
Hardware Hacking Tools for Medical Device Cybersecurity Testing
A practical, authorized toolkit for medical device hardware security testing - RFID, SDR, Wi-Fi, HID, and lab essentials - plus FAQs.
Read articleDeep dives on FDA expectations, threat modeling, penetration testing, SDLC, and the standards your team is being asked to meet.
Showing 12 of 360 articles · Page 24 of 30

A practical, authorized toolkit for medical device hardware security testing - RFID, SDR, Wi-Fi, HID, and lab essentials - plus FAQs.
Read article
Updated October 26, 2024 One of the hardest parts of the security process is the initial discovery phase of understanding what could go wrong. Cyber threats are constantly changing, with old attacks slowly becoming less common while new attacks rapidly pop up. Modern attack techniques target new tec
Read article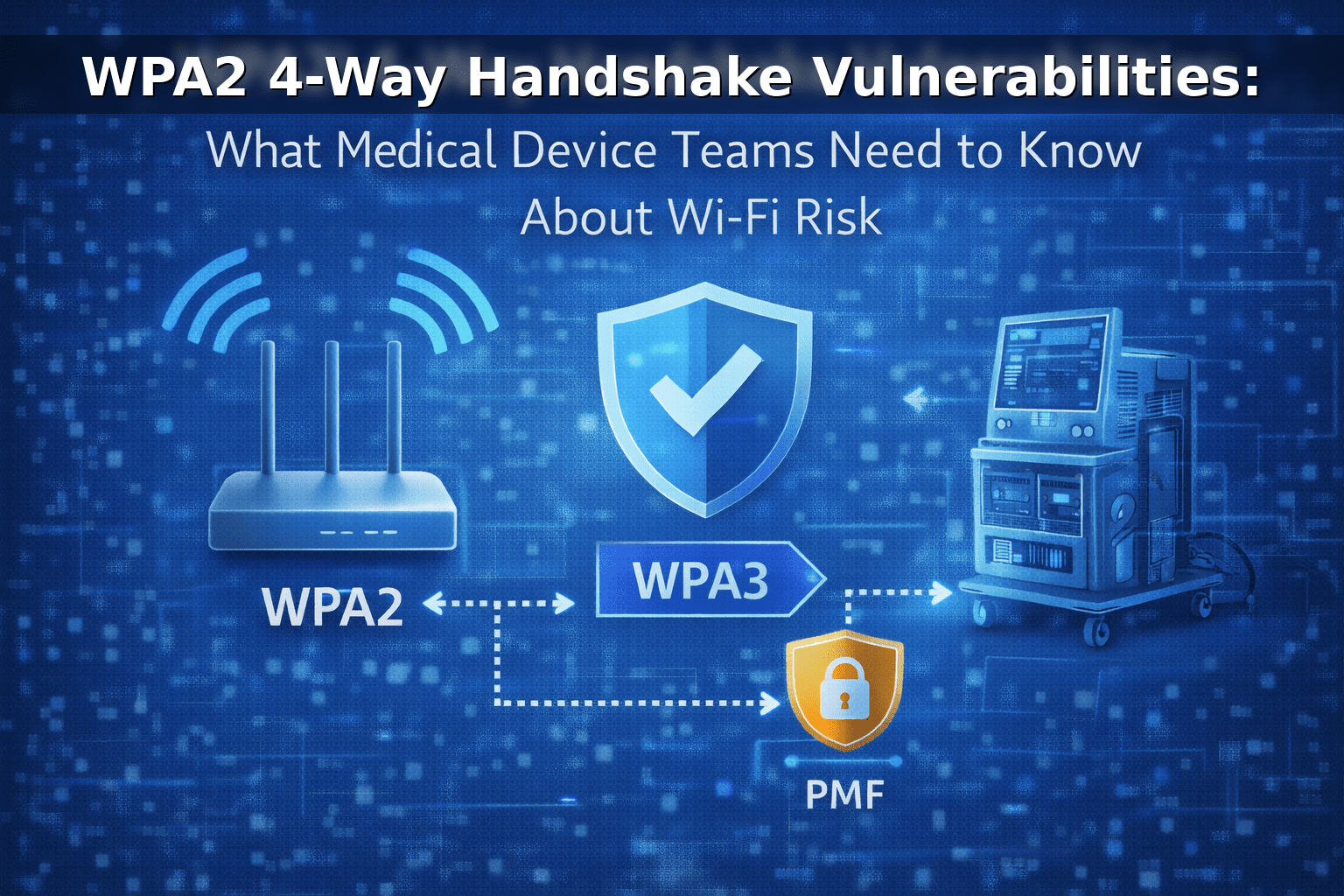
Understand WPA2’s 4-way handshake, real risks like KRACK and weak passphrases, and practical mitigations for connected medical device Wi-Fi ecosystems.
