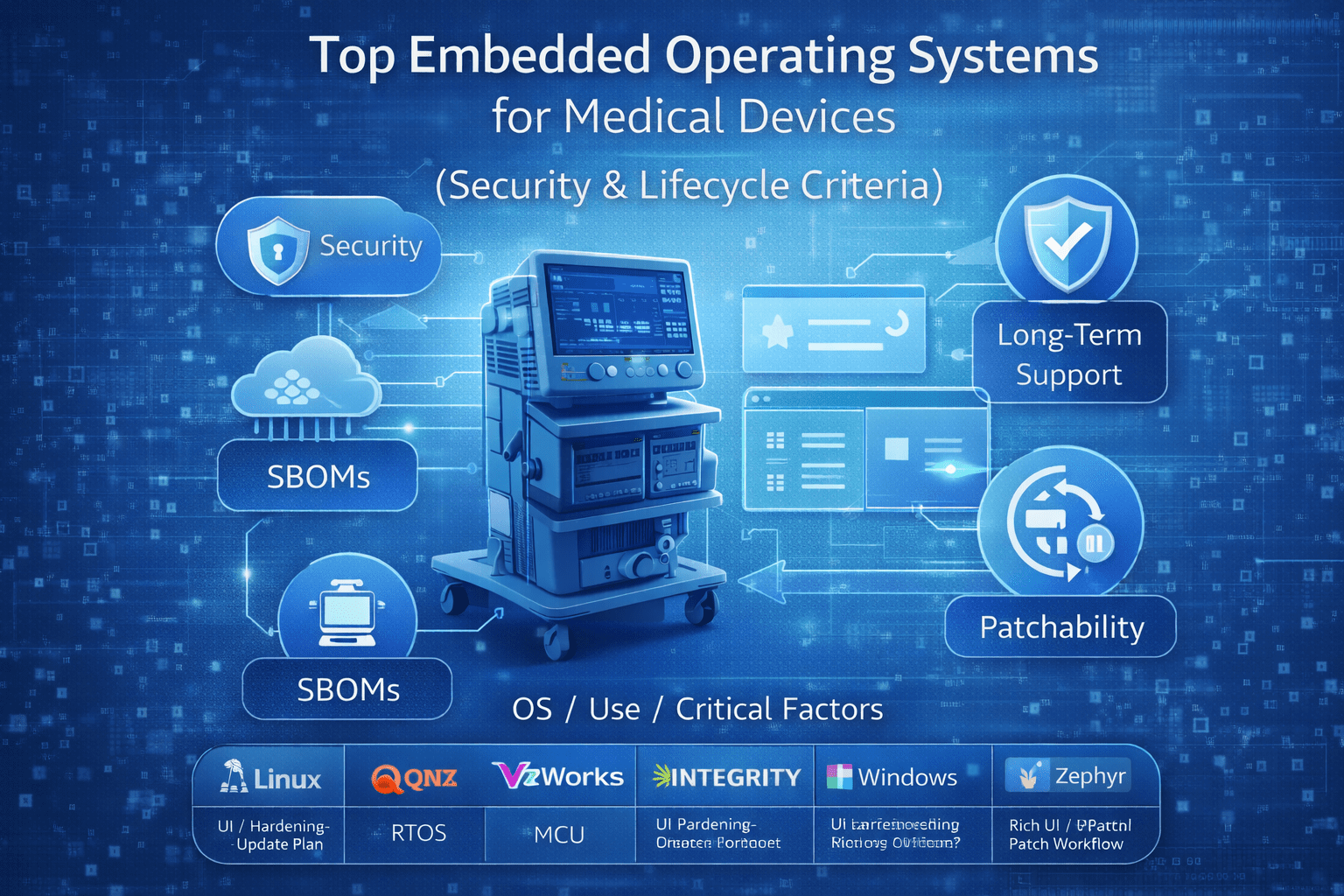
Top 10 Embedded Operating Systems for Medical Devices
Compare the top embedded OS options for medical devices using security, long-term support, and update readiness - so teams can choose and defend decisions.
