Securing IoT-Enabled Medical Devices: 5 Essential Tips
Discover 5 essential tips for securing IoT-enabled medical devices and safeguarding patient data.
Read articleDeep dives on FDA expectations, threat modeling, penetration testing, SDLC, and the standards your team is being asked to meet.
Showing 12 of 360 articles · Page 28 of 30
Discover 5 essential tips for securing IoT-enabled medical devices and safeguarding patient data.
Read article
Discover the crucial steps to safeguarding network security for connected medical devices in the healthcare industry.
Read article
Why IDS/IPS agents don’t work for medical devices and what FDA-aligned alternatives like segmentation, gateways, and monitoring mean for patient safety.
Read article
Learn how nonrepudiation in medical device cybersecurity protects patient safety, ensures data integrity, and aligns with FDA guidance.
Read article
Discover how TLS 1.3 strengthens medical device cybersecurity, protects patient data, and supports FDA compliance with Blue Goat Cyber.
Read article
Learn how to create powerful and effective password wordlists with our comprehensive guide.
Read article
Learn how to protect medical devices from XSS attacks with expert guidance, FDA cybersecurity compliance, and proactive strategies from Blue Goat Cyber.
Read article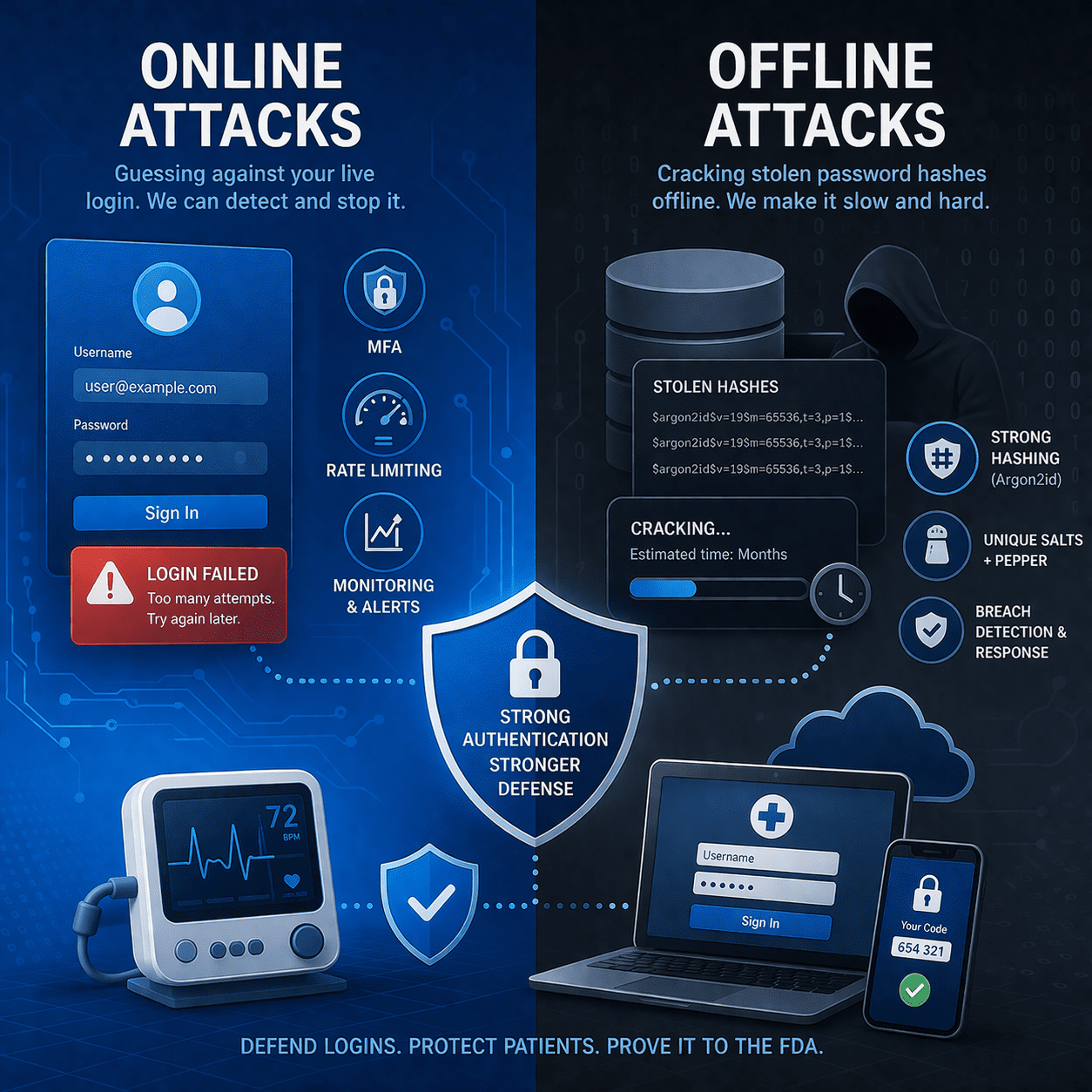
Compare online guessing vs offline hash cracking in MedTech systems. Learn MFA, rate-limits, and secure password storage to reduce risk & support FDA evidence.
Read article
Apply OWASP Top 10:2025 to connected medical devices, APIs, and apps. Practical testing, fixes, and FDA-ready evidence for MedTech teams.
Read article
Healthcare IoT and IoMT devices must be secured to avoid cybersecurity threats that could compromise patient safety and PHI.
Read article
This post delves into the intriguing world of Vulnerability Assessment and Penetration Testing (VAPT) and describes how these two should be used together.
Read article
Why medical device cybersecurity matters: protect patients, prevent disruptions, and meet FDA expectations with lifecycle security from design to postmarket.
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.