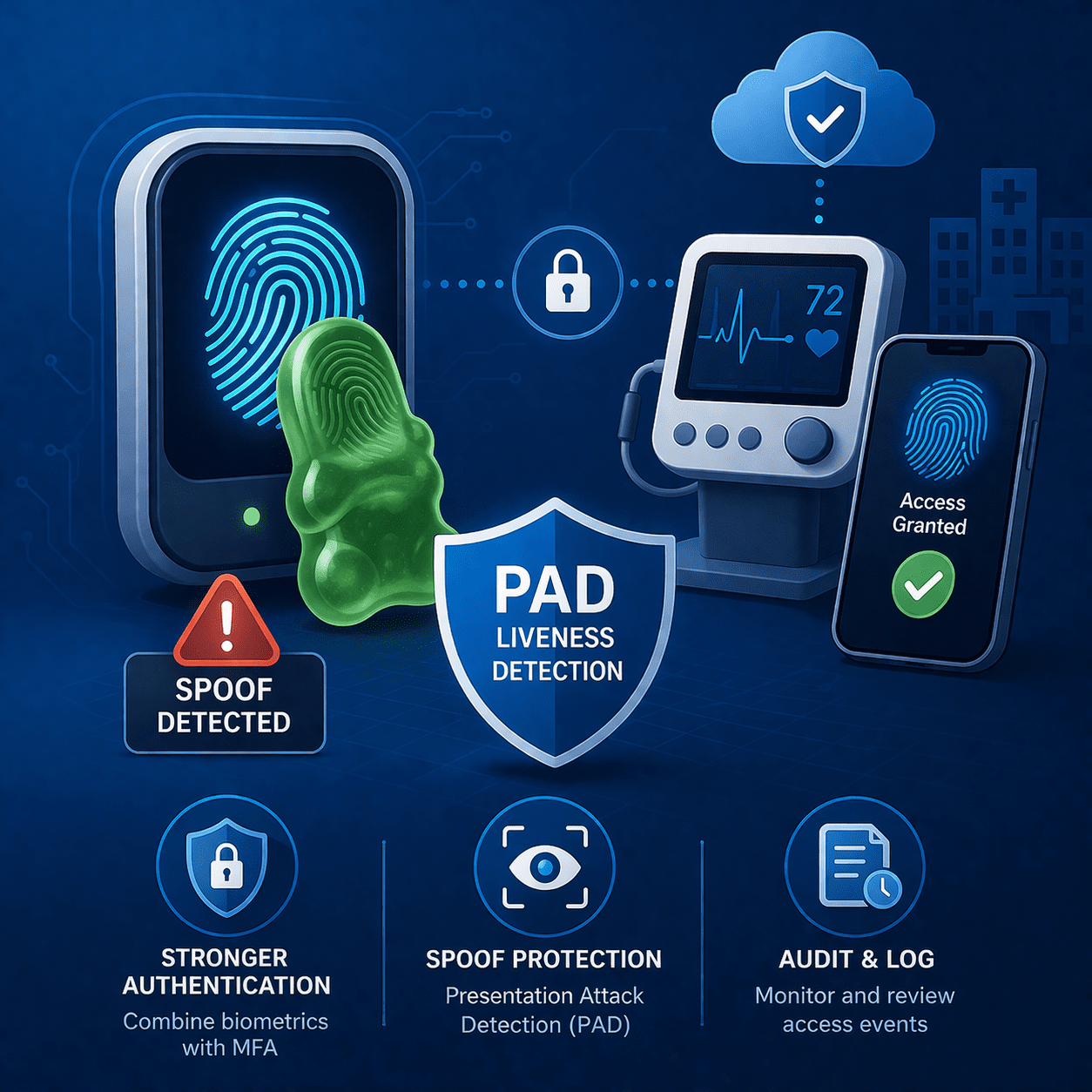
Biometrics improve usability - but can be spoofed. Learn “gummy finger” risks, liveness/PAD, and FDA-ready controls for medical device ecosystems.
Read article
Discover how cybersecurity failures in medical devices have led to recalls and potential risks for patients.
Read article
Learn how device cloning threatens medical device security and how manufacturers can defend against spoofing risks to meet FDA cybersecurity expectations.