Read articleDeep dives on FDA expectations, threat modeling, penetration testing, SDLC, and the standards your team is being asked to meet.
Showing 12 of 360 articles · Page 19 of 30
Compare the top embedded OS options for medical devices using security, long-term support, and update readiness - so teams can choose and defend decisions.
Read article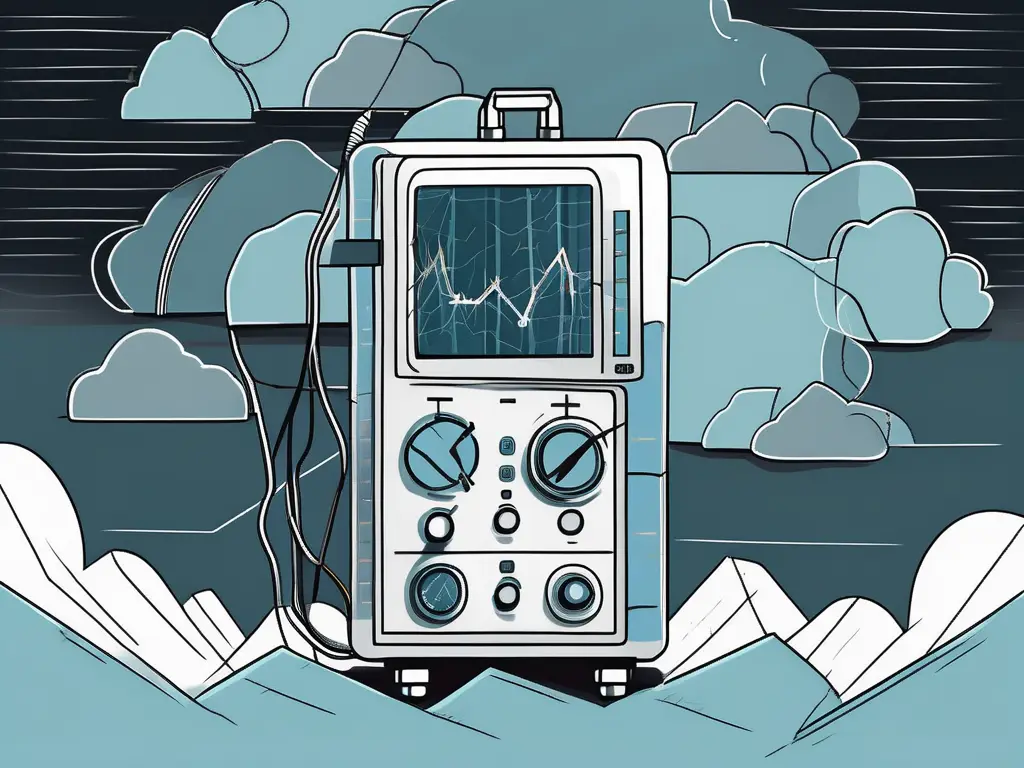
Uncover the potential dangers lurking within in vitro diagnostic (IVD) medical devices in this eye-opening article.
Read article
Insecure vs unsecure isn’t just grammar. Learn the difference and why precise wording matters for medical device cybersecurity docs and labeling. For FDA teams.
Read article
The “hoodie hacker” cliché distorts risk, weakens hiring, and misguides security decisions. Here’s what MedTech teams should do instead.