Read article
Learn how SUID attacks enable privilege escalation on Linux-based medical devices and how to prevent them with hardening, monitoring, and testing.
Read article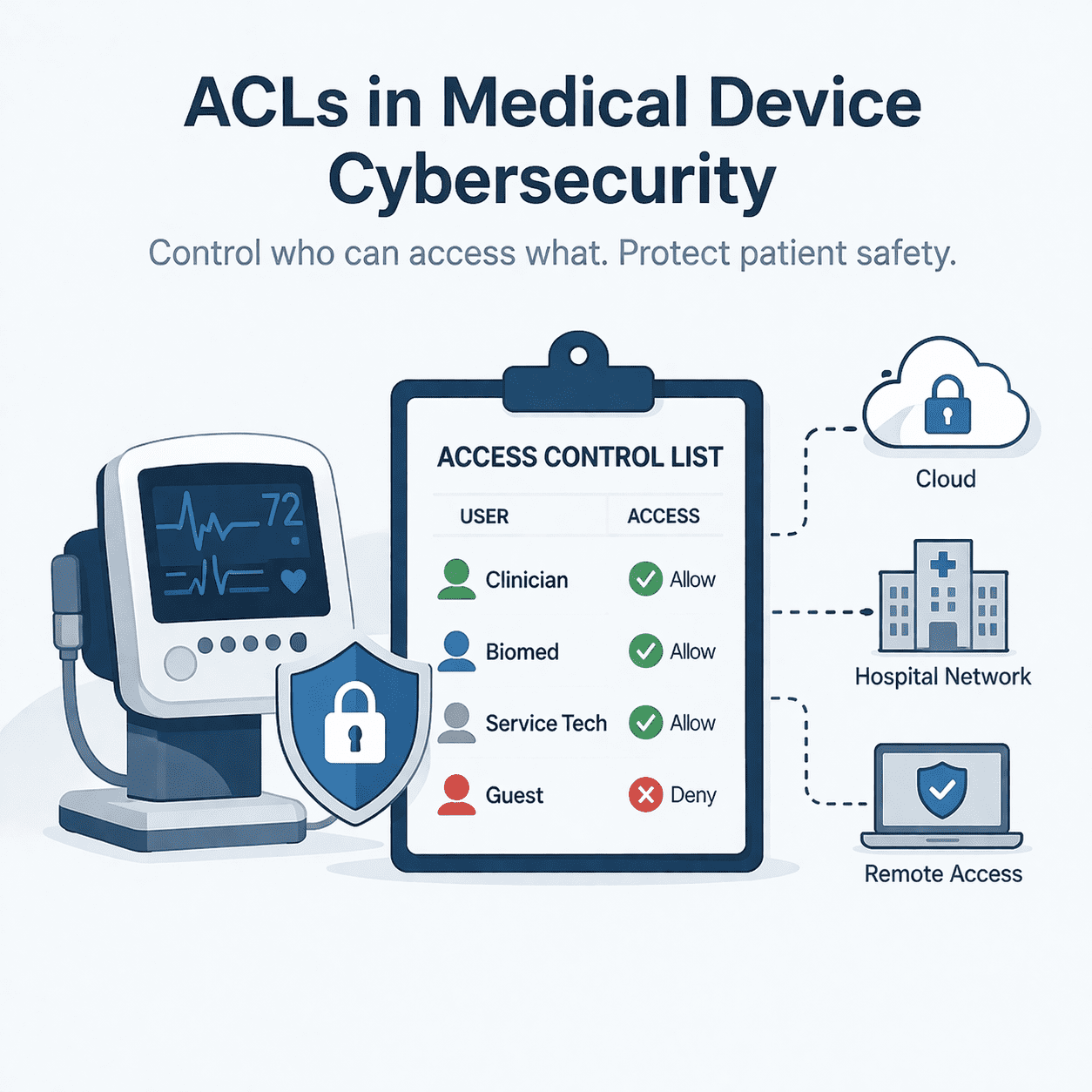
Use ACLs to enforce least privilege across device, cloud, and hospital networks - and produce FDA 524B-ready cybersecurity evidence.