Read article
Bluetooth Low Energy is core to CGMs, pacemakers, and wearables. Common BLE attack vectors and the controls FDA expects in premarket submissions.
Read article
Cyber attribution is uncertain by design. Learn why, what evidence holds up, and how MedTech teams should respond for FDA-aligned risk management.
Read article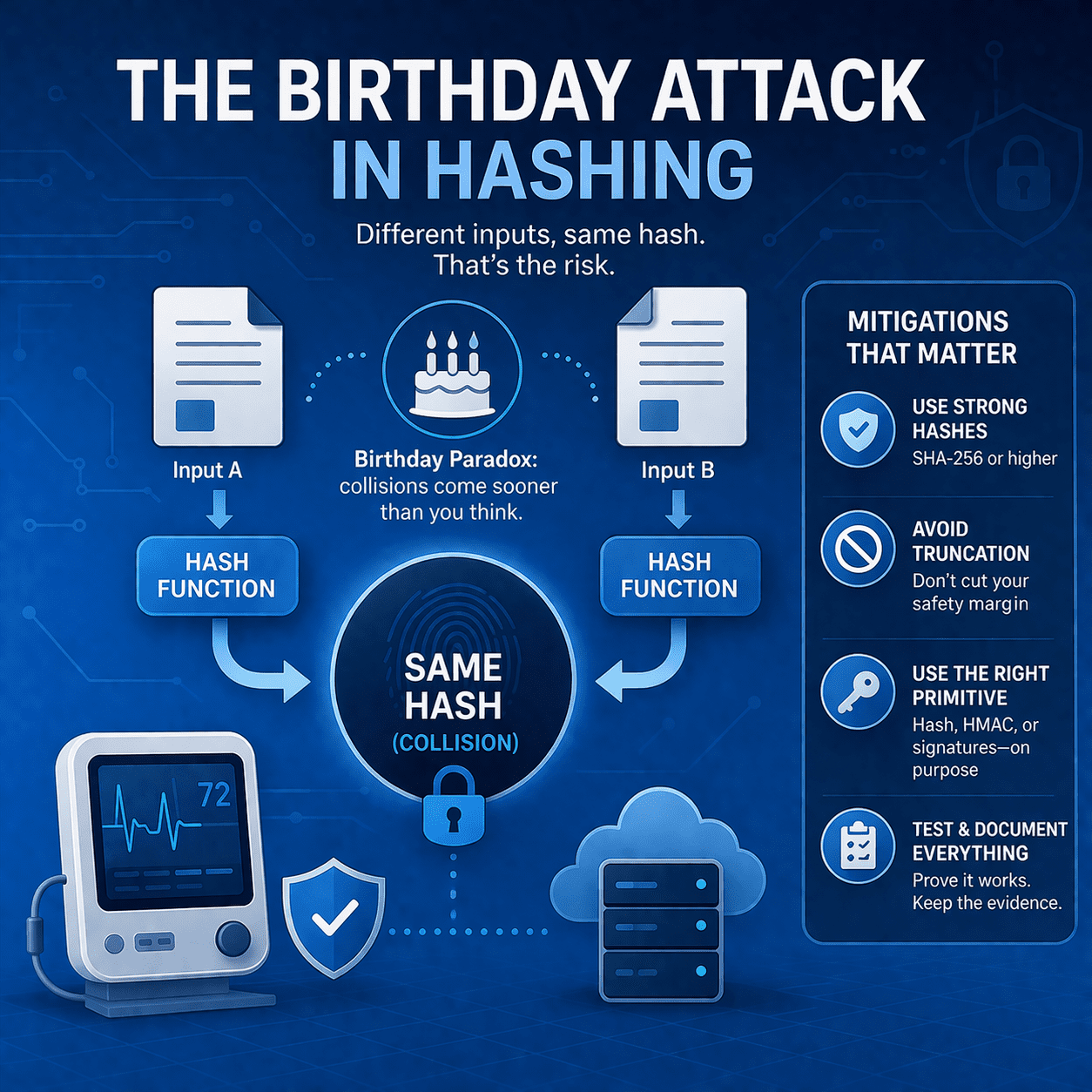
Learn how birthday attacks exploit hash collision probability - and what MedTech teams should do (SHA-256+, signing, truncation rules, testing, evidence).