Read article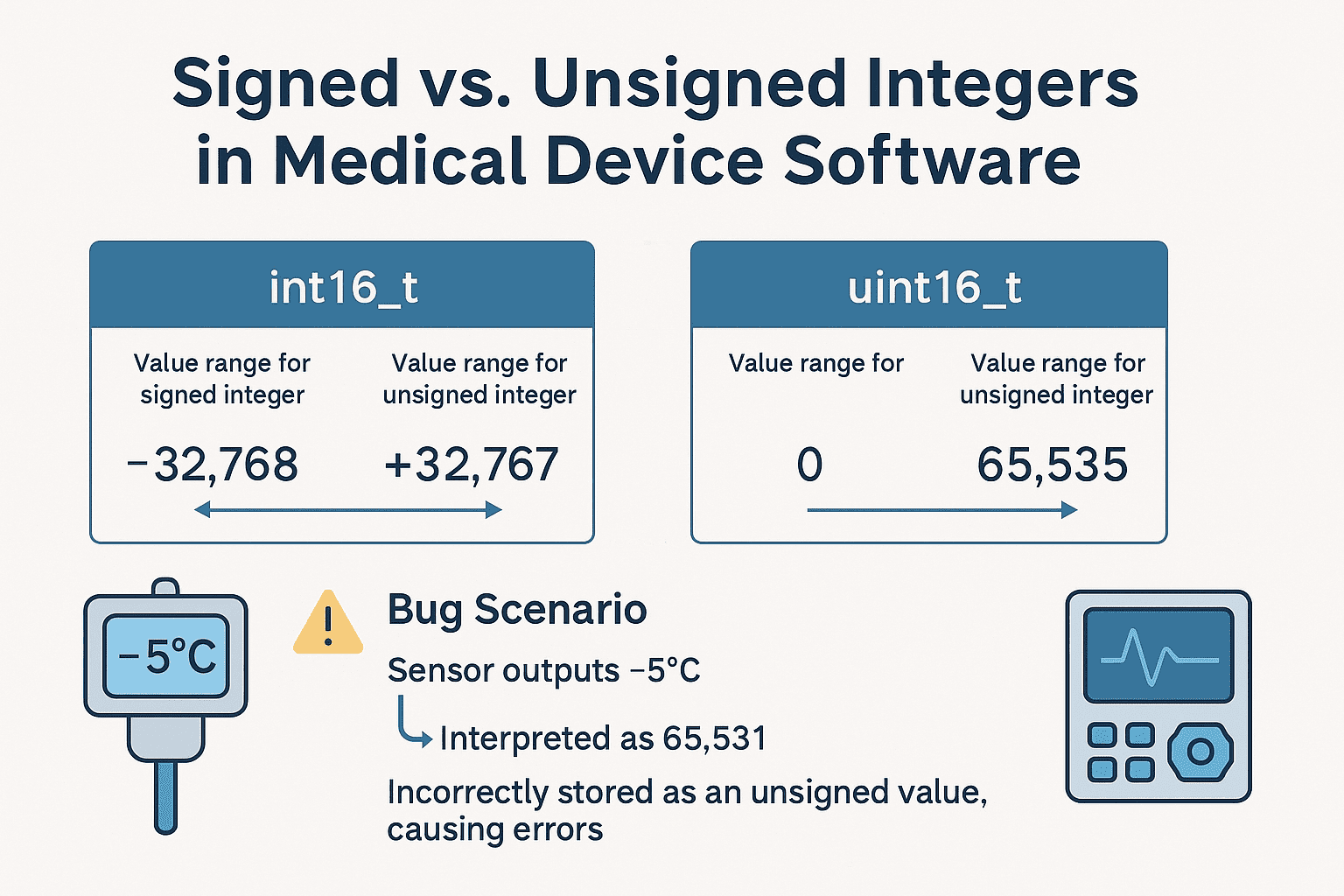
Explore the crucial disparities between unsigned and signed integers in this comprehensive article.
Read article
Discover how the FHIR Medical Device Protocol is revolutionizing cybersecurity in healthcare.
