
AAMI TIR57 Risk Management for Medical Devices
A practical guide to AAMI TIR57 (R2023) and how it supports FDA’s Feb 2026 cybersecurity guidance - risk analysis, controls, and evidence.
Read articleDeep dives on FDA expectations, threat modeling, penetration testing, SDLC, and the standards your team is being asked to meet.
Showing 12 of 360 articles · Page 29 of 30

A practical guide to AAMI TIR57 (R2023) and how it supports FDA’s Feb 2026 cybersecurity guidance - risk analysis, controls, and evidence.
Read article
This guide emphasizes securing communication protocols in medical devices and provides actionable insights for manufacturers to enhance safety and privacy.
Read article
In this post we're diving into a critical yet often shadowed aspect of healthcare cybersecurity – MedHacking and its various forms, including Medjacking
Read article
This post outlines the key steps to perform a comprehensive cybersecurity risk assessment and testing of medical devices.
Read article
In this post, we unravel this complex issue of cyber threats in medical devices and discuss what manufacturers can do to make their devices more secure.
Read article
The post reviews a vital yet often overlooked topic: securing medical devices from cyber threats and what steps can be taken to ensure medical device security.
Read article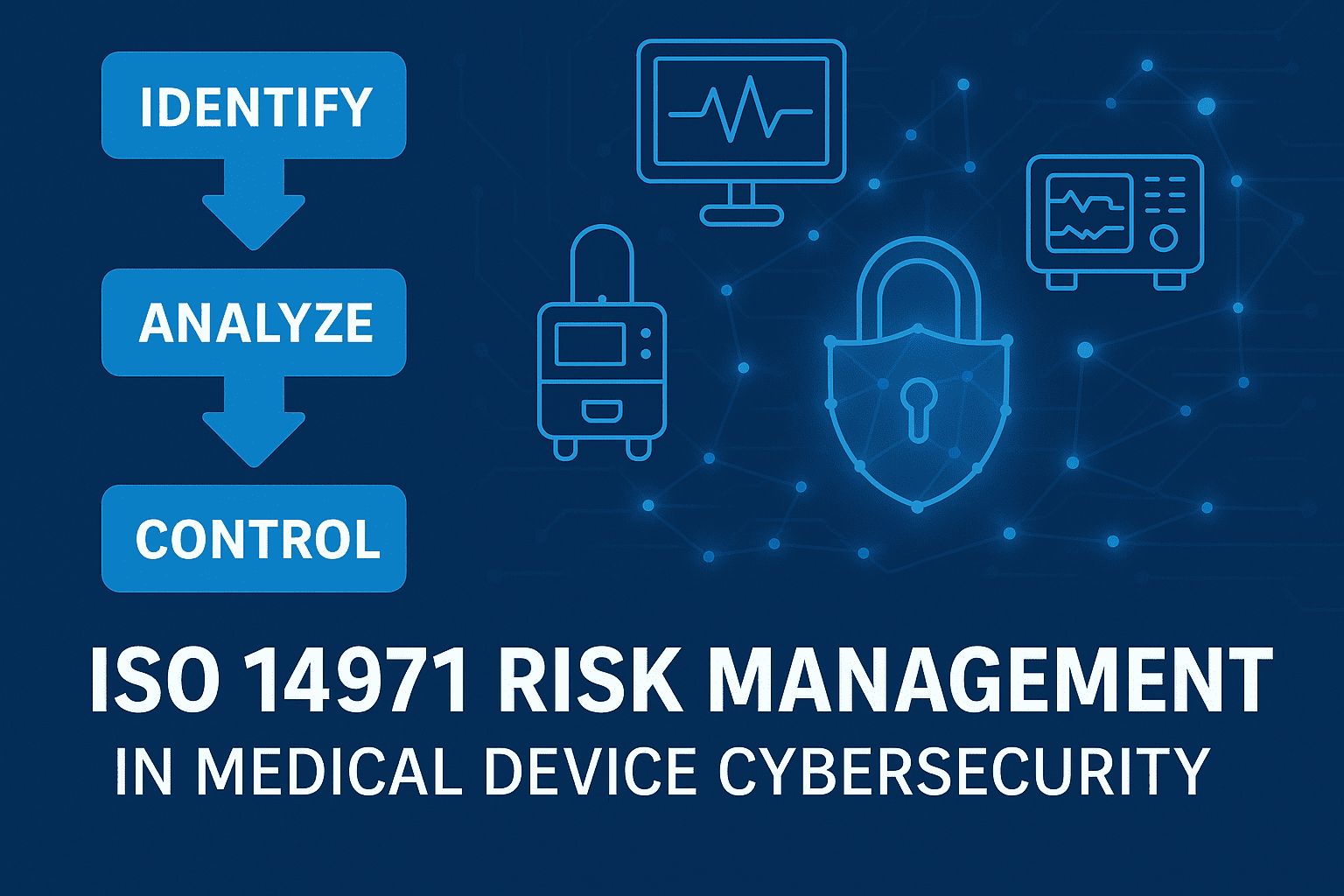
Learn how ISO 14971 risk management applies to medical device cybersecurity - identify cyber hazards, control residual risk, and align with FDA expectations.
Read article
This article discusses the relationship between ISO 14971 and AAMI TIR57, and how they help address risks in the production and use of medical devices.
Read article
Updated April 15, 2025 Health Level 7 (HL7) is a vital cog in the machinery of healthcare information technology. It is the backbone for data exchange across various healthcare systems, facilitating improved patient care and efficient administration. However, the extensive adoption of HL7 also bring
Read article
This post covers the purposes, security risks, & regulatory guidance for medical device protocols for manufacturers, healthcare providers, & regulatory bodies.
Read article
Learn the 7 software testing principles and how to apply them to medical device software and cybersecurity - risk-based testing, evidence, and common pitfalls.
Read article
Discover the 10 ways cybercriminals monetize medical device breaches. Get expert advice from Blue Goat Cyber to protect patient data, safety, and compliance.
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.