Read article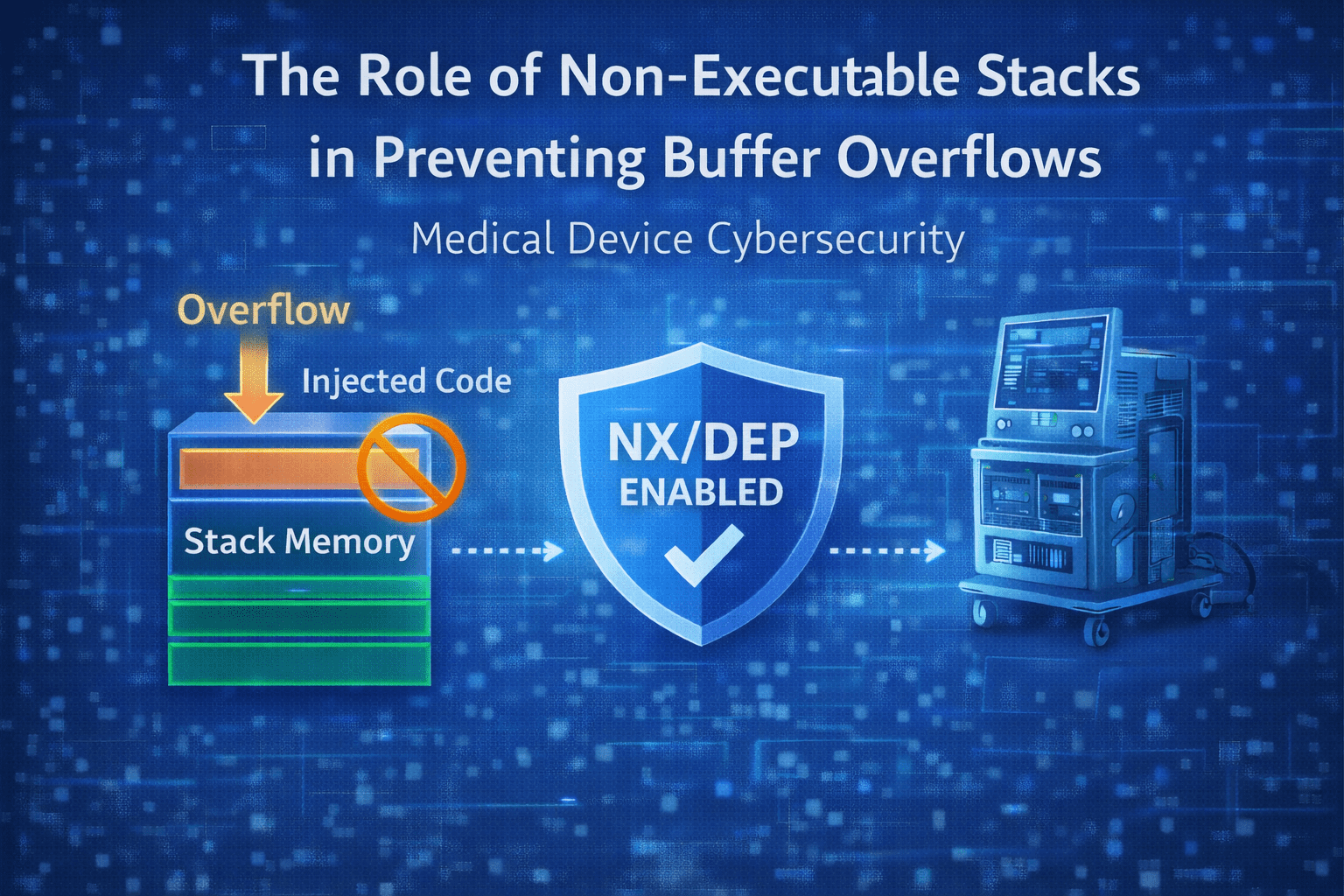
Learn how non-executable stacks (NX/DEP) reduce buffer overflow risk in medical device software, plus practical implementation and verification guidance.
