Ephemeral Ports in Medical Device Cybersecurity (What to Know)
Ephemeral ports affect firewall rules, logging, and threat models for connected medical devices. Learn ranges, risks, and practical controls.
Read articleDeep dives on FDA expectations, threat modeling, penetration testing, SDLC, and the standards your team is being asked to meet.
Showing 12 of 360 articles · Page 20 of 30
Ephemeral ports affect firewall rules, logging, and threat models for connected medical devices. Learn ranges, risks, and practical controls.
Read article
Discover the potential risks and implications of LoRaWan vulnerabilities on the cybersecurity of medical devices.
Read article
Discover the crucial role of RFID technology in safeguarding medical devices from cyber threats.
Read article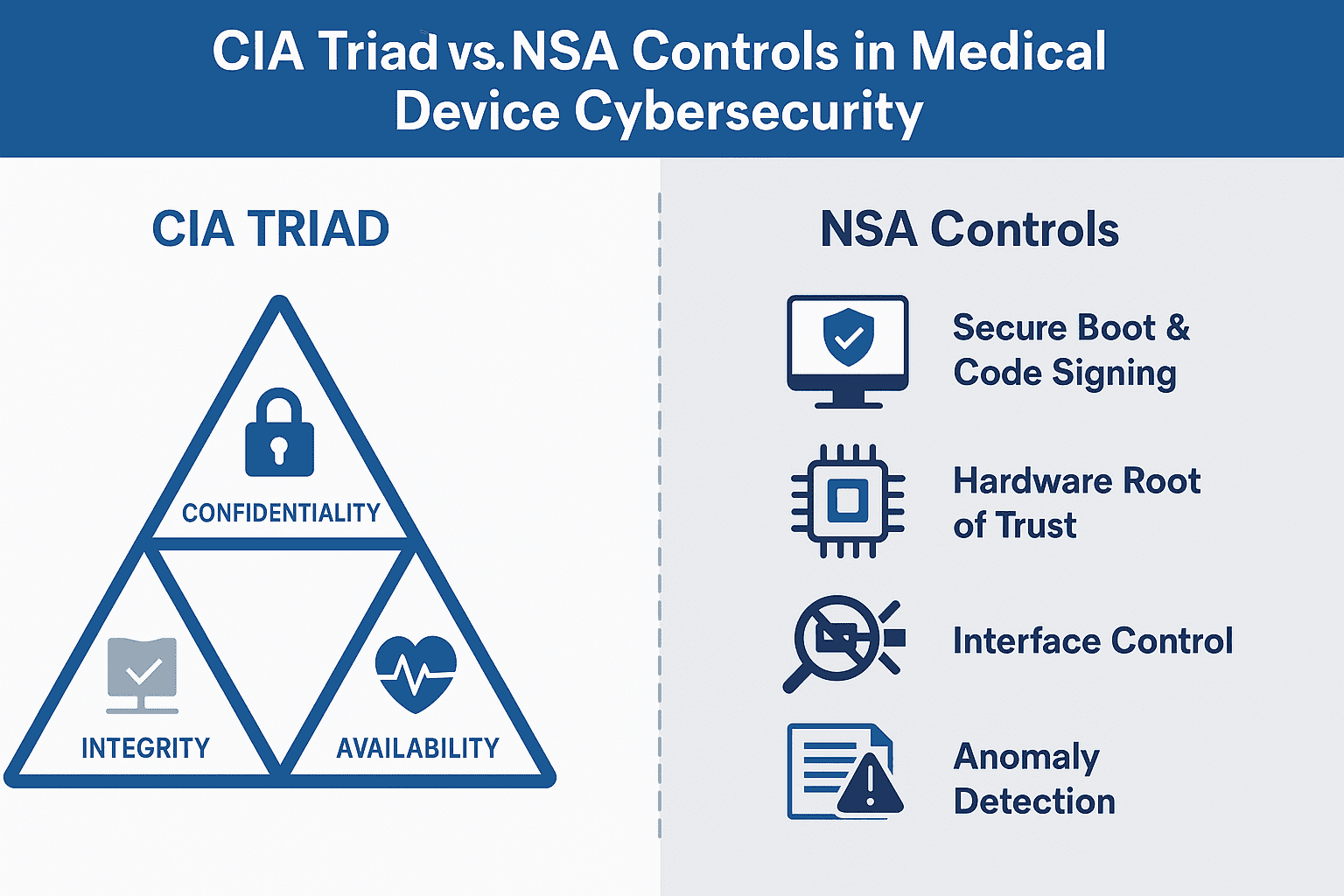
Explore how the CIA Triad and NSA cybersecurity controls strengthen medical device security and support FDA compliance from design to postmarket.
Read article
Learn how symmetric encryption works in medical devices, where AES fits, and what strong key management looks like for FDA-ready cybersecurity documentation.