Read article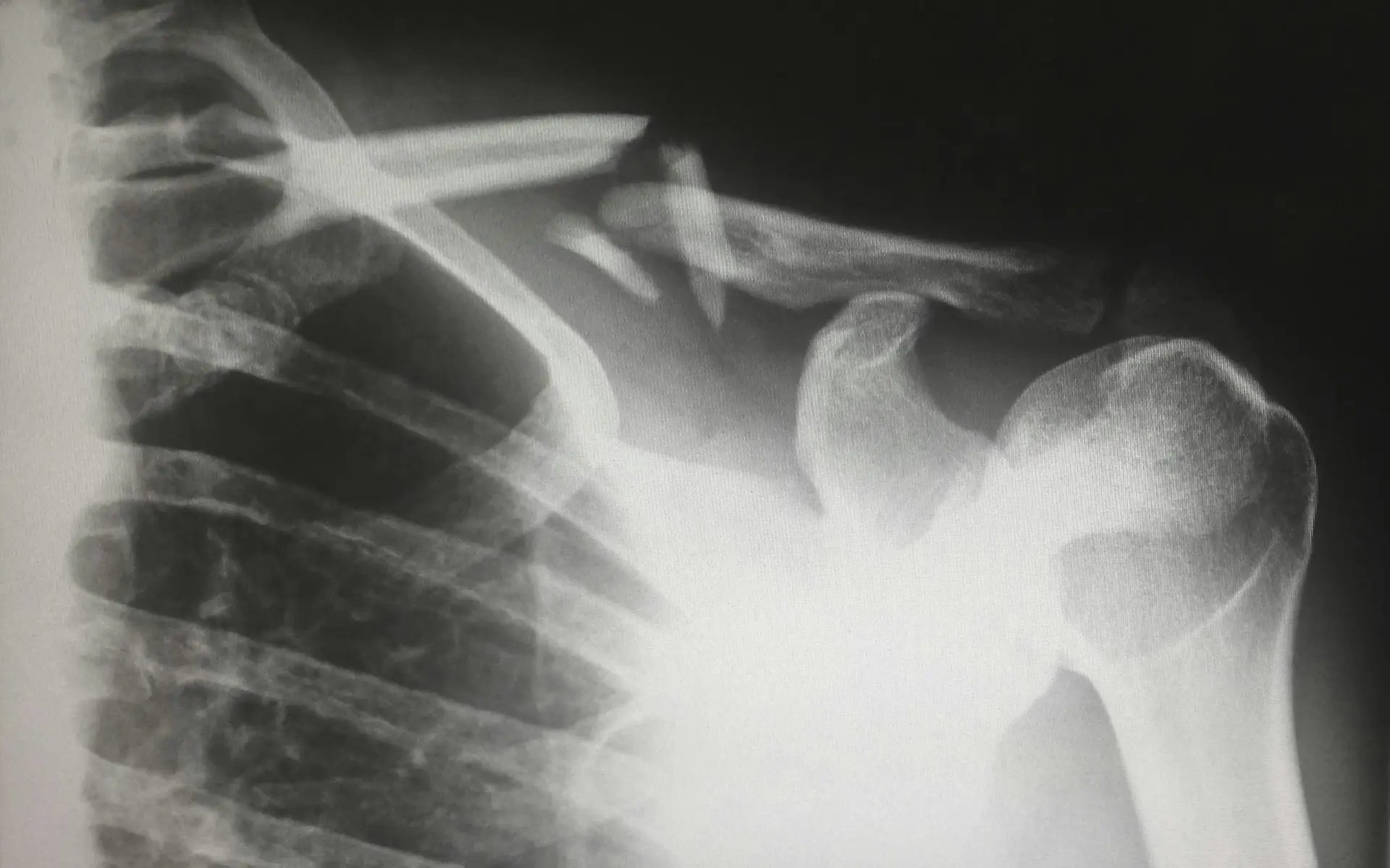
Digital Imaging and Communications in Medicine, or DICOM, is the industry standard for medical imaging formats. This format has expanded functionality compared to typical image formats, as it can store patient data and procedure information along with the actual image. Typically, a specialized DICOM
Read article
Discover the ins and outs of DICOM vulnerabilities in the MedTech industry with this comprehensive overview.