Read article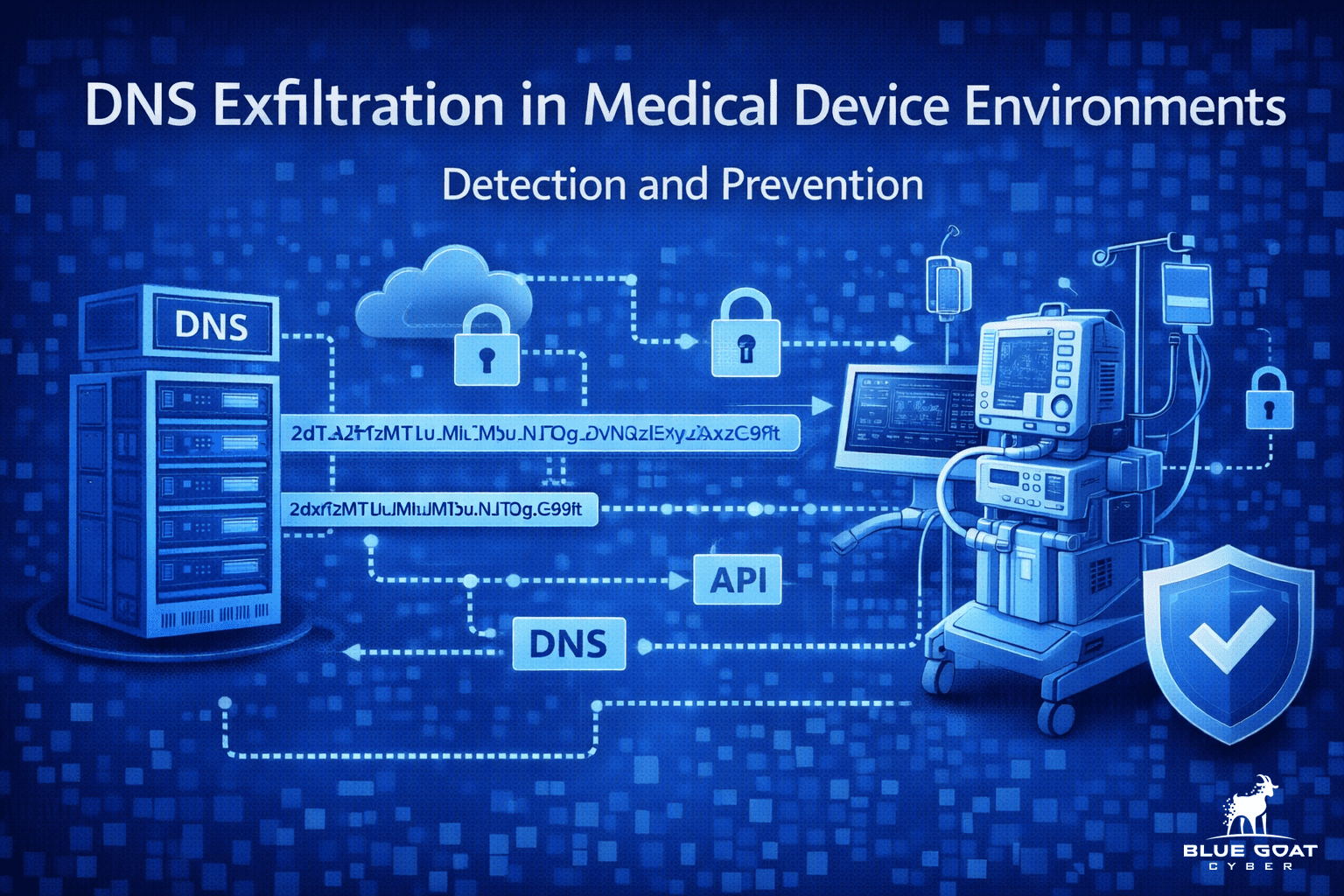
DNS exfiltration can bypass controls by hiding data in DNS queries. Learn detection signals and mitigations for medical device and healthcare networks.
Read article
Explore how the Medical Device Single Audit Program (MDSAP) streamlines international compliance for medical devices.
Read article
Discover how the International Medical Device Regulators Forum (IMDRF) is working towards harmonizing global regulations for medical devices.