Read article
Replay attacks are a core threat to BLE and MICS-enabled medical devices. How MedTech manufacturers detect and prevent replay in wireless protocols.
Read article
How MedTech teams should identify, triage, and document VxWorks RTOS vulnerabilities (URGENT/11 and beyond) for FDA Section 524B premarket and postmarket submissions.
Read article
Discover the Electronic Frontier Foundation (EFF) and its role in protecting digital rights and privacy.
Read article
Learn why medical device vulnerability testing is crucial for patient safety and data security.
Read article
Delve into the fascinating world of self-aware AI as we explore the concept, implications, and potential of artificial intelligence that possesses self-awareness.
Read article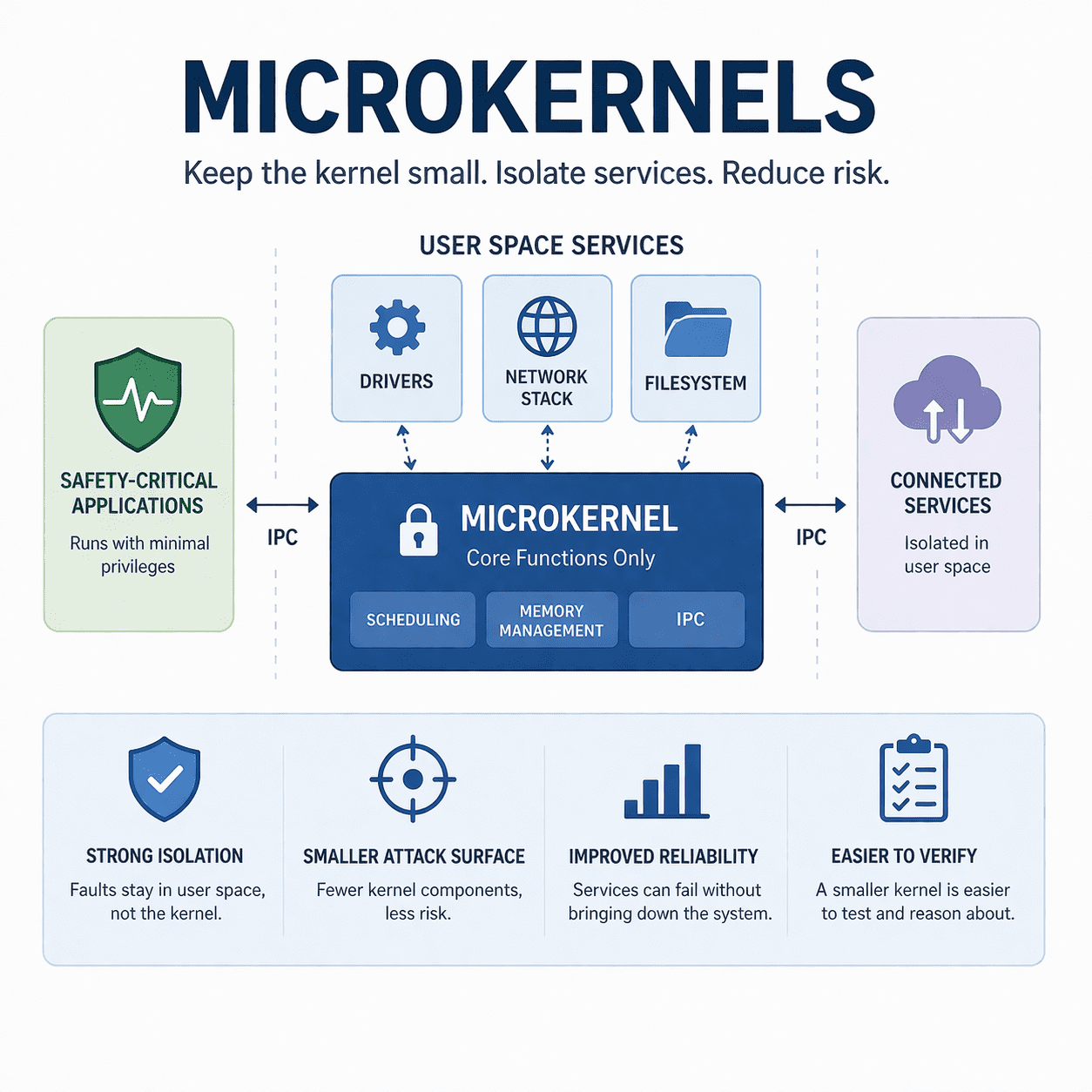
Microkernels can improve isolation and reduce trusted code in medical devices. Learn real tradeoffs, design patterns, and FDA-friendly evidence ideas.
Read article
Learn how brute force, side-channel, and cryptanalysis attacks compromise encryption in medical devices - and how to secure your product before FDA submission.
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.