Read article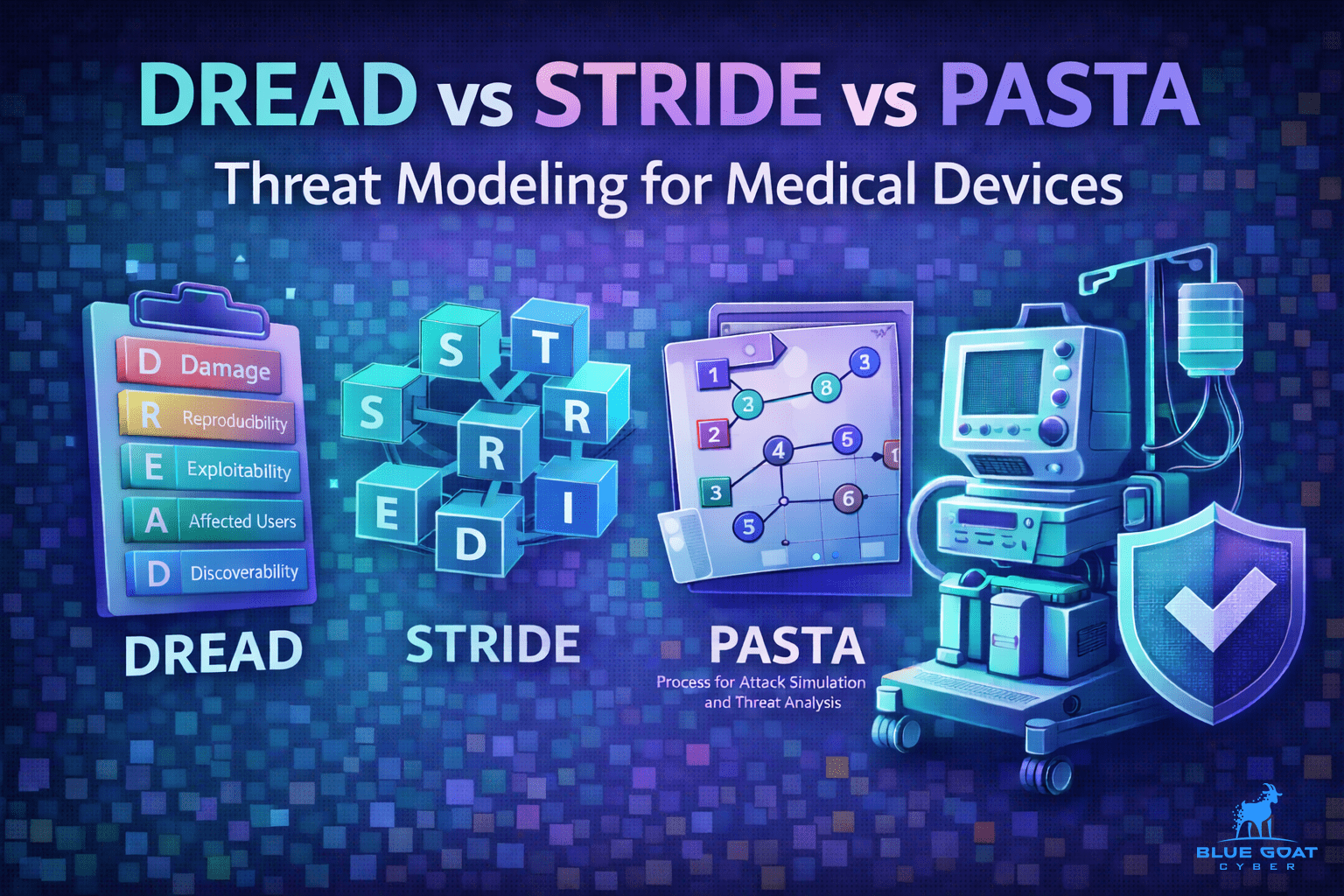
STRIDE is the preferred threat modeling baseline for medical device cybersecurity. Compare STRIDE, DREAD, and PASTA and when to use each.\
Read article
Can contact lenses fool iris scans? Learn how iris spoofing affects medical device cybersecurity, liveness detection, and FDA lifecycle expectations.
Read article
Learn how to identify and address vulnerabilities in PACS medical devices with our comprehensive guide.
Read article
Medical device cybersecurity doesn't require genius hackers - just neglected vulnerabilities. Discover how Blue Goat protects devices, patients, and compliance.
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.