Read article
What is an IMEI and why it matters for cellular-connected medical devices: inventory, incident response, lost/stolen playbooks, and common pitfalls.
Read article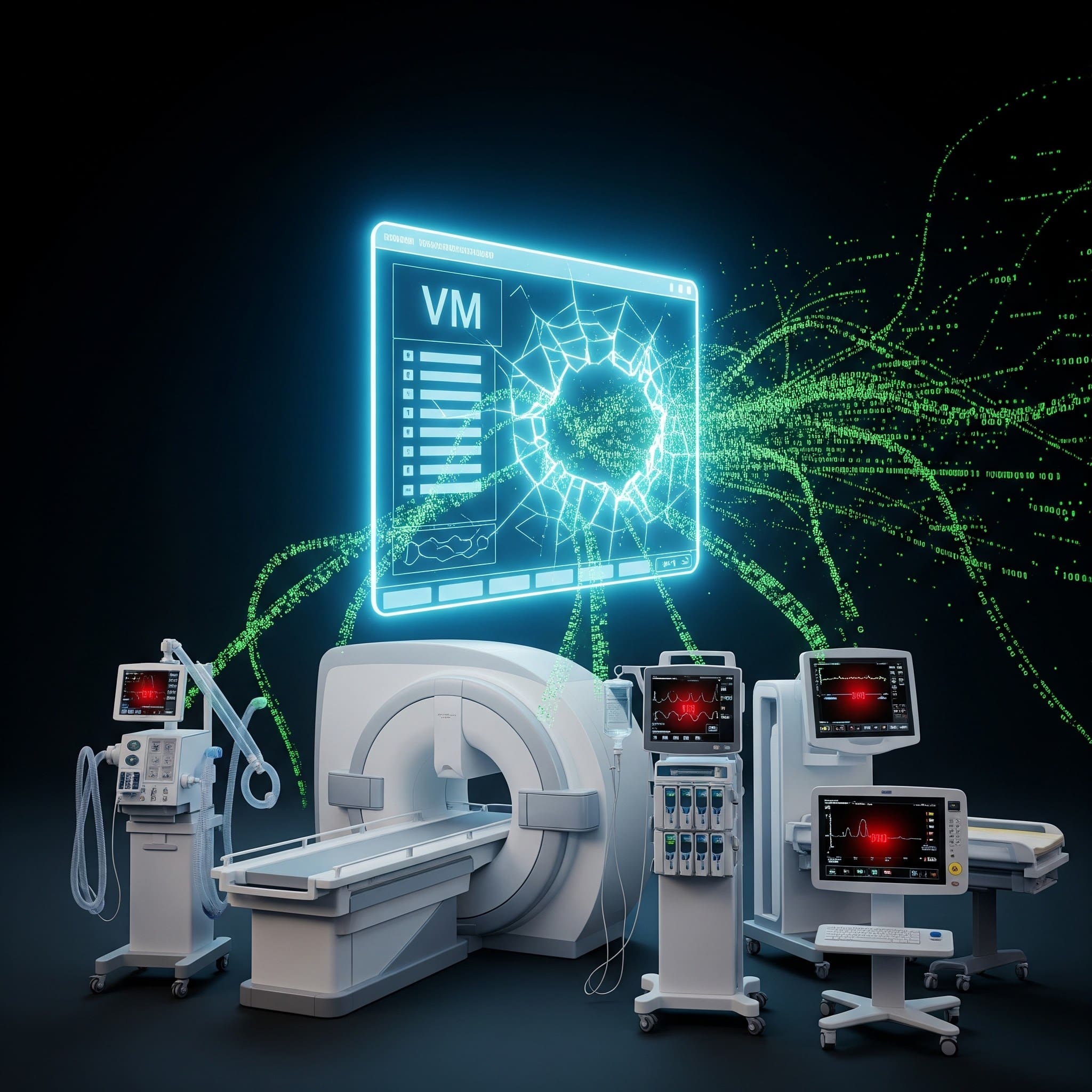
VM escape breaks VM isolation to reach the host or hypervisor. Learn MedTech scenarios, controls, and evidence for FDA-aligned security.
Read article
Learn what post-exploitation frameworks (like Empire) mean for medical device cybersecurity - plus detection priorities, controls, and testing guidance.
Read article30-minute strategy session. No cost, no commitment - just answers from people who've shipped 250+ submissions.