Read article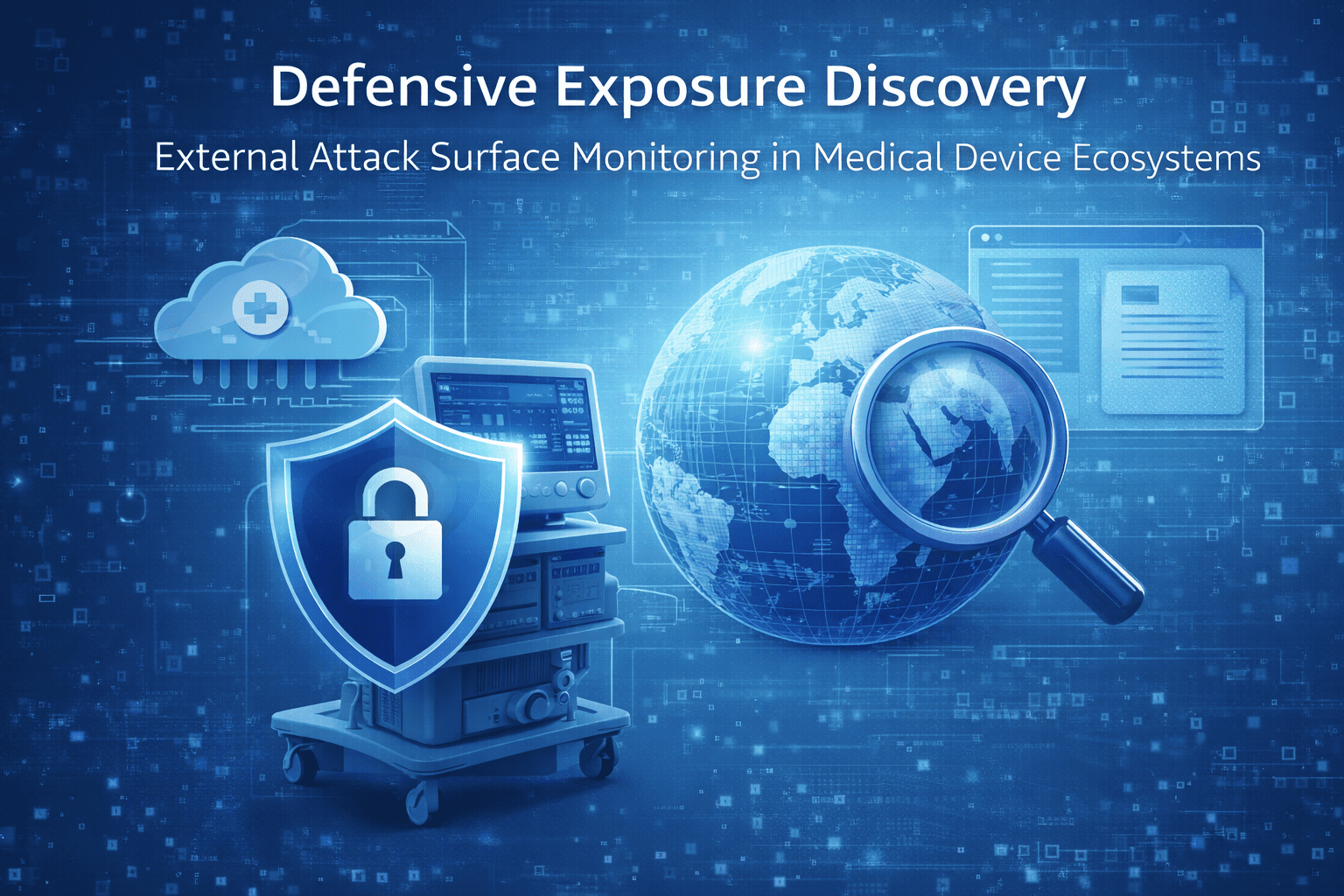
Use GHDB as a defensive OSINT check to find unintended public exposure in medical device ecosystems - cloud portals, docs, and support sites - and fix it fast.
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.